Shared key establishment method suitable for computing resource dissymmetric fields
A technology for sharing keys and computing resources, applied in the field of information security, can solve problems such as low implementation efficiency, mathematical difficulties, and weak terminal computing resources, and achieve the effect of improving implementation efficiency
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0020] In order to facilitate those of ordinary skill in the art to understand and implement the present invention, the present invention will be described in further detail below in conjunction with the accompanying drawings and embodiments. It should be understood that the implementation examples described here are only used to illustrate and explain the present invention, and are not intended to limit this invention.
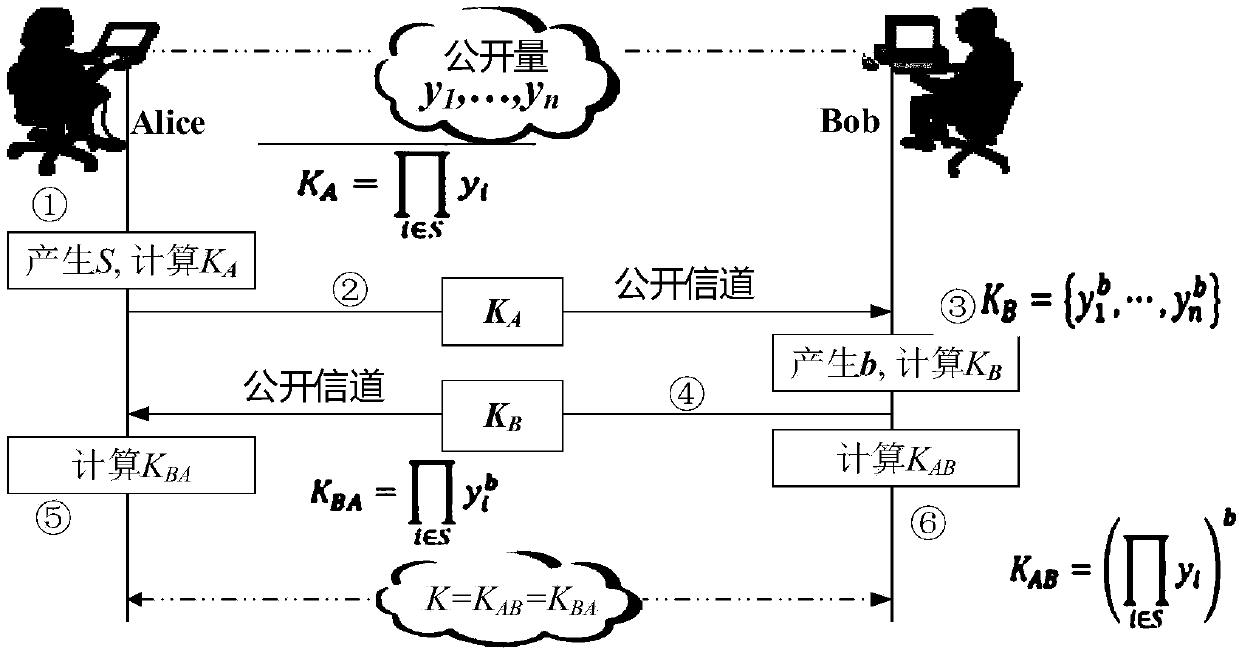
[0021] please see figure 1 , a method for establishing a shared key applicable to the field of asymmetric computing resources provided by the present invention. Assuming that the two parties in communication are Bob and Alice, the establishment of key sharing by the two parties in communication includes the following steps:
[0022] Step 1: Build the system;
[0023] Cyclic group Then randomly pick n values y 1 ,…, Then the public parameters of the system are
[0024] Step 2: Alice randomly selects the set evenly Use S as your temporary private k...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More