An android system heap overflow vulnerability verification method and device
A vulnerability and system process technology, applied in the field of information security, to achieve the effect of good scalability, high accuracy and strong pertinence
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0022] The specific implementation manners of the present invention will be further described in detail below in conjunction with the accompanying drawings and embodiments. The following examples are used to illustrate the present invention, but are not intended to limit the scope of the present invention.
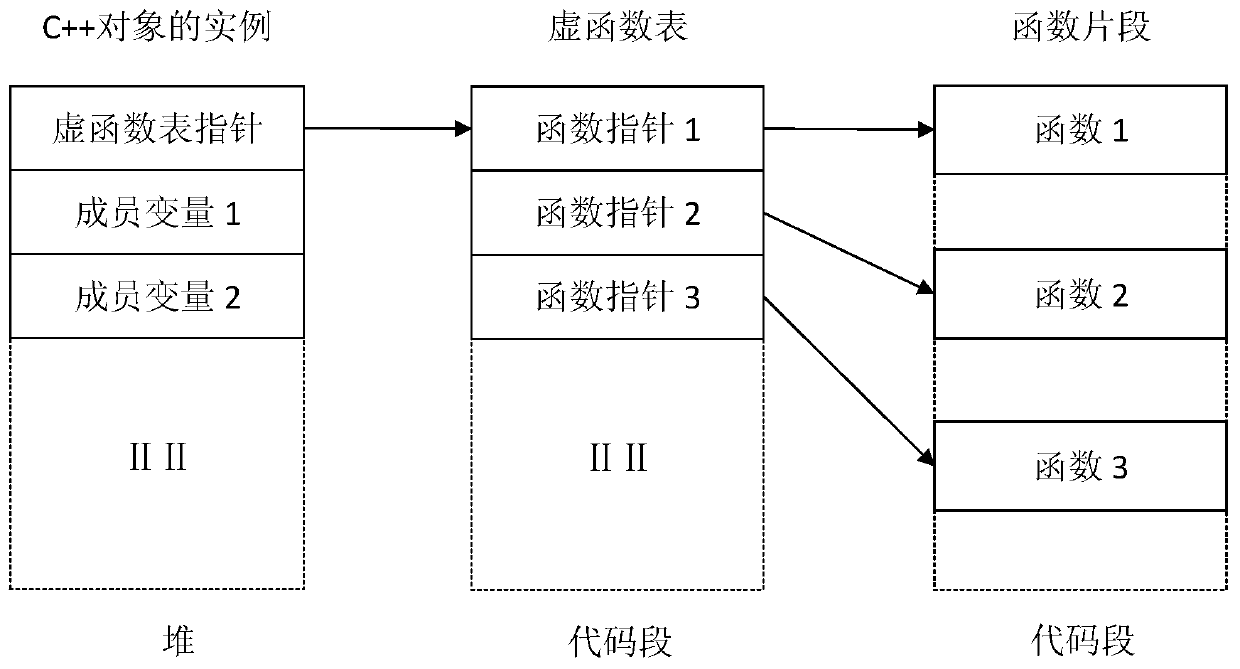
[0023] In the Android system, an instance of a C++ object is usually allocated in the heap memory space. If this C++ object implements virtual functions, its basic layout in memory is as follows figure 1 as shown, figure 1 A schematic diagram of the memory layout of a C++ object with virtual functions.
[0024] It can be seen that the instance of this C++ object is allocated in the heap memory space, and the virtual function table pointer of the four-byte length is stored in the starting position of the memory. Other data such as member variables are allocated behind this virtual function table pointer. The virtual function table pointer points to a virtual function ta...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More