Method and system for screening, categorizing and intercepting fraud samples of suspicious numbers
A number and suspicious technology, applied in electrical components, automatic switching offices, telephone communications, etc., can solve problems such as hidden dangers of network security, difficult deployment, and call paralysis of the entire network, to avoid infringement, improve trust and perception, Avoid the effects of subjectivity and blindness
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0034] The following will clearly and completely describe the technical solutions in the embodiments of the present invention with reference to the accompanying drawings in the embodiments of the present invention. Obviously, the described embodiments are only some, not all, embodiments of the present invention. All other embodiments obtained by persons of ordinary skill in the art based on the embodiments of the present invention belong to the protection scope of the present invention.
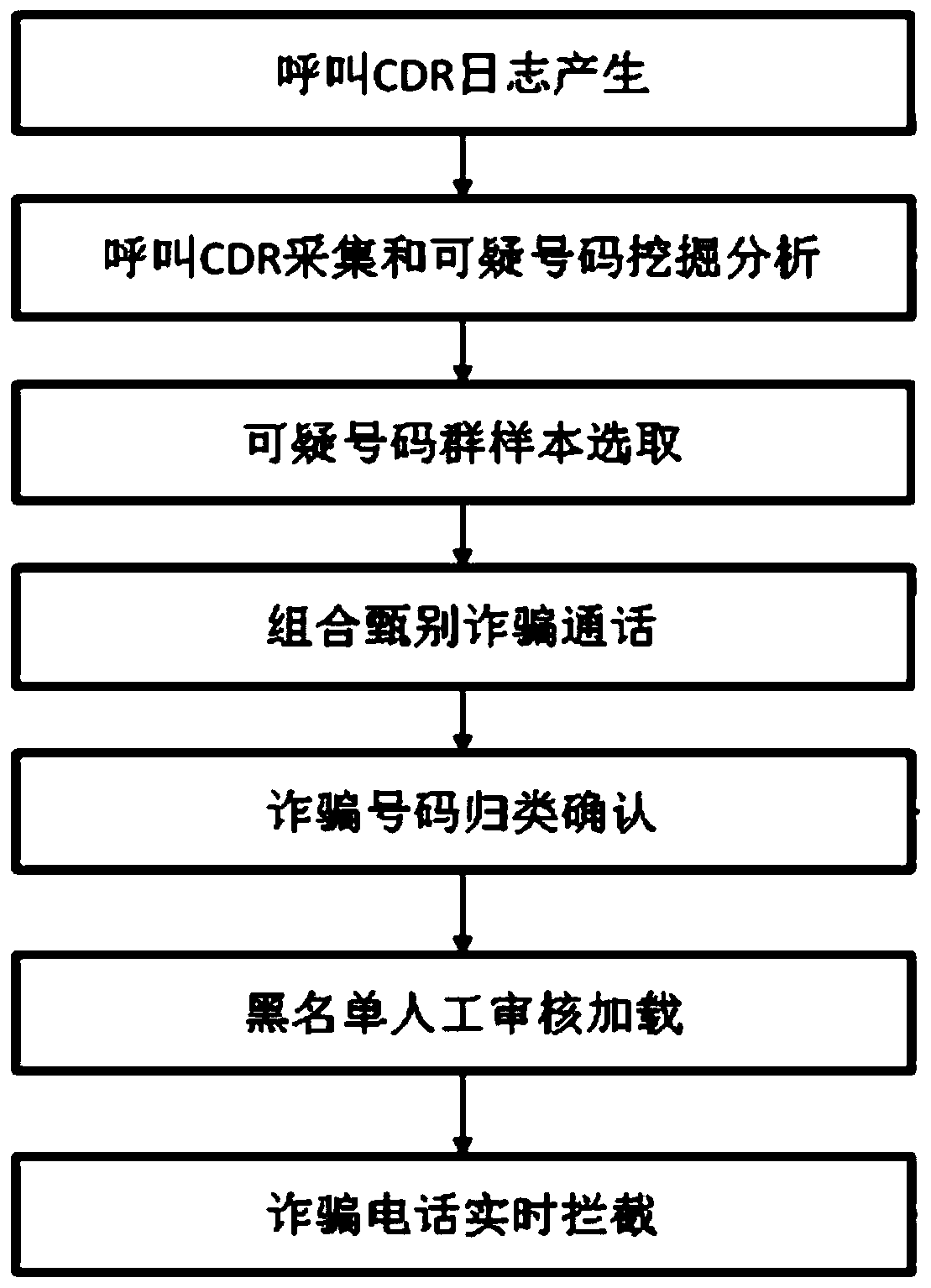
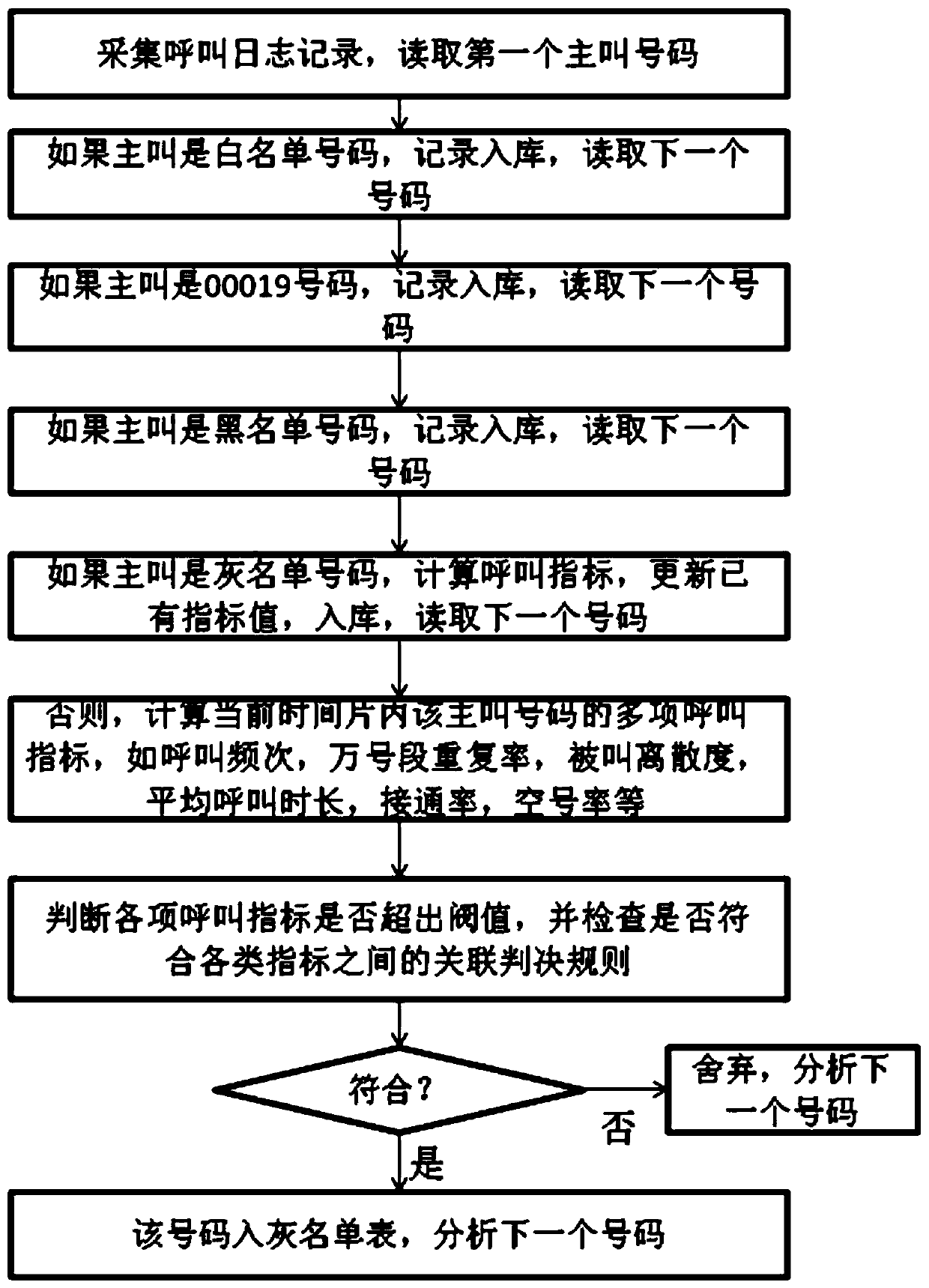
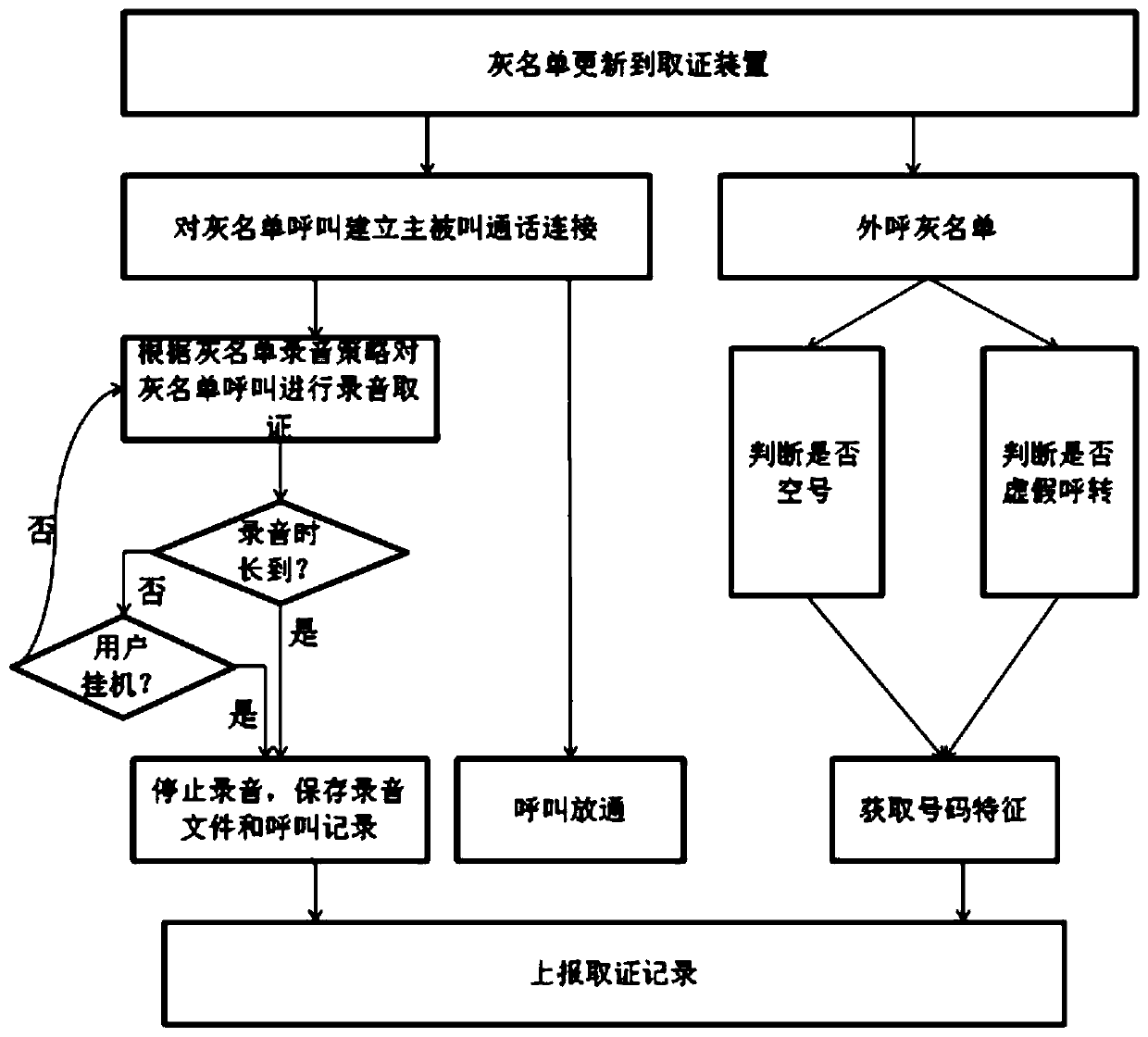
[0035] Such as Figure 1-7 As shown, according to the embodiment of the present invention, a method for screening, categorizing and intercepting fraudulent samples of suspicious numbers includes: S1 accessing the core network, collecting call logs: connecting the anti-fraud interception platform to the core network, and the core The network redirects the call to the interception device, and the interception device generates a call log for all calls, and sends the call log to the gray list ana...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More