Malicious software interception method and device and terminal
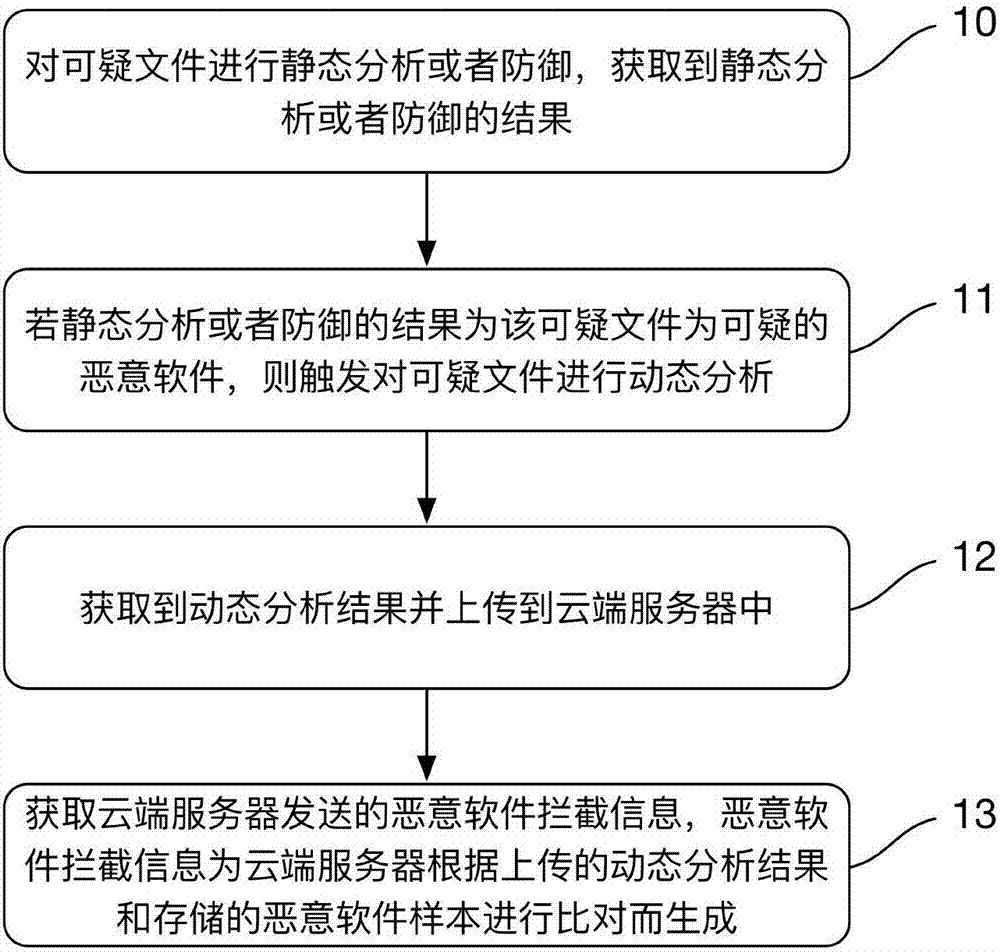
A technology of malicious software and interception devices, which is applied in the field of network security to achieve the effect of requiring no human intervention and consuming less time
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0034] It should be understood that the specific embodiments described here are only used to explain the present invention, not to limit the present invention.
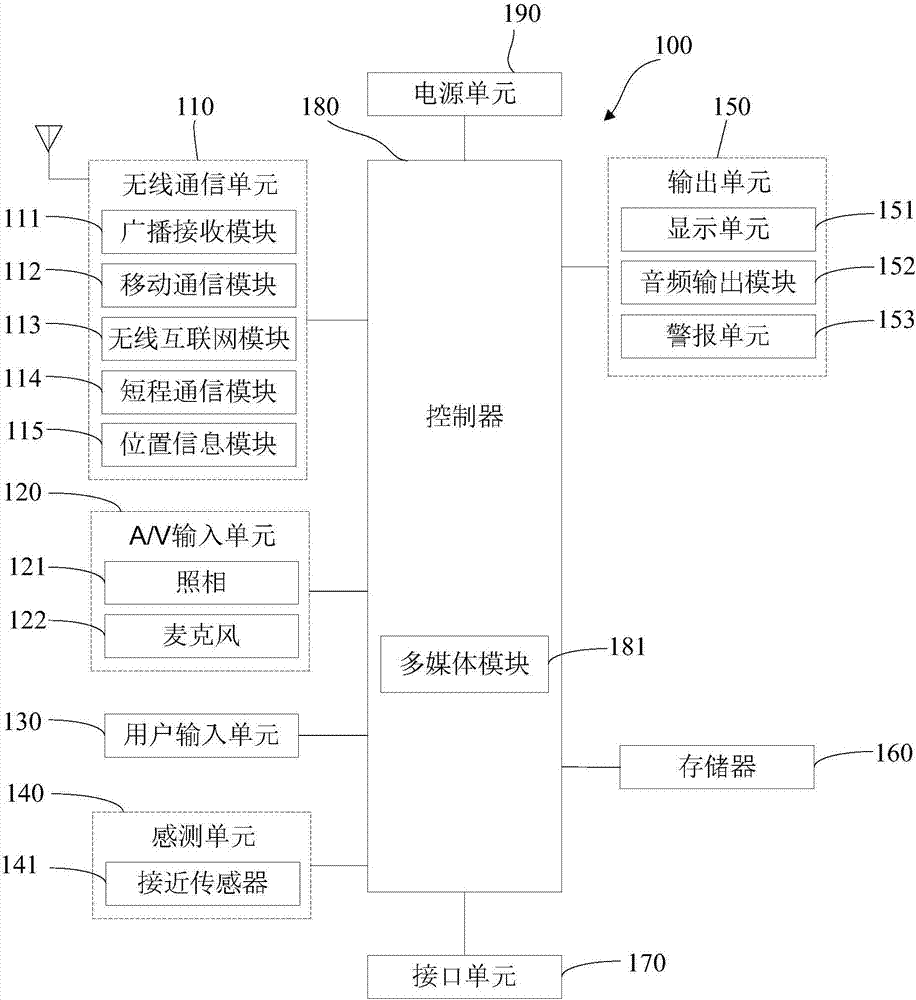
[0035] A mobile terminal implementing various embodiments of the present invention will now be described with reference to the accompanying drawings. In the following description, use of suffixes such as 'module', 'part' or 'unit' for denoting elements is only for facilitating description of the present invention and has no specific meaning by itself. Therefore, "module" and "component" may be used mixedly.
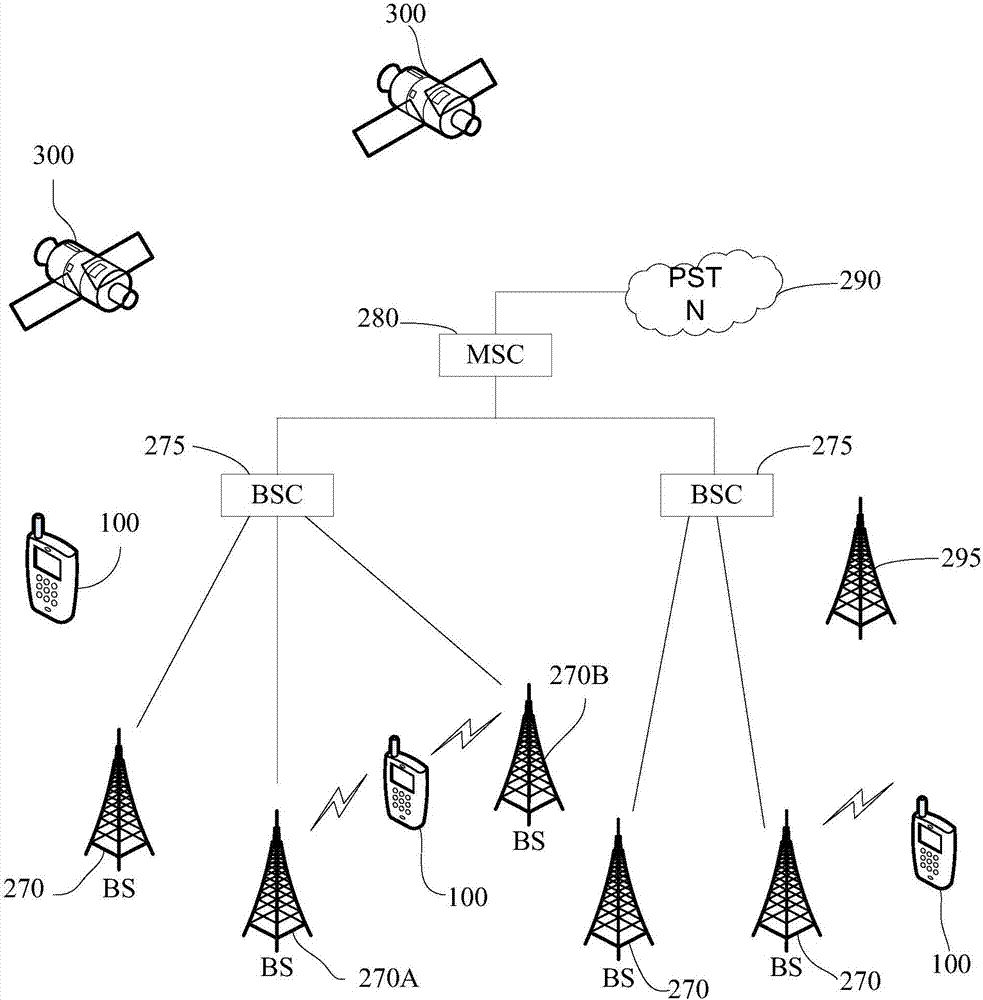
[0036] Mobile terminals may be implemented in various forms. For example, terminals described in the present invention may include devices such as mobile phones, smart phones, notebook computers, digital broadcast receivers, PDAs (Personal Digital Assistants), PADs (Tablet Computers), PMPs (Portable Multimedia Players), navigation devices, etc. mobile terminals and fixed terminals such as digital TVs, desktop c...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More