Authentication method in network slice, slice authentication proxy entity and session management entity
A network slicing and session management technology, applied in the field of communication, can solve problems such as insufficient authentication scheme, and achieve the effect of ensuring the security of slicing
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 2
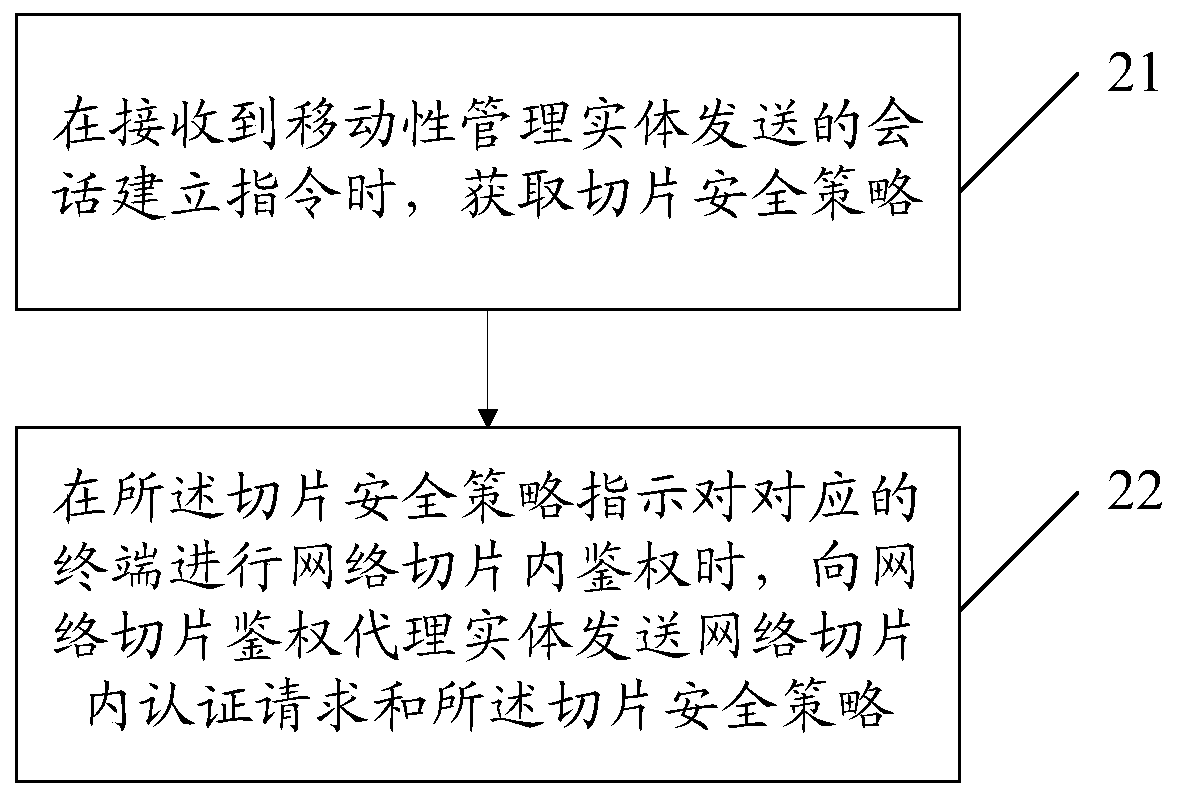
[0086] Such as figure 2 As shown, Embodiment 2 of the present invention provides an authentication method in a network slice, which can be applied to a session management entity, and the method includes:
[0087] Step 21: Obtain the slice security policy when receiving the session establishment instruction sent by the mobility management entity;
[0088] Step 22: When the slice security policy indicates that the corresponding terminal is authenticated in the network slice, send a network slice authentication request and the slice security policy to the network slice authentication proxy entity.
[0089] The method for authenticating within the network slice provided by Embodiment 2 of the present invention obtains the slice security policy when receiving the session establishment instruction sent by the mobility management entity, and performs network During intra-slice authentication, send an authentication request in the network slice and the slice security policy to the n...
Embodiment 3
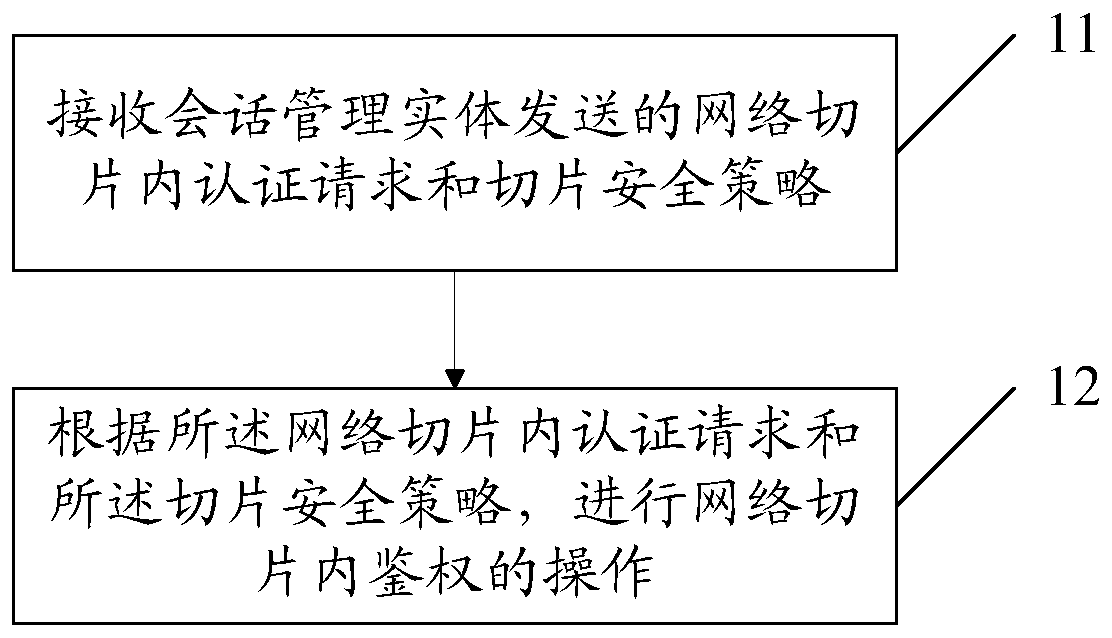
[0190] Such as Figure 6 As shown, Embodiment 3 of the present invention provides a network slice authentication proxy entity, including:
[0191] The first receiving module 61 is configured to receive the authentication request in the network slice and the slice security policy sent by the session management entity;
[0192] The first processing module 62 is configured to perform an intra-network slice authentication operation according to the intra-network slice authentication request and the slice security policy.
[0193] The network slice authentication proxy entity provided in Embodiment 3 of the present invention receives the network slice authentication request and slice security policy sent by the session management entity, and performs network slice authentication according to the network slice authentication request and the slice security policy. The operation of authentication in the slice; it can complete the authentication in the network slice, further guarantee...
Embodiment 4
[0204] Such as Figure 7 As shown, this embodiment provides a network slice authentication proxy entity, including:
[0205] Processor 71; and a memory 73 connected to the processor 71 through a bus interface 72, the memory 73 is used to store programs and data used by the processor 71 when performing operations, when the processor 71 calls and When executing the programs and data stored in the memory 73, the following processes are performed:
[0206] Receive the authentication request and slice security policy in the network slice sent by the session management entity through the transceiver 74;
[0207] An operation of authentication in the network slice is performed according to the authentication request in the network slice and the security policy of the slice.
[0208] Wherein, the transceiver 74 is connected to the bus interface 72 for receiving and sending data under the control of the processor 71 .
[0209] It should be noted that, in Figure 7 Among them, the b...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More