Authentication device, authentication system, authentication method, and storage medium
An authentication device and authentication method technology, applied in security devices, transmission systems, digital transmission systems, etc., can solve problems such as longer authentication processing time
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment approach 1
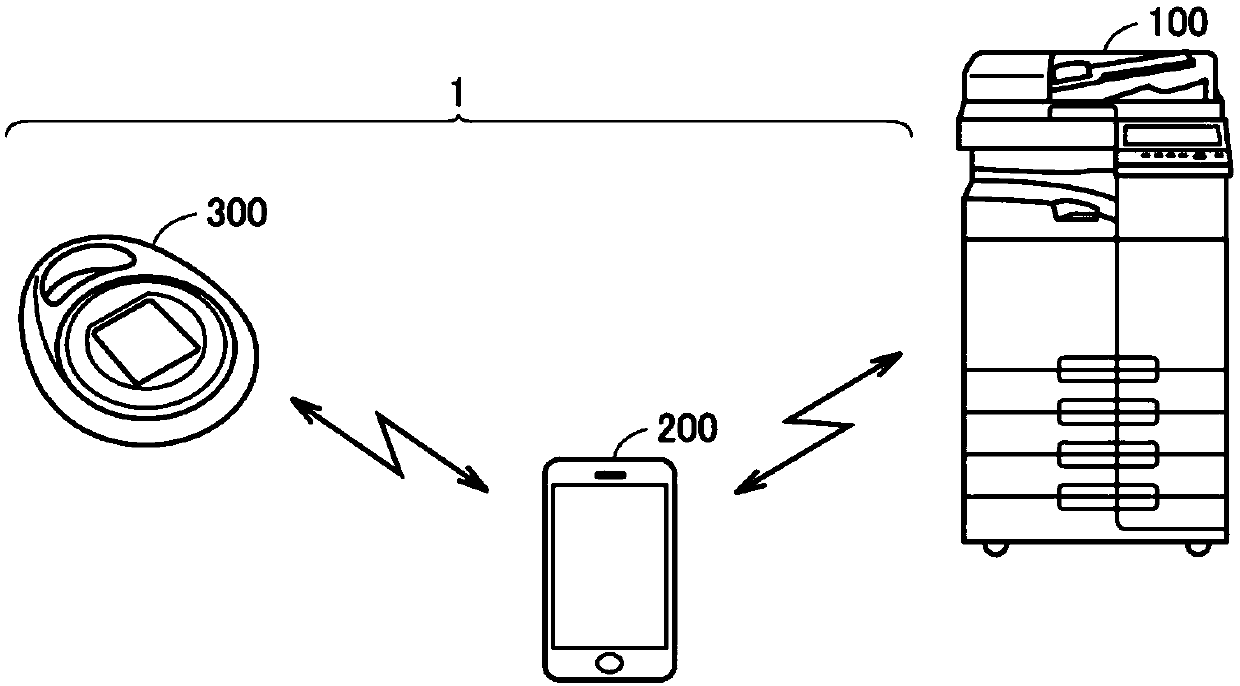
[0060] The outline of Embodiment 1 is as follows.
[0061] The authentication system includes a portable first device that acquires biological information of a subject, and a portable second device that communicates with the first device. The first device performs a first authentication process using the acquired biometric information, and the second device performs a second authentication process with a precision different from that of the first authentication process. The second device performs a second authentication process using the biometric information received from the first device when communication is established with the first device. During the period when the above-mentioned communication is established and the subject is authenticated through the second authentication process and the predetermined condition is satisfied after the subject is authenticated through the first authentication process, the first device sends an Information about the subject.
[0062] ...
Embodiment approach 2
[0151] The outline of Embodiment 2 is as follows.
[0152] The portable authentication device includes a biological information acquisition unit for acquiring biological information of a subject, a communication unit for wirelessly communicating with an external device including a terminal device carried by the subject, and a processor as a control unit. The processor executes authentication processing for confirming the validity of the subject based on the acquired biometric information. That is, through the authentication process, it is possible to confirm whether or not the subject is himself. The authentication device differs the accuracy of authentication processing (hereinafter referred to as authentication accuracy) depending on whether or not communication (connection) has been established with the terminal device. The authentication device judges whether or not communication has been established based on the strength (unit: dB) of a signal received from the terminal ...
Embodiment approach 3
[0233] In the third embodiment, a program for causing the mobile terminal 200 ( 200A) or the biometric authentication sensor 300 ( 300A) to execute the authentication process in each of the above-mentioned embodiments is provided. Such procedures include at least Figure 7 ~ Figure 9 , Figure 12 to Figure 14 , Figure 16 and Figure 17 The procedure shown in the flowchart. It can also be recorded in computer-readable records such as floppy disk, CD-ROM (Compact Disk-Read Only Memory), ROM, RAM, and memory card attached to the computer of the portable terminal 200 (200A) or the biometric authentication sensor 300 (300A). media and delivered as a Program Product. Alternatively, the program can be recorded on a recording medium such as a hard disk built in a computer and provided. In addition, the program can also be provided by downloading via the network. The program is executed by one or more processors such as CPU20 or CPU30, or by a combination with a processor or a c...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More