Authentication method and terminal equipment
An identity verification method and technology for terminal equipment, which are applied in the field of identity verification methods and terminal equipment, can solve the problems of low reliability, peeping to obtain passwords, etc., and achieve the effects of high reliability, saving user costs, and improving user experience.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0024] In order to make the technical problems, technical solutions and beneficial effects solved by the present invention clearer, the present invention will be further described in detail below in conjunction with the accompanying drawings and embodiments. It should be understood that the specific embodiments described here are only used to explain the present invention, not to limit the present invention.
[0025] When ordinal numerals such as "first" and "second" are mentioned in the embodiments of the present invention, unless they really express the meaning of order according to the context, it should be understood that they are only used for distinction.
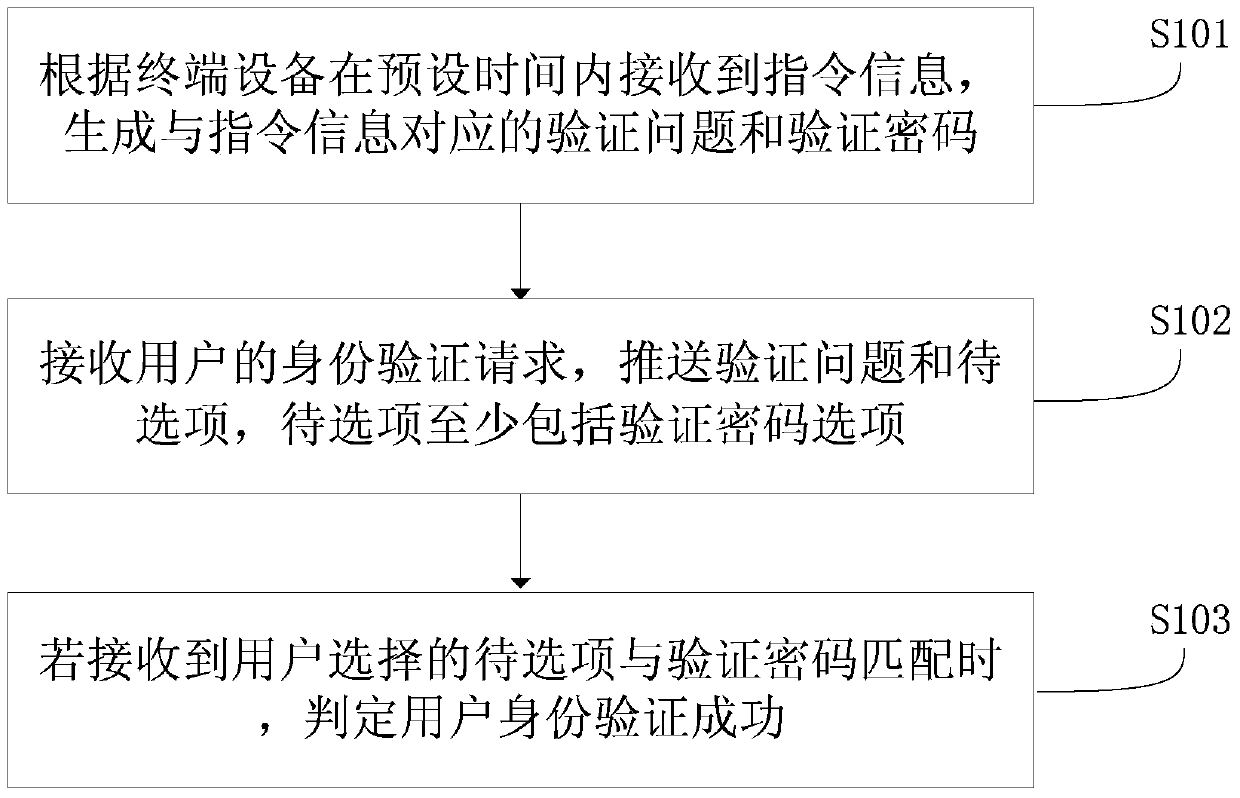
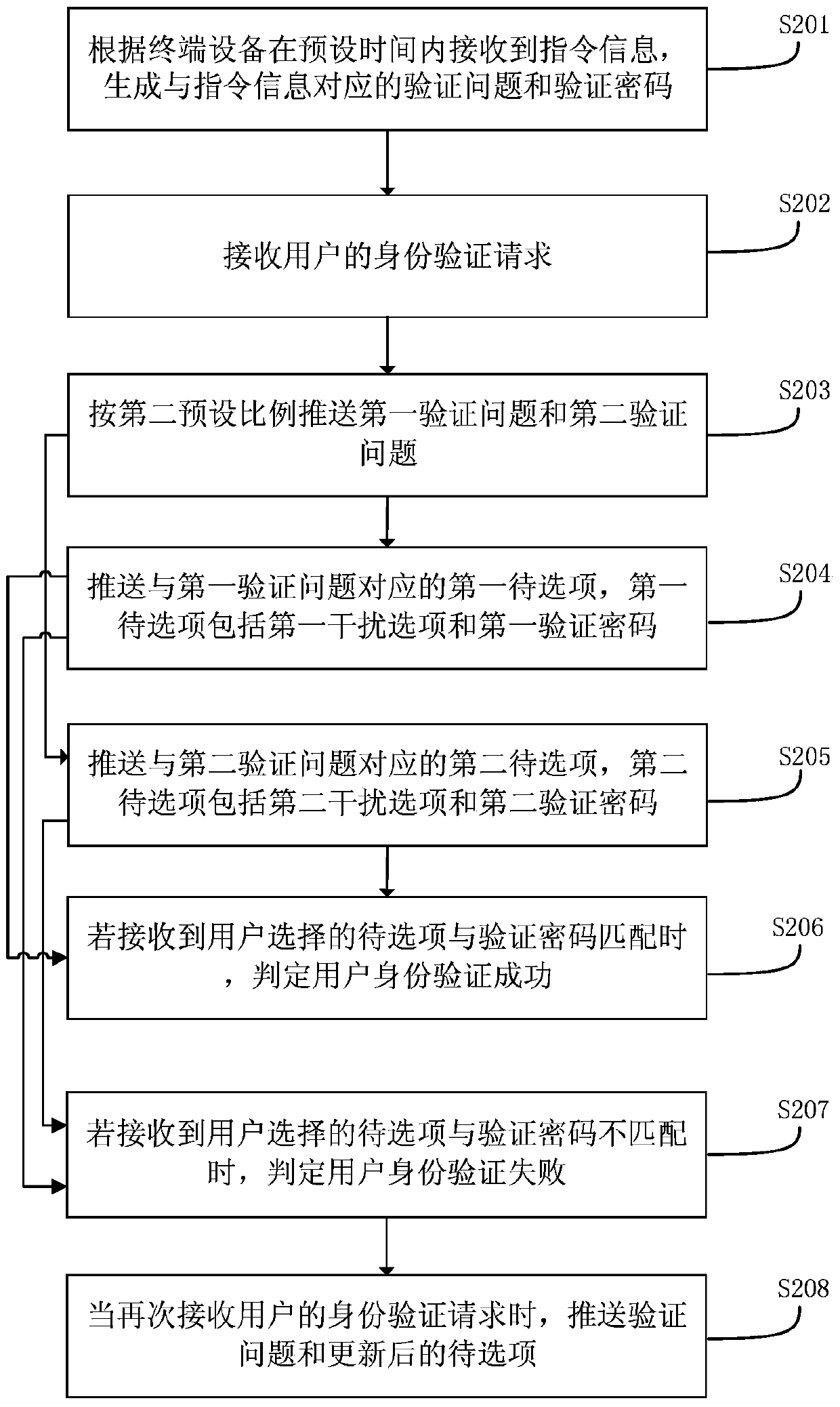
[0026] Such as figure 1 Shown is a schematic flow chart of the first embodiment of the identity verification method of the present invention. Including S101-S103.
[0027] S101. Generate a verification question and a verification password corresponding to the instruction information according to the instruction info...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More