Terminal application protecting method and device
A terminal application and protection device technology, applied in computer security devices, program/content distribution protection, instruments, etc., can solve the problem of high threshold, achieve the effect of preventing tampering and reducing the embedding of malicious advertisements
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0044] The present invention will be further described in detail below in conjunction with the accompanying drawings and specific embodiments.
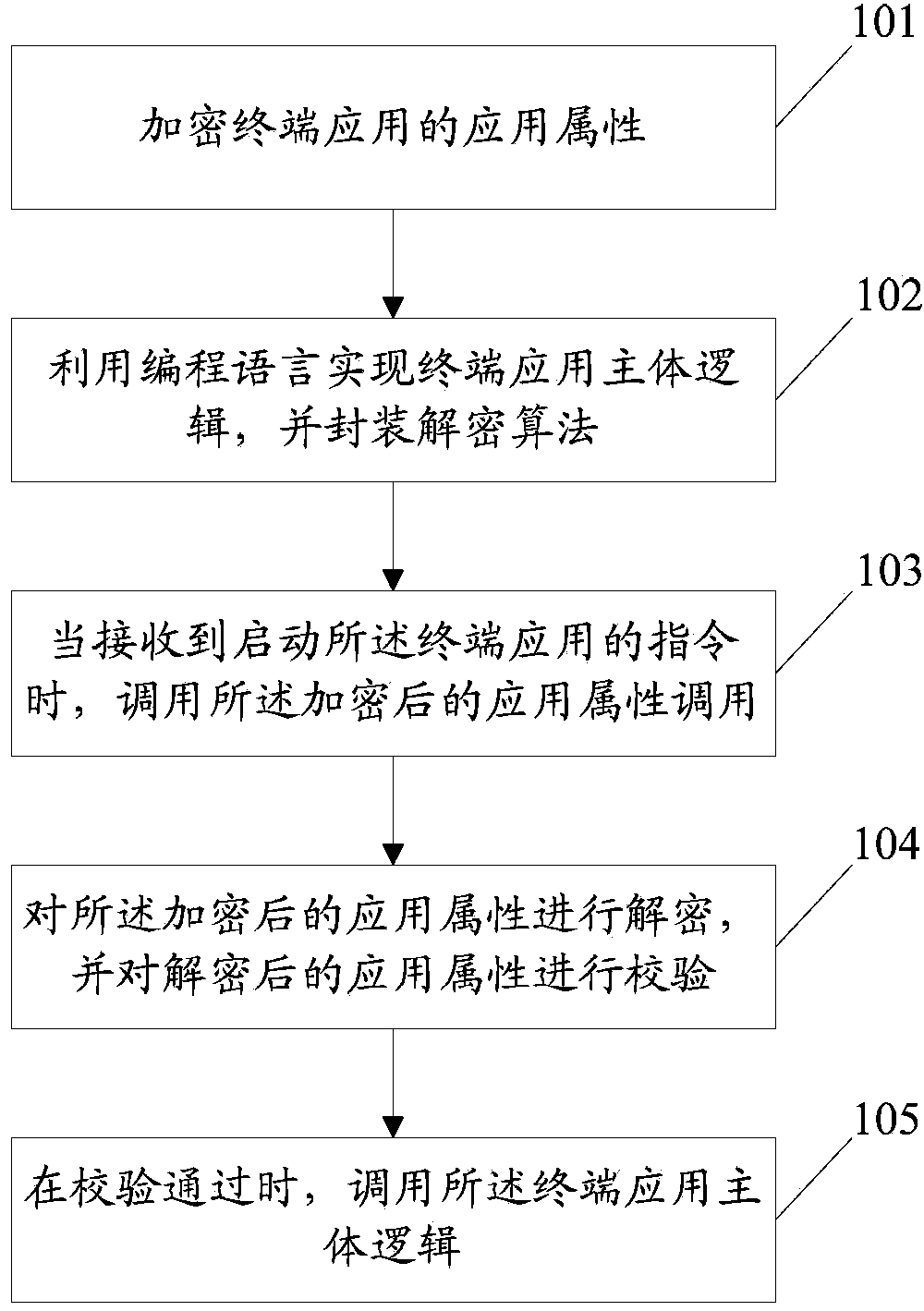
[0045] figure 1 It is a schematic flowchart of an embodiment of a protection method for a terminal application of the present invention, such as figure 1 shown, including the following steps:
[0046] Step 101: encrypting the application attributes of the terminal application;
[0047] Here, the application attribute of the terminal application is encrypted at the display layer, and the display layer is a decompilable layer, which may be a JAVA layer in the present invention;
[0048] Wherein, the application attribute includes an application package name, or a combination of an application package name and a digital signature.
[0049] The application attributes of the encryption terminal application specifically include:
[0050] The application package name of the terminal application is obtained, the application package name i...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More