Verification method for own integrity of software system
A technology of software system and verification method, applied in the field of computer security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0016] In order to make the purpose, technical solution and advantages of the present invention clearer, the present invention will be further described in detail below in conjunction with the accompanying drawings.
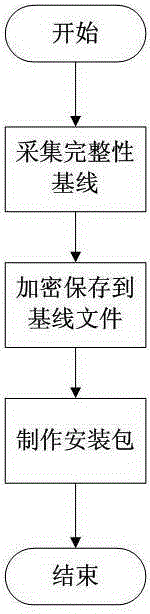
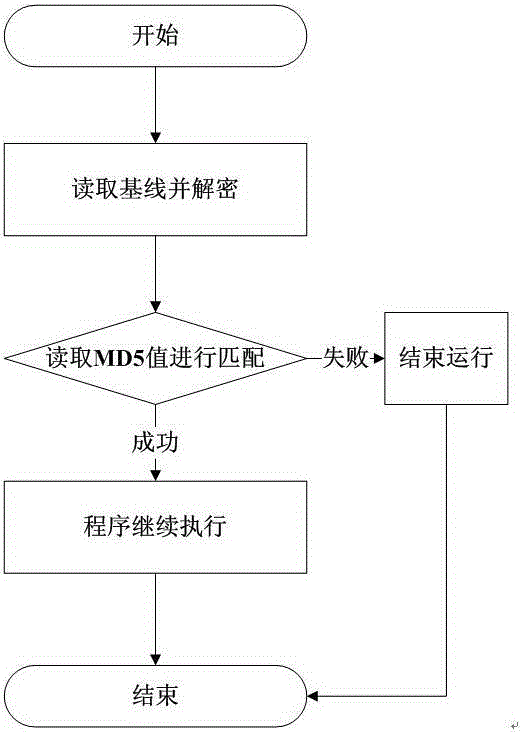
[0017] The present invention has two core processing flows, 1. the baseline collection of the integrity of the software system itself; 2. the integrity detection of the software system itself.
[0018] First of all, the integrity baseline collection of the software system itself requires the software system to perform baseline collection on all important files of the software system before launching. The integrity baseline collection includes two elements [file name] and [MD5 value]. The baseline of all files should be encrypted and saved As an encrypted file, this file will be installed on the user's machine along with the software as an integral part of the software system. Such as: attached figure 1 The flow chart of the software system's own integrity baseli...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More