Whitelist network management and control system and method based on trusted chip
A network control and whitelist technology, applied in the field of information security, can solve problems such as the inability to realize effective network supervision and the inability to meet the diverse needs of users, and achieve the effect of ensuring security and integrity and meeting diverse needs
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
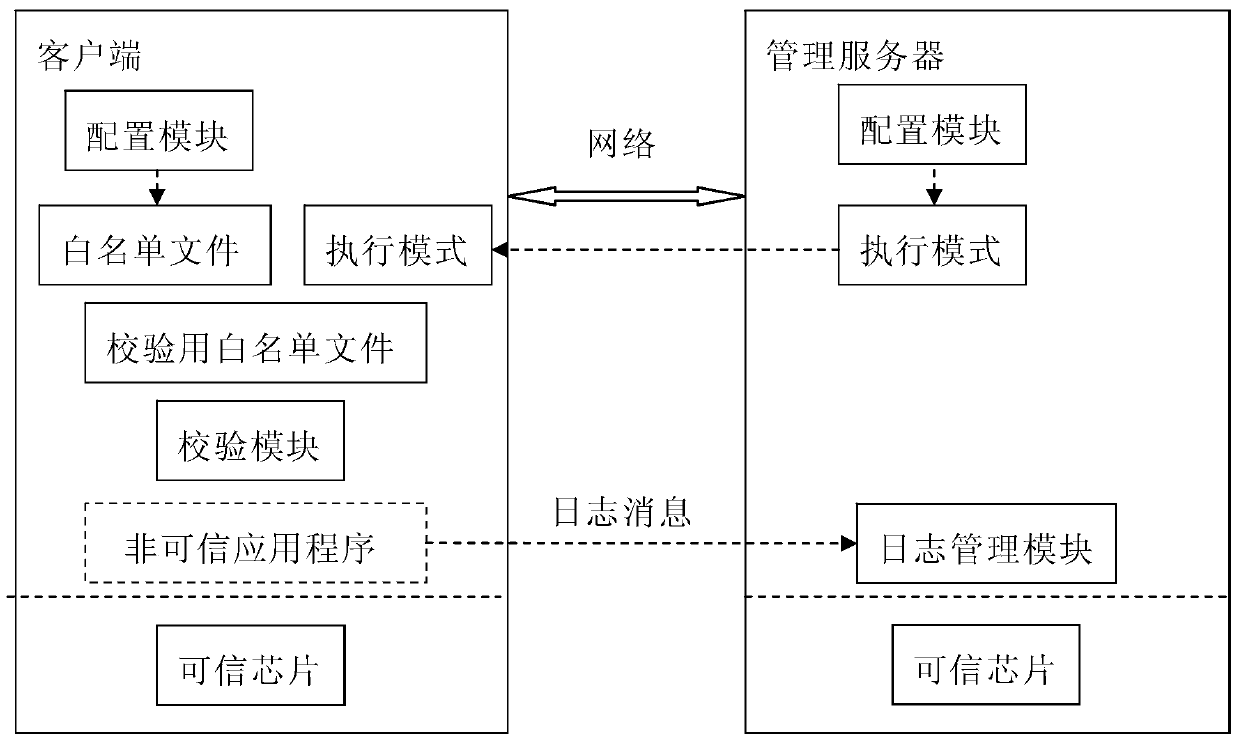
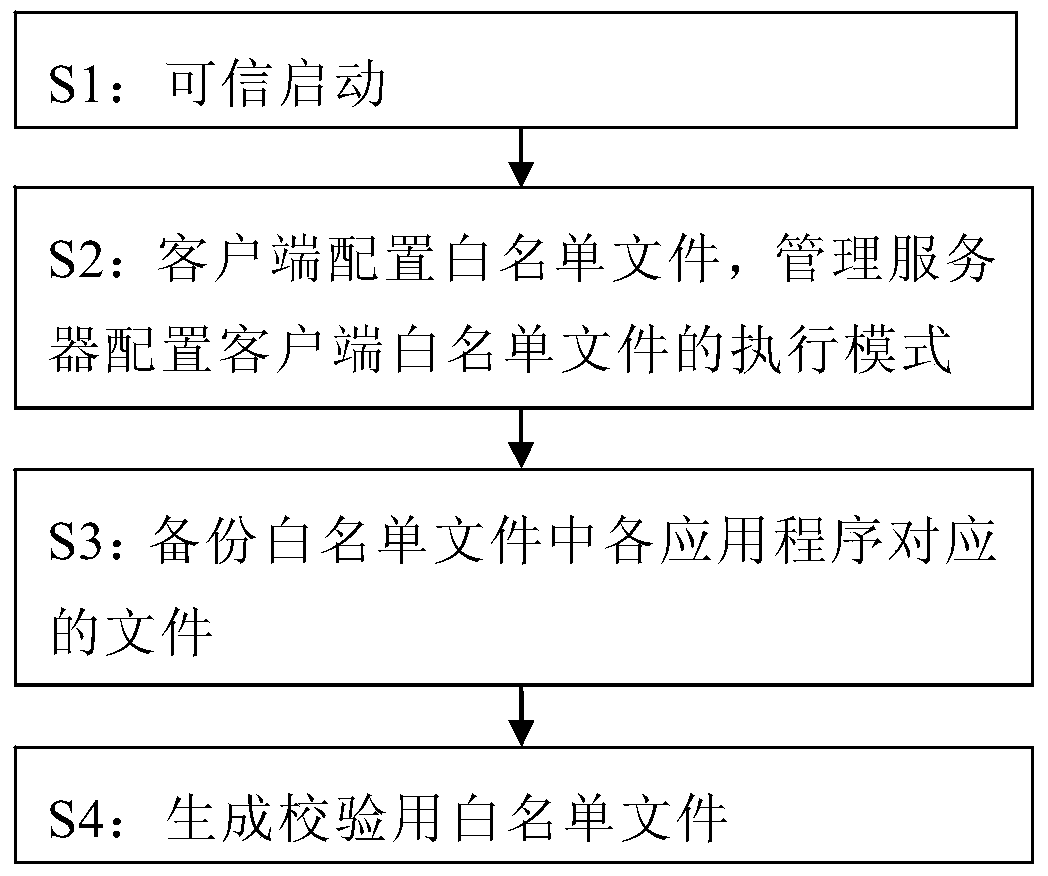
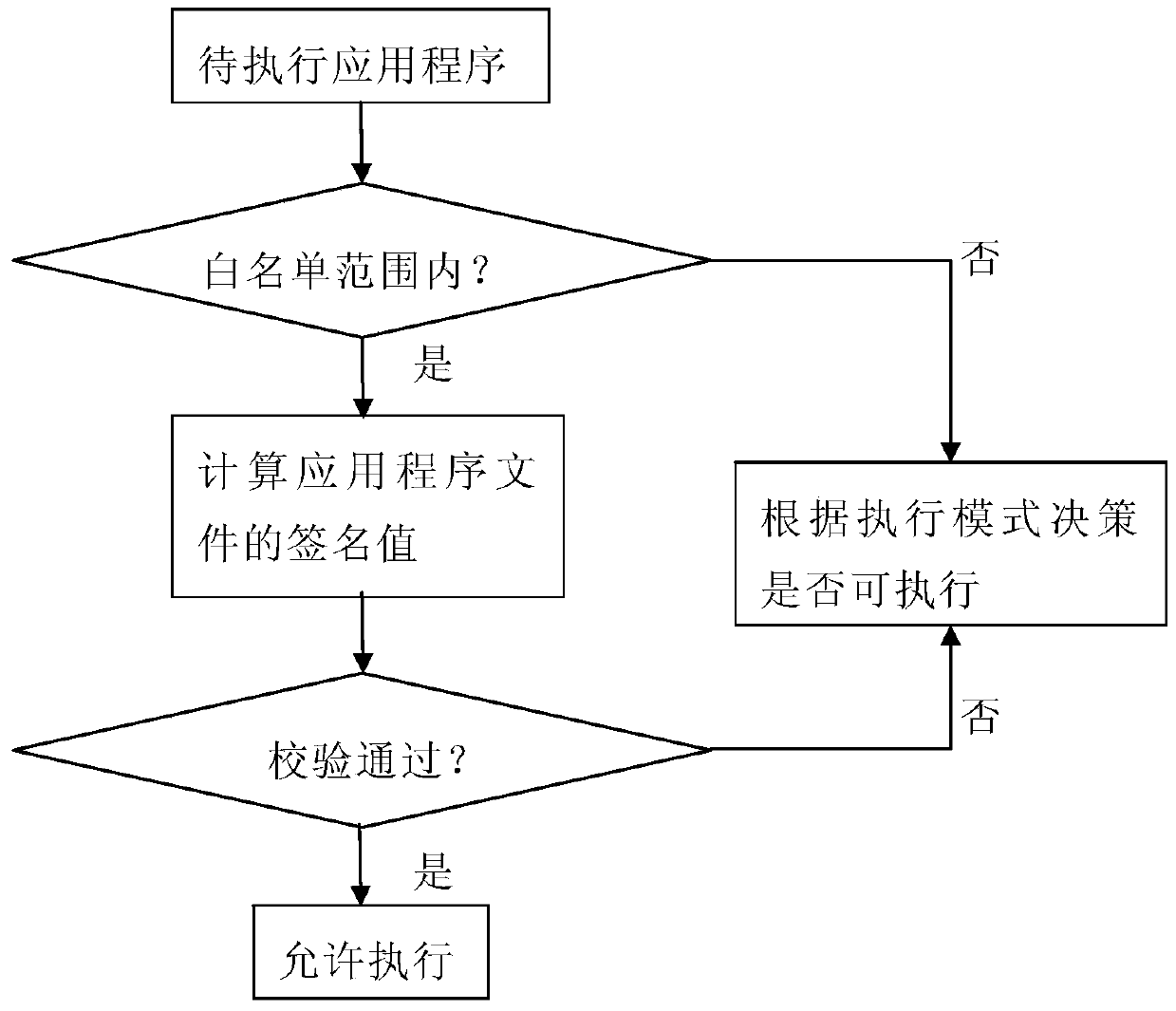
[0046] figure 1 It is a block diagram of the system composition of the present invention, as shown in the figure, the whitelist network management and control system based on trusted chips disclosed by the present invention includes a management server and a client, the management server and the client establish a network connection through the network, and the configuration module of the client It is used to set the whitelist file. The configuration module of the management server is used to configure the execution mode corresponding to the whitelist file of each client. The log management module of the management server is used to manage the logs of untrusted applications that fail the client verification. , when the client wants to execute the application program, the verification module verifies the application program, and the application program that passes the verification is allowed to execute, and the non-trusted application program that fails the verification determin...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More