Information operation and maintenance service knowledge sharing method based on trusted computing of big data
A trusted computing and knowledge sharing technology, applied in the field of information sharing, can solve the problems of poor timeliness and security of knowledge sharing in information operation and maintenance services, and the inability to safely and quickly realize shared information storage and release of shared information, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
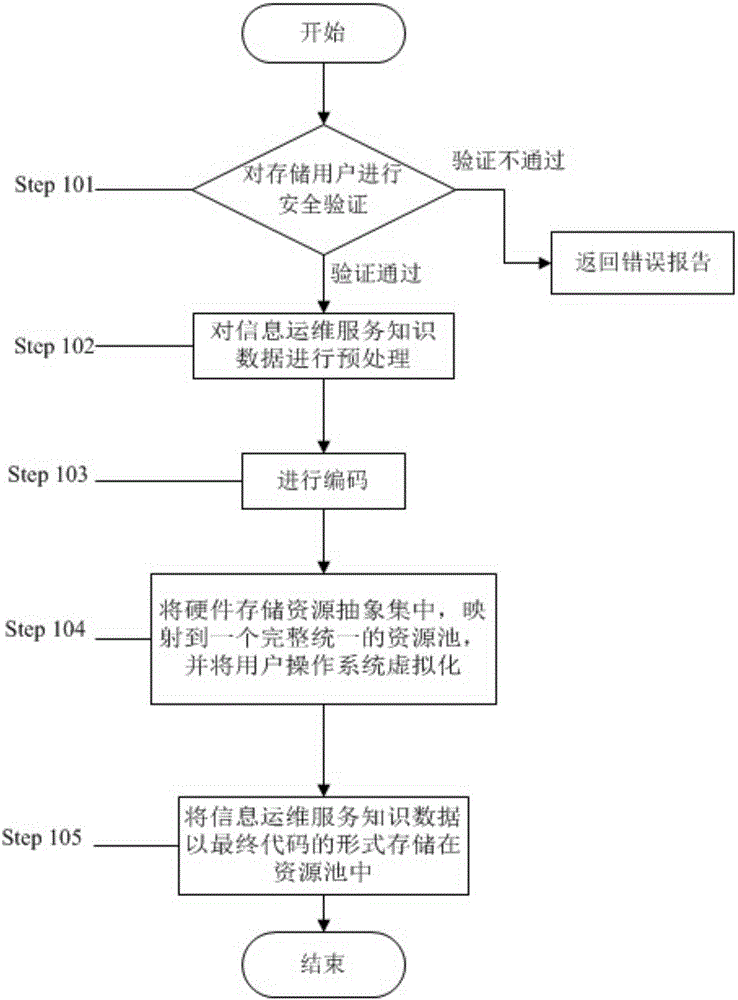
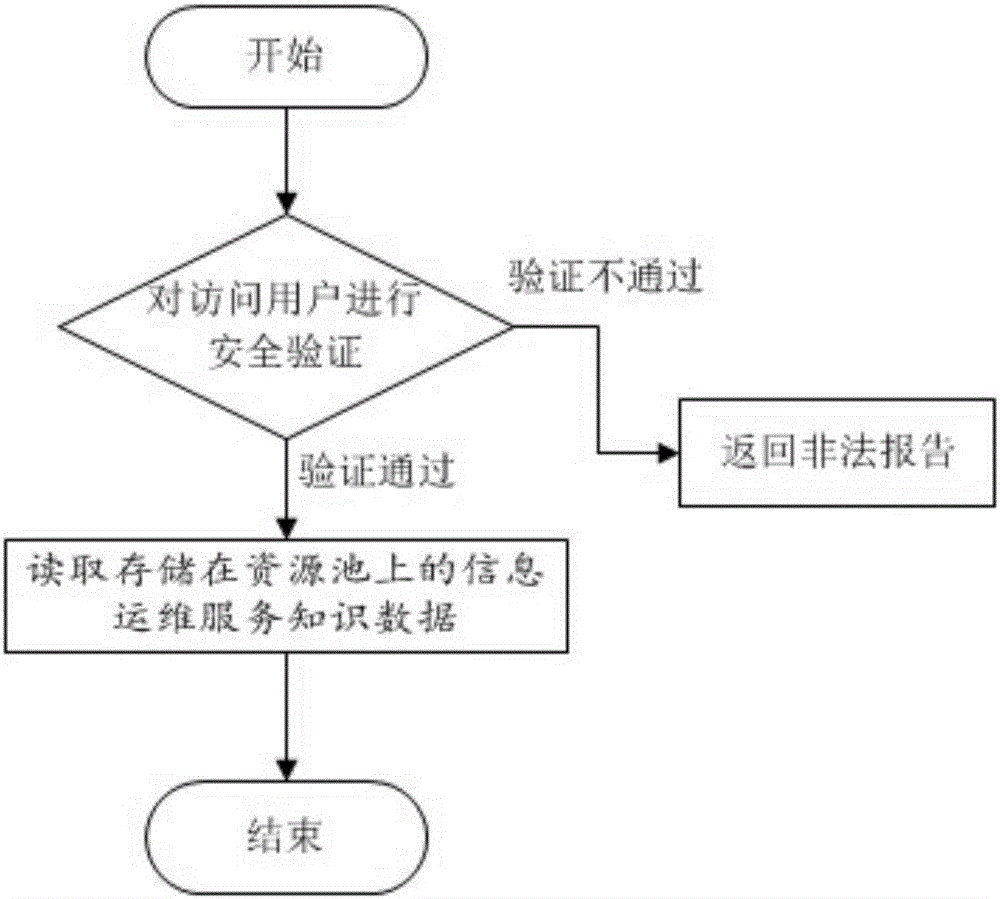
[0061] see figure 1 , figure 2 , this embodiment is based on big data trusted computing information operation and maintenance service knowledge sharing method, including information operation and maintenance knowledge security storage, information operation and maintenance knowledge security access and trustworthiness assessment;
[0062] The safe storage of the information operation and maintenance knowledge includes the following steps:
[0063] Step 101 When the storage user submits a storage request for operation and maintenance information knowledge security service knowledge, perform security verification on the storage user's identity;
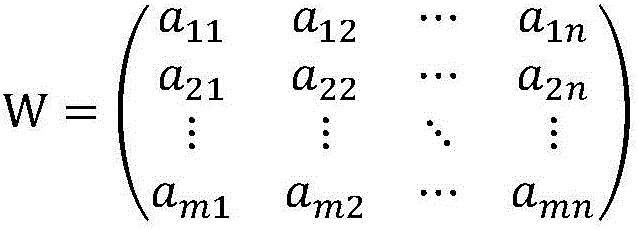
[0064] Step 102 preprocesses the information operation and maintenance service knowledge data, and divides the information operation and maintenance service knowledge into two types of data: basic knowledge and business knowledge. The basic knowledge includes text and images that can reflect the basic situation of information operatio...
Embodiment 2
[0083] see figure 1 , figure 2 , this embodiment is based on big data trusted computing information operation and maintenance service knowledge sharing method, including information operation and maintenance knowledge security storage, information operation and maintenance knowledge security access and trustworthiness evaluation;
[0084] The safe storage of the information operation and maintenance knowledge includes the following steps:
[0085] Step 101 When the storage user submits a storage request for operation and maintenance information knowledge security service knowledge, perform security verification on the storage user's identity;
[0086] Step 102 preprocesses the information operation and maintenance service knowledge data, and divides the information operation and maintenance service knowledge into two types of data: basic knowledge and business knowledge. The basic knowledge includes text and images that can reflect the basic situation of information operatio...
Embodiment 3
[0121] see figure 1 , figure 2 , this embodiment is based on big data trusted computing information operation and maintenance service knowledge sharing method, including information operation and maintenance knowledge security storage, information operation and maintenance knowledge security access and trustworthiness assessment;
[0122] The safe storage of the information operation and maintenance knowledge includes the following steps:
[0123] Step 101 When the storage user submits a storage request for operation and maintenance information knowledge security service knowledge, perform security verification on the storage user's identity;
[0124] Step 102 preprocesses the information operation and maintenance service knowledge data, and divides the information operation and maintenance service knowledge into two types of data: basic knowledge and business knowledge. The basic knowledge includes text and images that can reflect the basic situation of information operatio...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More