Information-disclosure-free two-way quantum secure direct communication protocol based on Bell state and control-not-operation
A technology for secure direct communication and information leakage, applied in the field of quantum secure communication
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
preparation example Construction
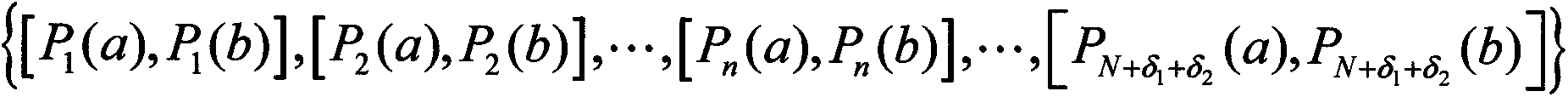
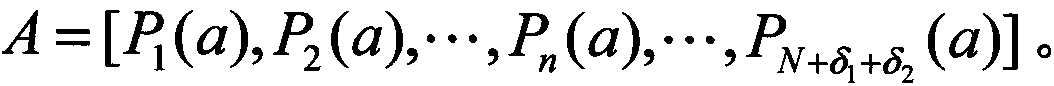
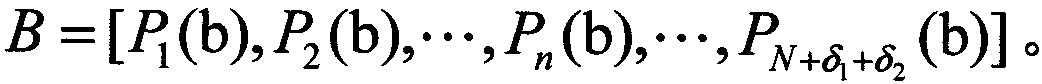
[0052] S1) Preparation of Bell state: Alice prepares N+δ 1 +δ 2 EPR pairs randomly in one of the four Bell states, where N EPR pairs are used for secret information transmission, δ 1 +δ 2 An EPR pair is used for security testing. { [ P 1 ( a ) , P 1 ( b ) ] , [ P 2 ( a ) , P 2 ( b ) ] , . . . , [ P n ( a ) , P n ( b ) ] , ...
Embodiment
[0061] 1. Application example of two-way quantum secure direct communication protocol
[0062] An example is given here to further explain the protocol of the present invention. Assume that the first Bell state prepared by Alice is And suppose Alice and Bob use this Bell state to send bits "10" and "01" to each other respectively. in possession of particle a 1 and b 1 Afterwards, Bob's implement control non-operations (in the form of a 1 To control the qubit, take b 1 is the target qubit). so, Will evolve as follows:
[0063] C C - Not ⊗ | φ + > a 1 b 1 = 2 | + > a 1 | 0 ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More