However, although the attendance
check in the existing management software is operated on employees, the attendance rules are directly set for users or employees.
The current employee-oriented attendance method has the following deficiencies: (1) When a new employee enters the job, it is necessary to set the attendance rule for the new employee separately. If the setting is delayed or the attendance rule of the new employee is not set, it will Affect the normal attendance of the new employee; for example, after employee A is newly hired, in addition to assigning a job to employee A, the corresponding attendance rules need to be set separately for employee A; (2) when the employee is transferred (the attendance rules and If the attendance rules of the previous position are different), it is necessary to actively set new attendance rules for the employee. If the new attendance rules are not set for the employee in time, it will cause errors in the employee's attendance statistics; for example, the company's administrative department The
working hours of the company are 9:00-17:00, and the
working hours of the
production department are 8:00-18:00. When employee A is transferred from the
production department to the administration department and fails to set new attendance rules for employee A in time, If employee A clocks in at 8:30 and clocks out at 17:30, the management software still performs attendance statistics according to the original rules at this time, so that employee A's attendance is recorded as being late and leaving early, resulting in the statistics for employee A Attendance information does not match the actual situation
[0006] However, the traditional role-based user
rights management methods all adopt the "role-to-user one-to-many" association mechanism. / Position / Type of work and other concepts, the
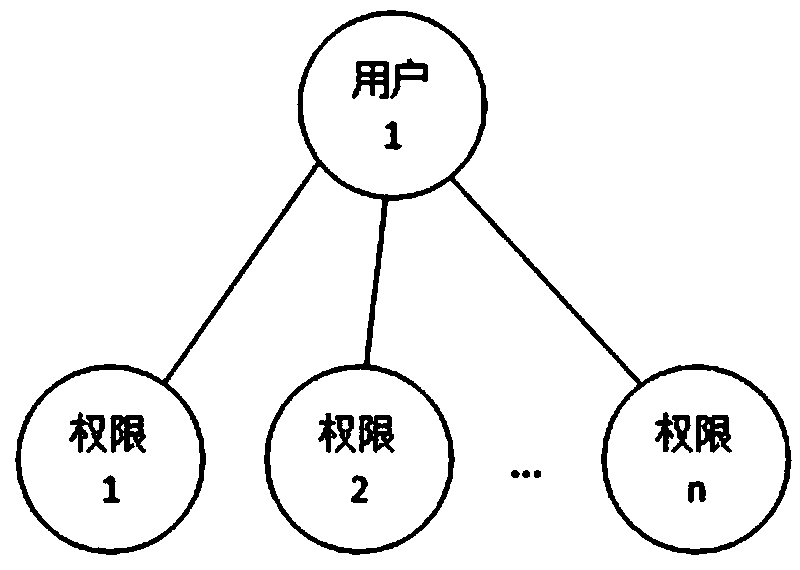
authorization of user rights under this association mechanism is basically divided into the following three forms: 1. figure 1 As shown, directly authorizing users has the disadvantages of heavy
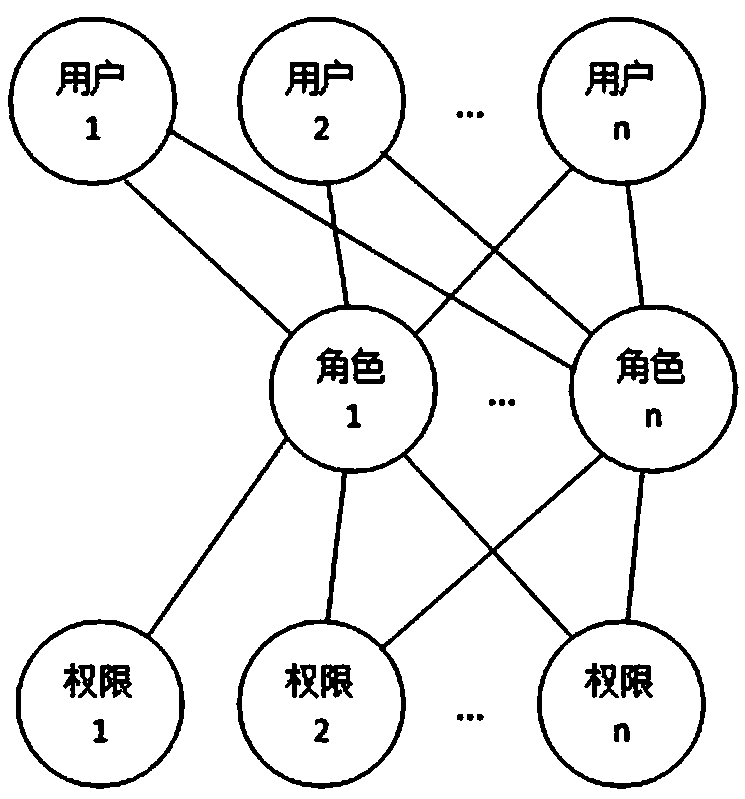
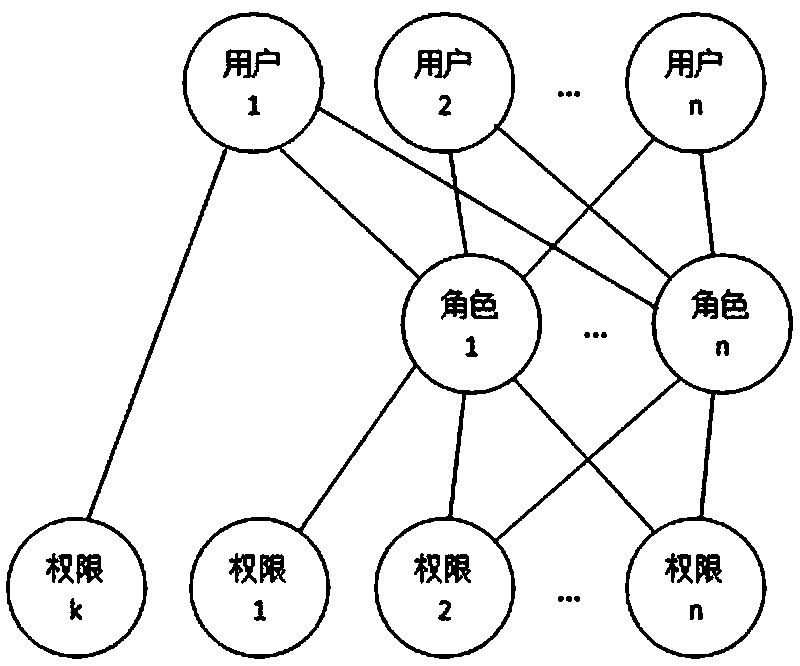
workload, frequent and cumbersome operations; 2. figure 2 As shown, authorize the role (category / group / position / type of work) (a role can be associated with multiple users), and the user obtains the authority through the role; 3. For example image 3 As shown, the combination of the above two methods
[0007] In the above statement, both 2 and 3 need to authorize the role of class / group nature, but the way of
authorization through the role of class / group / post / job nature has the following disadvantages: 1. The operation is difficult when the user authority changes: In the actual system use, it is often necessary to adjust the user's permissions during the operation process. For example, when dealing with changes in employee permissions, the permissions of an employee associated with a role change. We cannot Changes to change the permissions of the entire role, because the role is also associated with other employees whose permissions have not changed
The above two
processing methods not only take a long time to authorize the role in the case of many role permissions, but also are prone to mistakes. The operation of the user is cumbersome and troublesome, and it is also easy to make mistakes and cause losses to the system user.
[0008] 2. It is difficult to remember the specific permissions contained in the role for a long time: If the role has many permission function points, it is difficult to remember the specific permissions of the role over time, and it is even more difficult to remember the permission differences between roles with similar permissions. To associate a new user, it is impossible to accurately determine how to choose the association
[0009] 3. Due to the change of user permissions, more and more roles will be created (if no new roles are created, the direct
authorization to users will be greatly increased), and it is more difficult to distinguish the specific differences between the permissions of each role
[0010] 4. When transferring a post, if you want to assign many permissions of the transferred user to several other users, you must distinguish these permissions of the transferred user during
processing, and then create roles to associate with the other users. users, such an operation is not only complicated and time-consuming, but also prone to errors
 Login to View More
Login to View More  Login to View More
Login to View More