Data integrity verification method supporting key updating and third-party privacy protection
A data integrity and key update technology, applied in the field of cloud storage security, can solve the problems of lack of encryption primitives, unforgeability, and inability to update keys, and achieve the effect of reducing computational overhead and communication overhead
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0034] The technical solutions provided by the present invention will be described in detail below in conjunction with specific embodiments. It should be understood that the following specific embodiments are only used to illustrate the present invention and not to limit the scope of the present invention.
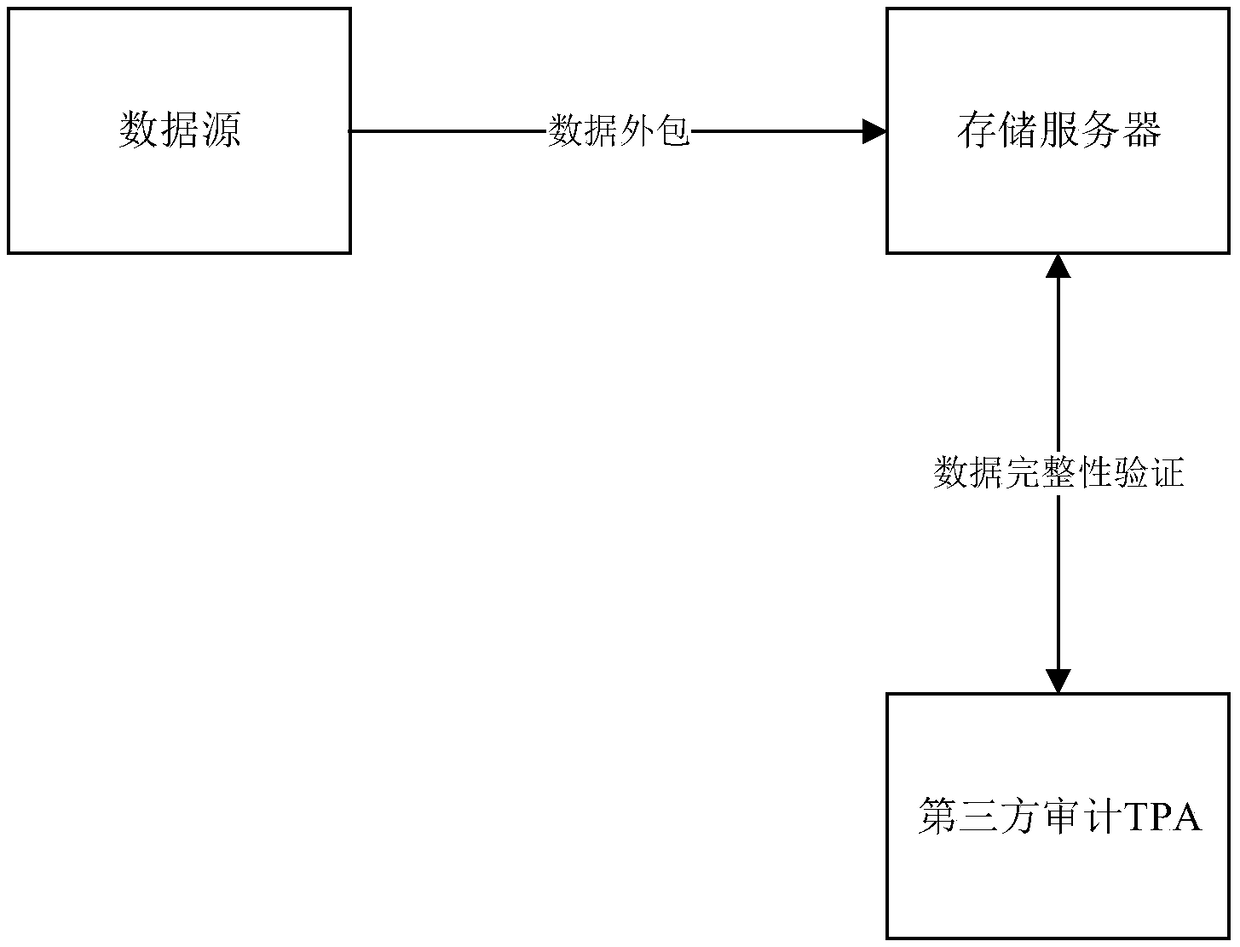
[0035] The data integrity verification method that supports key update and third-party privacy protection provided by the present invention is implemented based on the data integrity verification protocol system model, such as figure 1 As shown, the model includes three entities: data source, storage server and third-party audit TPA.
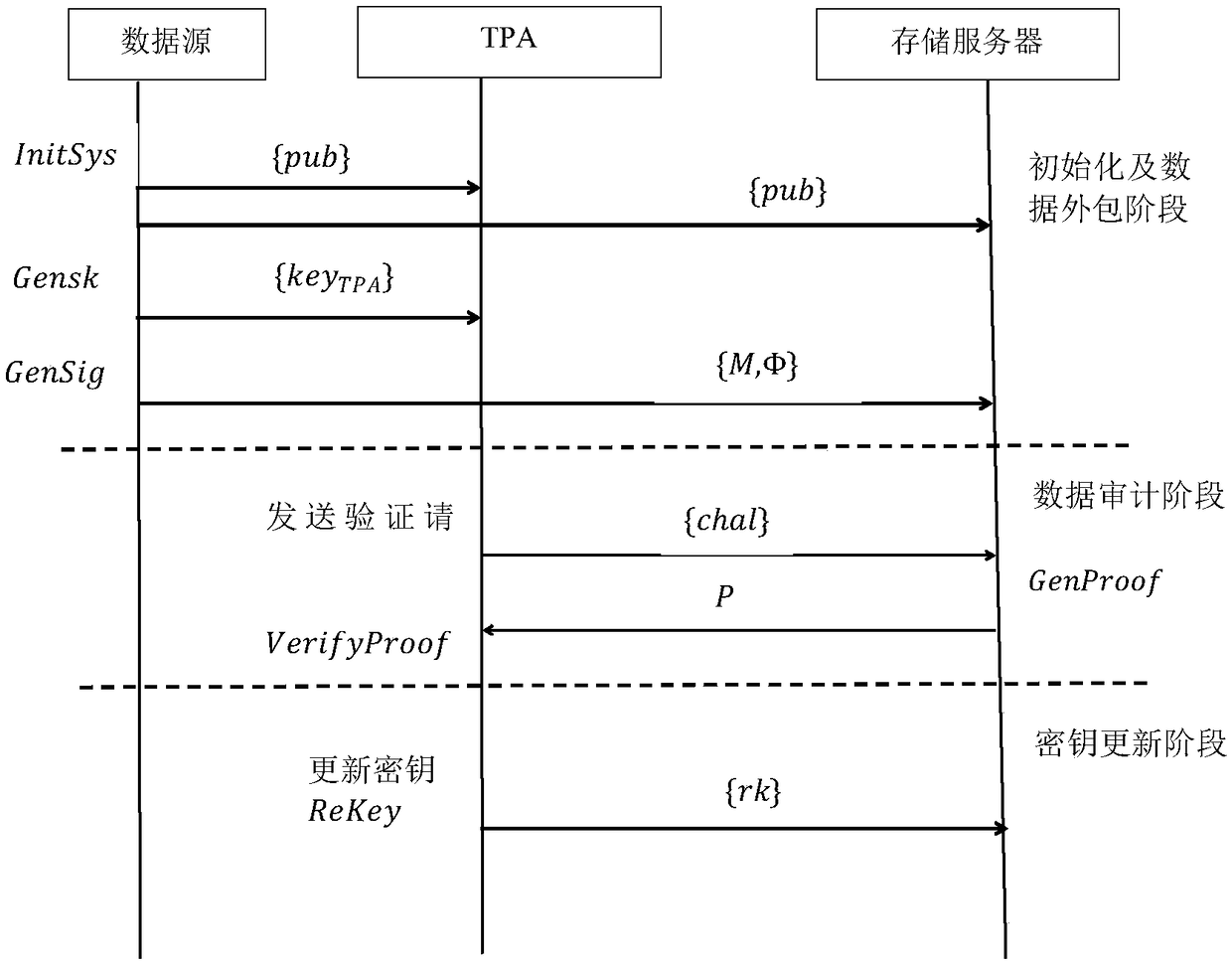
[0036] The method of the present invention includes three major contents: initialization and data outsourcing stage, data audit stage, and key update stage.
[0037] Such as figure 2 As shown, in the initialization and data outsourcing stage, the public parameters are first initialized, the key parameters are generated by the data source, and the...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More