A POS terminal activating method
A terminal, to-be-activated technology, applied in the field of communication security, can solve the problems of access failure, cumbersome, poor user experience, etc., and achieve the effect of avoiding intervention failure, cumbersome solution steps, and simple steps
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0015] The following description and drawings illustrate specific embodiments of the invention sufficiently to enable those skilled in the art to practice them. Other embodiments may incorporate structural, logical, electrical, process, and other changes. The examples merely represent possible variations. Individual components and functions are optional unless explicitly required, and the order of operations may vary. Portions and features of some embodiments may be included in or substituted for those of other embodiments. The scope of embodiments of the present invention includes the full scope of the claims, and all available equivalents of the claims.
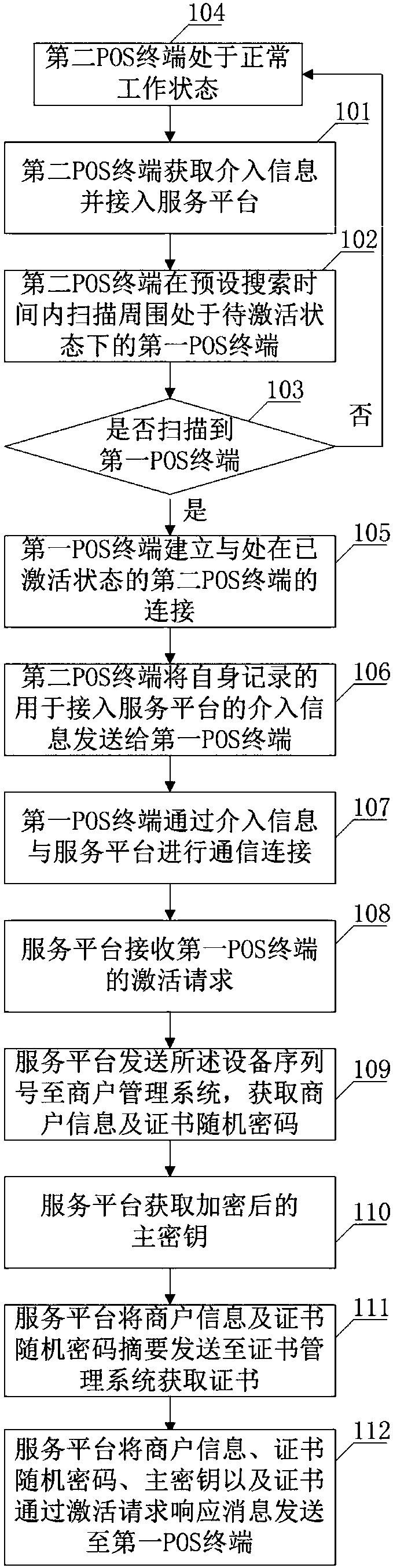
[0016] Such as figure 1 As shown, in some illustrative embodiments, a POS terminal activation method is provided, comprising:
[0017] 101: The second POS terminal acquires intervention information and accesses the service platform.
[0018] 102: The second POS terminal scans for the first POS terminals in the to-be-ac...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More