Composite dynamic password authentication method and authentication system applicable to plug-and-play terminal
A dynamic password, plug-and-play technology, applied in transmission systems, digital transmission systems, user identity/authority verification, etc. The effect of defensive attacks
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0034]In order to make the object, technical solution and advantages of the present invention clearer, the present invention will be further described in detail below in conjunction with the accompanying drawings and embodiments. It should be understood that the specific embodiments described here are only used to explain the present invention, not to limit the present invention. In addition, the technical features involved in the various embodiments of the present invention described below can be combined with each other as long as they do not constitute a conflict with each other.
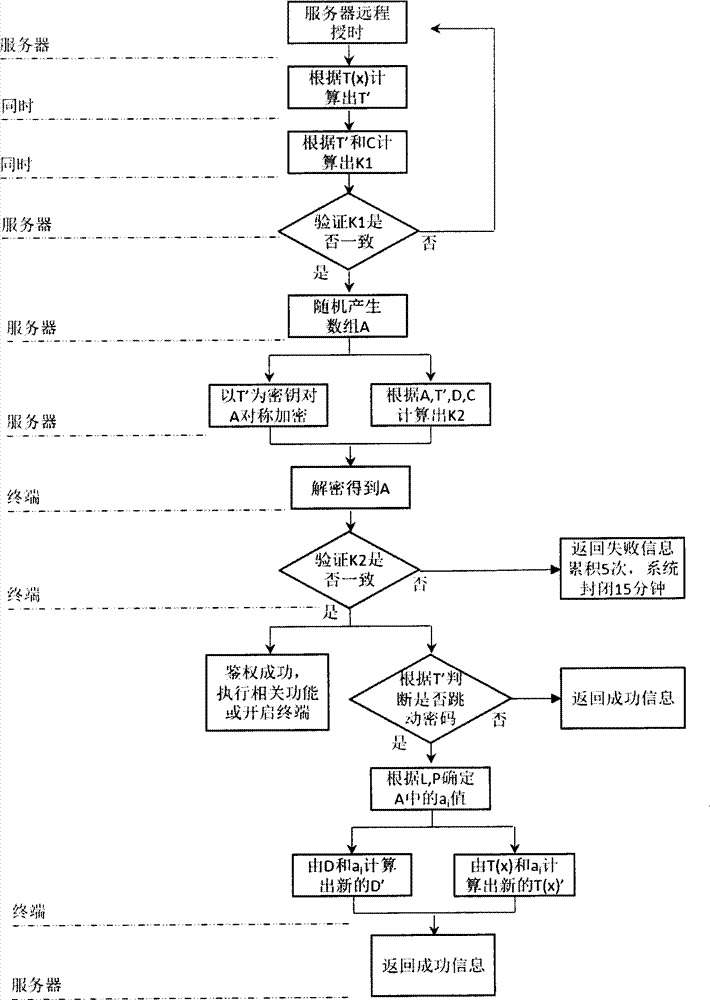
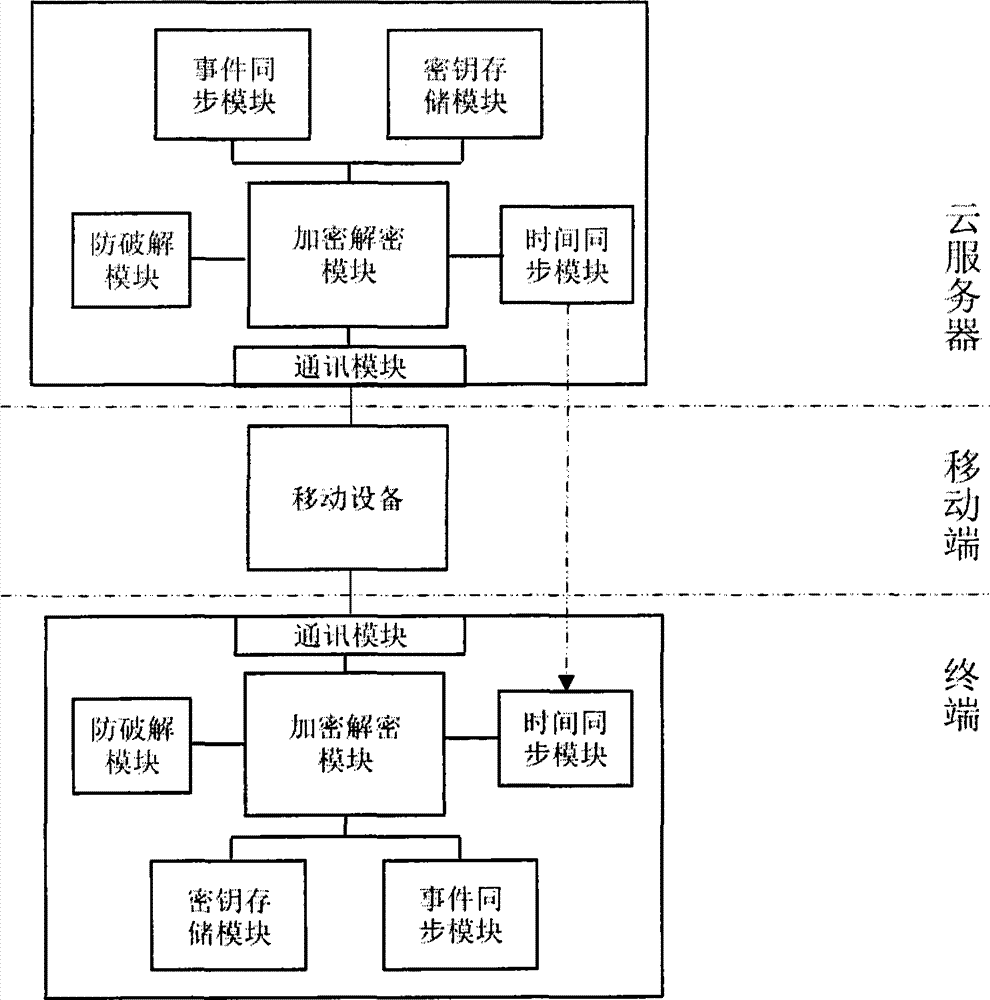
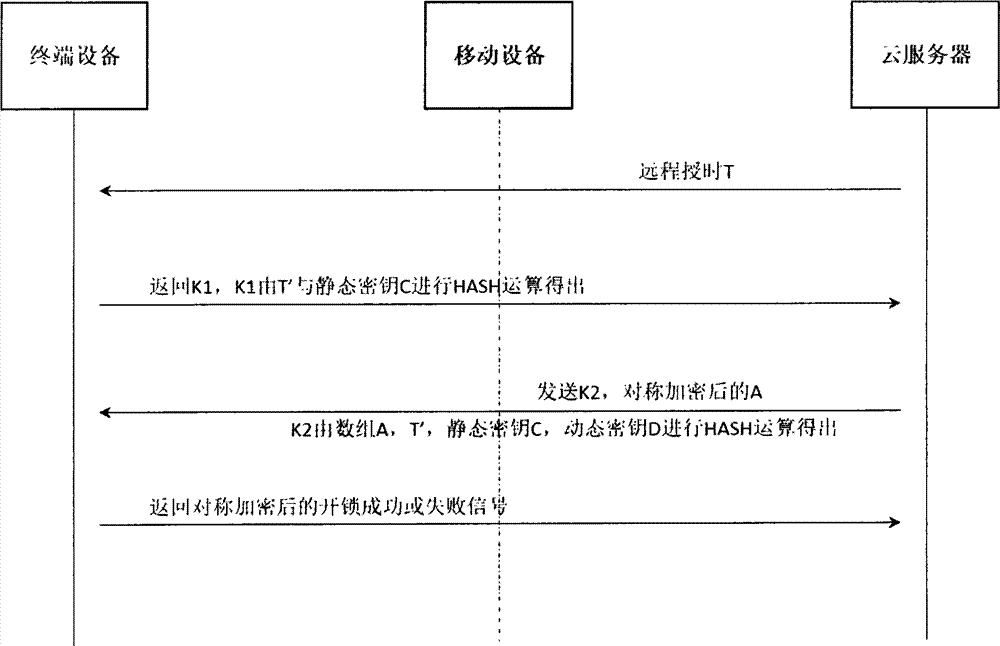
[0035] Such as figure 1 , figure 2 As shown, the system consists of three parts: server, mobile, and terminal. The server and terminal also include the same encryption and decryption module, time synchronization module, event synchronization module, communication module, and key storage module. Among them, the key module stores a static key C and a dynamic key D; the encryption and decryption ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More