Cloud storage data audit method against key leakage
A data audit and cloud storage technology, applied in the field of cloud computing security, can solve the problems of system audit security loss, inability to resist key leakage, and low user security awareness, so as to improve storage efficiency and audit performance, reduce the number of tags, The effect of reducing the burden on oneself
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
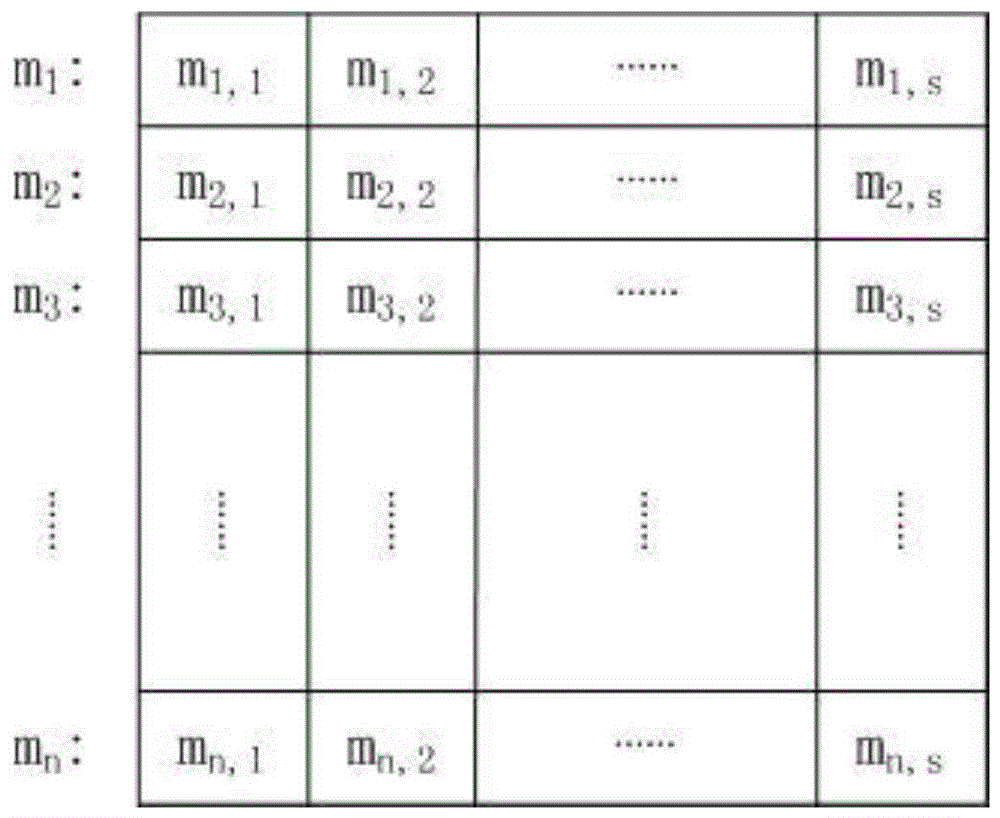
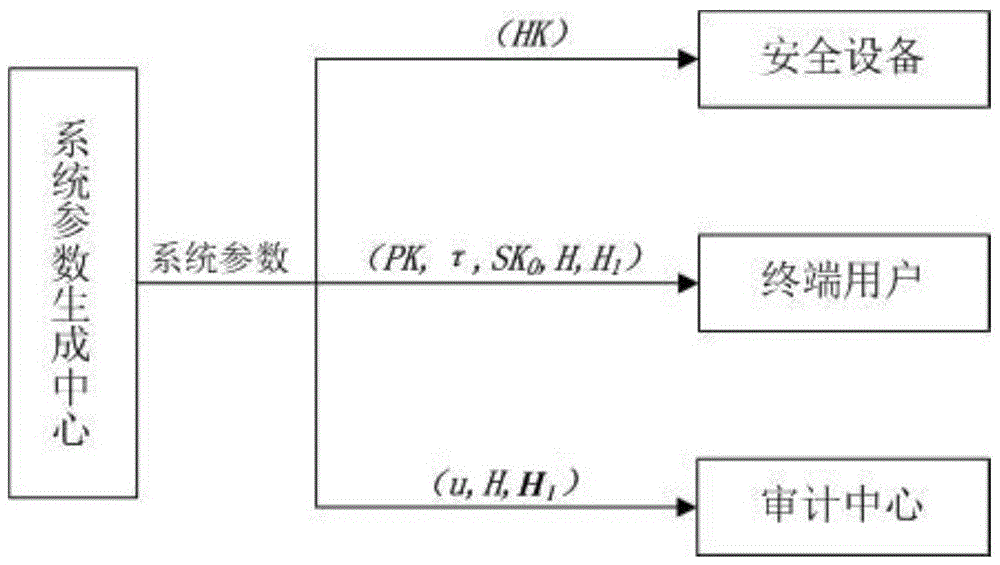
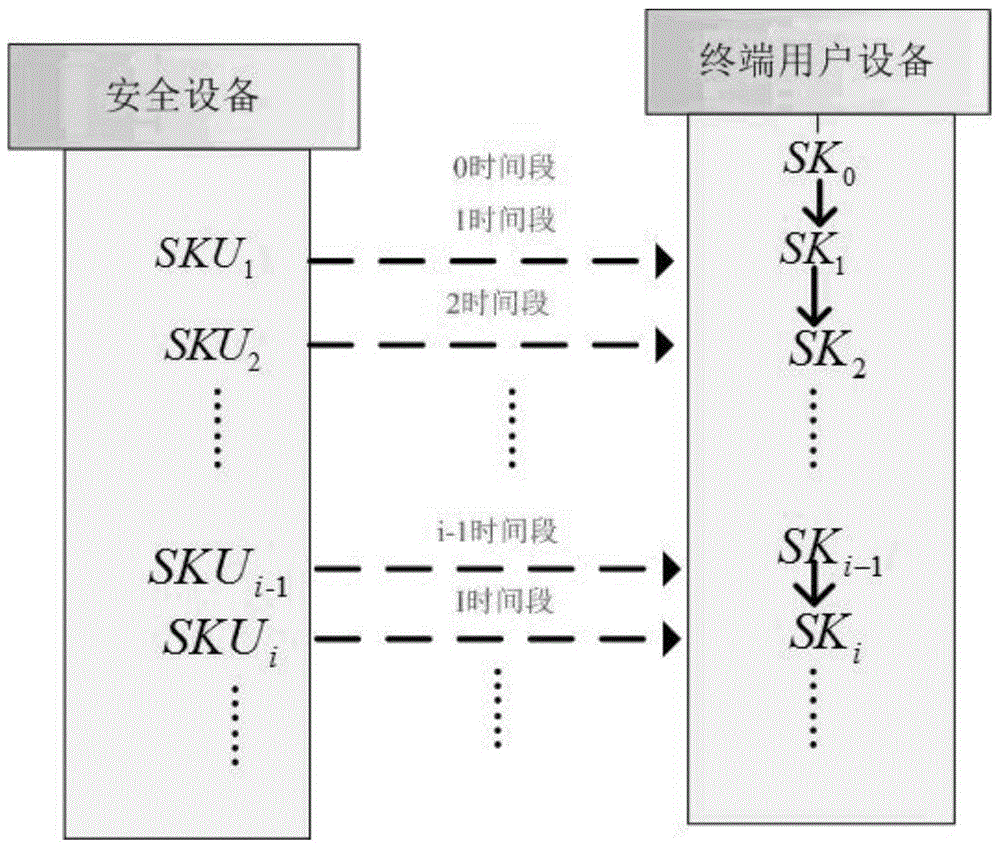
[0030] The members of the system used in the cloud storage data audit method that can resist key leakage provided by this patent include a system parameter generation center, a cloud, end users, security equipment, and an audit center. Among them, the system parameter generation center generates various system parameters, generates public and private keys for users, selects device private keys for security devices, calculates audit parameters, etc.; the cloud provides storage resources for user data; a large amount of data of end users must be outsourced to the cloud; security The device assists the user to periodically update the key; the audit center verifies the data integrity on behalf of the user.
[0031] The following examples are used to describe the implementation of the present invention in detail, so as to fully understand and implement the process of how to apply technical means to solve technical problems and achieve technical effects in the present invention.
[00...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More