Safe data transmission method
A transmission method and data security technology, applied in the field of data security transmission, can solve the problems of threatening the property safety of the lost person, leaking the personal privacy of users, etc., and achieve the effect of ensuring security and preventing malicious access.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
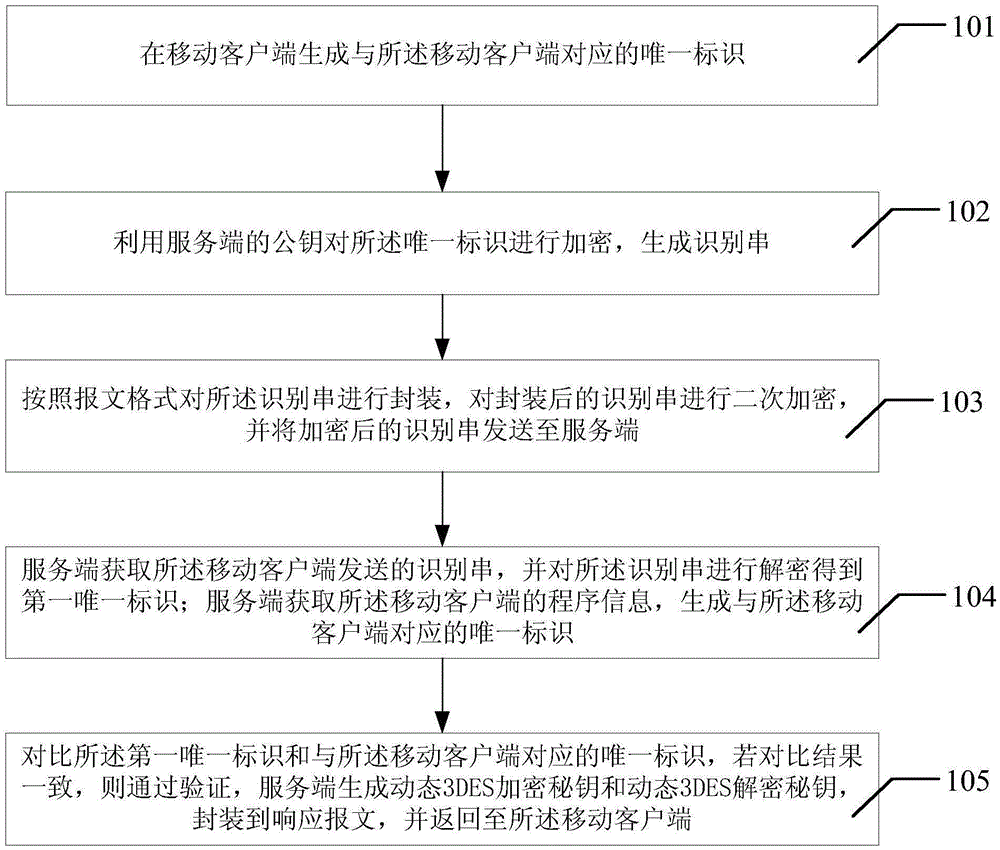
[0042] see figure 1 Shown is a specific embodiment of a data security transmission method described in this application. The method described in this embodiment includes the following steps:
[0043] Step 101, generating a unique identifier corresponding to the mobile client at the mobile client;
[0044] Step 102, using the public key of the server to encrypt the unique identifier to generate an identification string;
[0045] Step 103: Encapsulate the identification string according to the message format, perform secondary encryption on the encapsulated identification string, and send the encrypted identification string to the server;
[0046] Step 104: The server obtains the identification string sent by the mobile client, and decrypts the identification string to obtain a first unique identifier; the server obtains the program information of the mobile client, and generates a corresponding mobile client. Uniquely identifies;
[0047] Step 105, compare the first unique i...
Embodiment 2
[0058] The following provides an application embodiment of the data security transmission method of the present invention, taking the mobile client as an Android client as an example for description.
[0059] The Android client obtains the save path of the code according to the getPackageCodePath() method of the ContextWrapper class, then obtains the classes.dex file, then obtains the cyclic redundancy check value (CRC) of the file, and then adds a fixed secret key to the CRC string (the key string will be configured on the server), and the unique identifier corresponding to the mobile client is generated according to the SHA1 digest algorithm.
[0060] Use the public key of the server to encrypt with the RSA algorithm to generate an identification string, which can uniquely identify the published application version, and can prevent interception and tampering during the transmission process, and can also prevent denial.
[0061] The identification string is encapsulated accor...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More