An electronic document trust and security control method and system
An electronic document and security control technology, applied in computer security devices, electronic digital data processing, instruments, etc., can solve the problems of accidental loss, external information security threats, illegal data diffusion, etc., and achieve the effect of preventing illegal diffusion.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
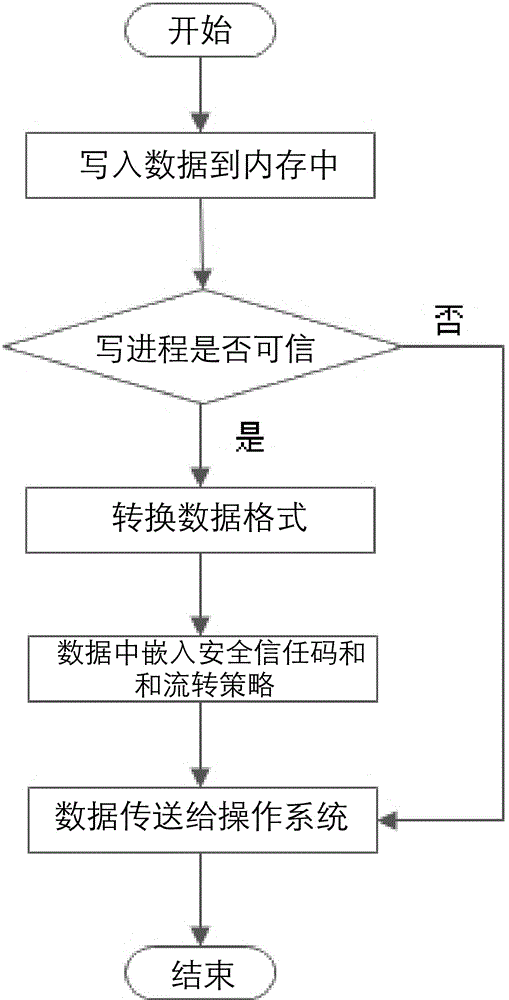
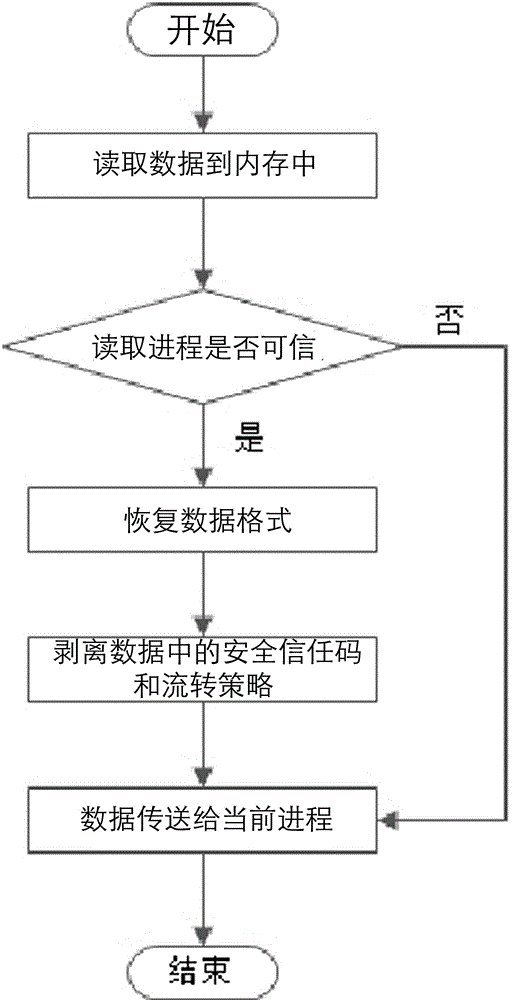
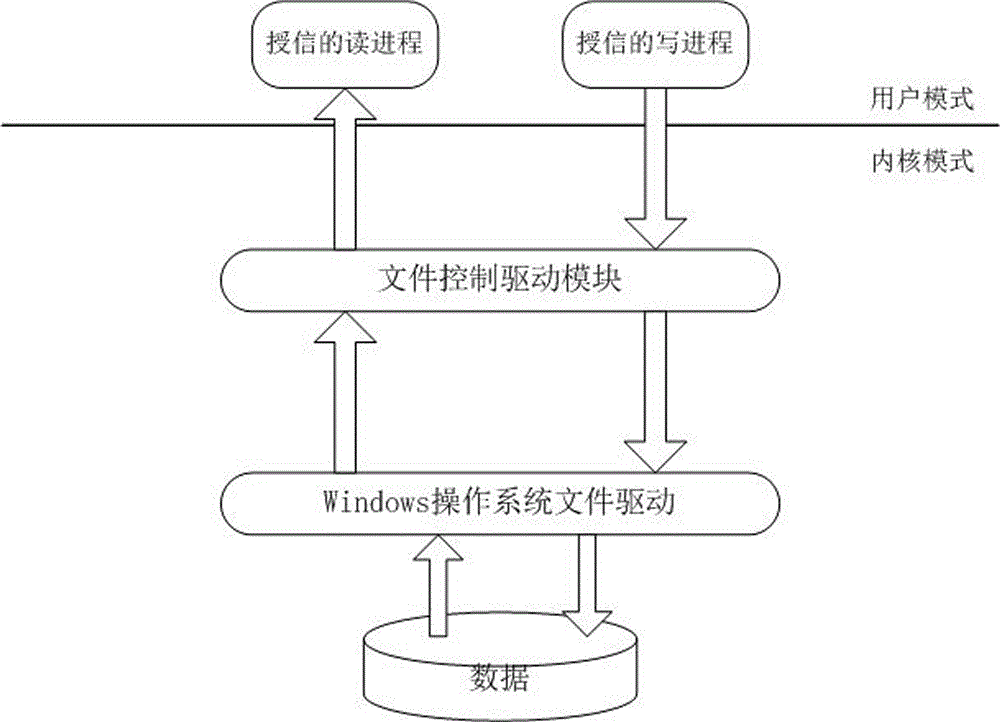
[0035] The present invention will be described in further detail below in conjunction with the accompanying drawings and specific embodiments.
[0036] An electronic document trust and security control method, which includes server-side credit granting to client-side, security isolation, circulation control and de-isolation, wherein the server-side credit granting to client-side includes the following steps:
[0037] A. The client connects to the server, queries the security trust management and control information of the unit where it is located, and forms a computer terminal security trust code. The computer terminal security trust code is composed of a unit trust code, a department trust code and a trust serial number;
[0038] B. The client uses the computer terminal security trust code to initiate a security trust code registration to the server, and waits for the server to grant credit;
[0039] C. The server assigns a new security trust code and control strategy to the ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More