Android application program strengthening method
An application and program technology, applied in the direction of program/content distribution protection, instruments, electronic digital data processing, etc., can solve the problems of insufficient encryption algorithm key protection, Android application attacks, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0026] The following will clearly and completely describe the technical solutions in the embodiments of the present invention with reference to the accompanying drawings in the embodiments of the present invention. Obviously, the described embodiments are only some, not all, embodiments of the present invention. Based on the embodiments of the present invention, all other embodiments obtained by persons of ordinary skill in the art without creative efforts fall within the protection scope of the present invention.
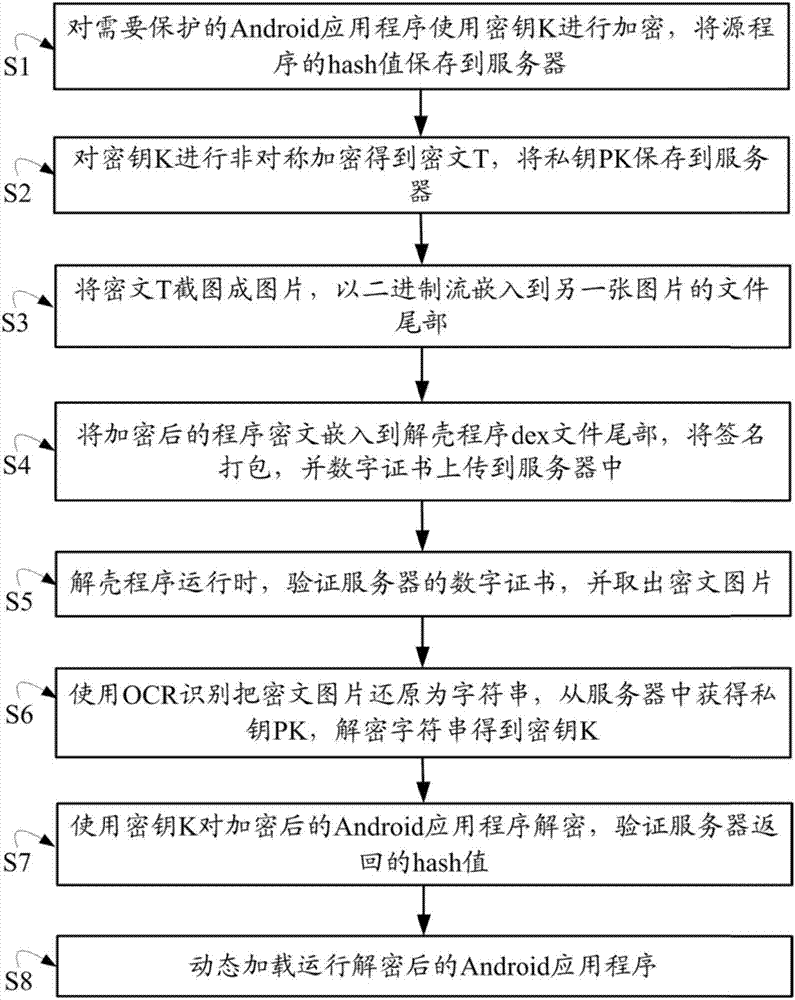
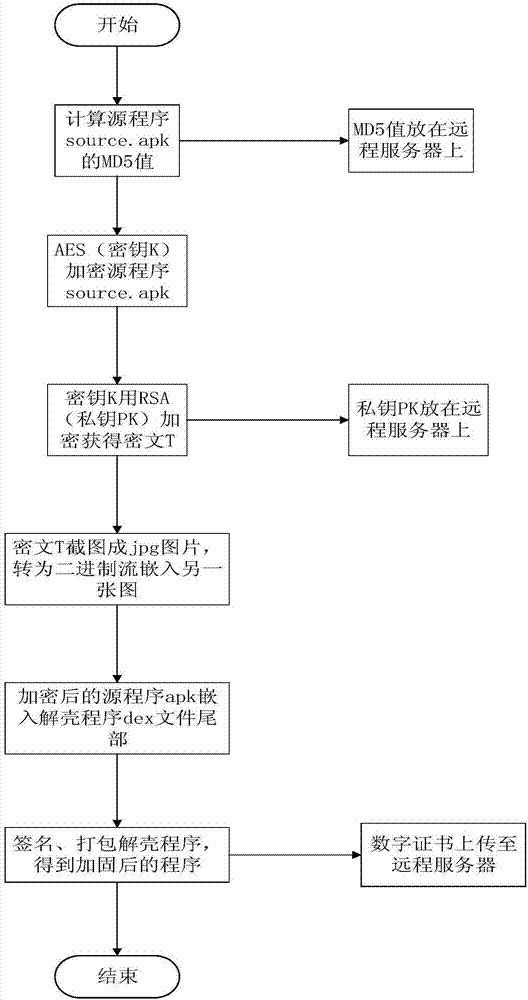
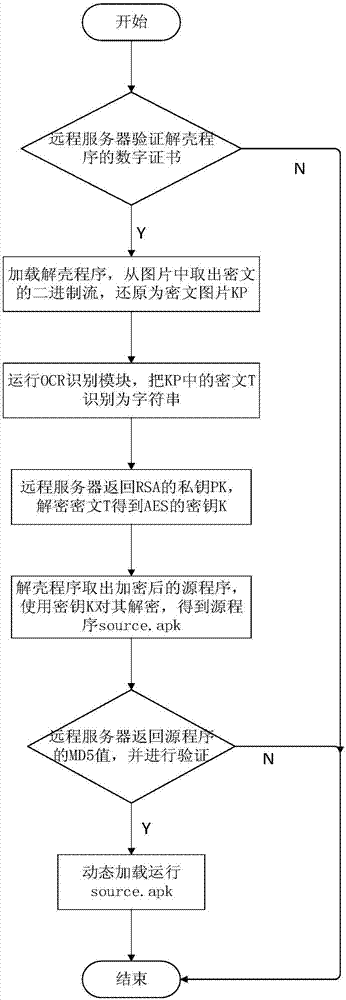
[0027] See figure 1 , a kind of Android application reinforcement method of the present invention, comprises steps
[0028] S1: Encrypt the Android application to be protected using the key K, and save the hash value of the source program to the server;
[0029] S2: Asymmetrically encrypt the key K to obtain the ciphertext T, and save the private key PK to the server;
[0030] S3: Screenshot the ciphertext T into a picture, and embed it into the end of another pi...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More