A spam feature selection method and its detection method
A feature selection method and spam technology, applied in special data processing applications, instruments, electronic digital data processing, etc., can solve the problems of time-consuming, difficult results, and high computational complexity, reducing feature dimensions and wide application. Effect
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0058] The specific implementation manners of the present invention will be further described in detail below in conjunction with the accompanying drawings and embodiments. The following examples are used to illustrate the present invention, but are not intended to limit the scope of the present invention.
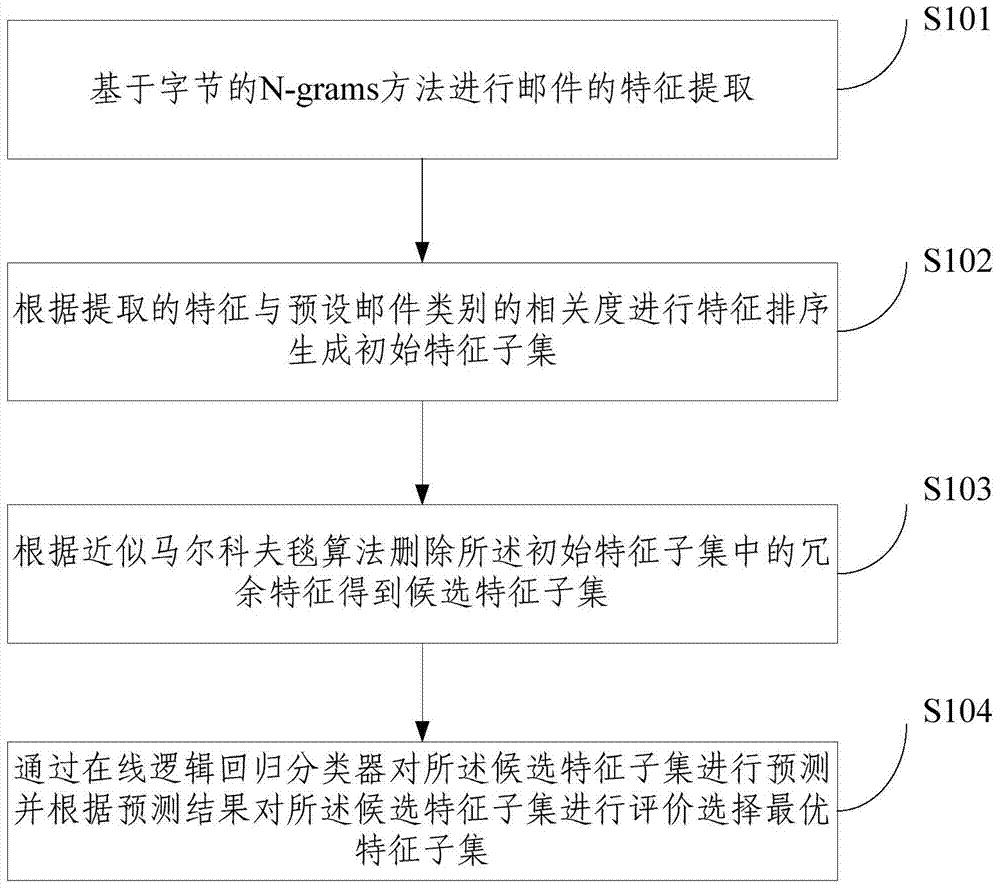
[0059] The present invention proposes a feature selection method of spam, such as figure 1 shown, including the following steps:
[0060] S101 extracting the features of the email based on the N-grams method of bytes, specifically including: segmenting the email into bytes of a preset length according to the byte stream to obtain the hash dictionary of the email; combining the preset samples with the hash dictionary Perform feature comparison to obtain a feature set corresponding to the hash dictionary;
[0061] Wherein, comparing the features of the preset sample with the hash dictionary to obtain the feature set corresponding to the hash dictionary is specifically: whe...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More