A transaction risk identification method, device, and computer equipment
A risk identification and transaction technology, applied in the field of data processing, can solve the problems of low discrimination, high user interruption rate, affecting user experience, etc., to achieve the effect of ensuring security, reducing interruption rate, and ensuring payment experience
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
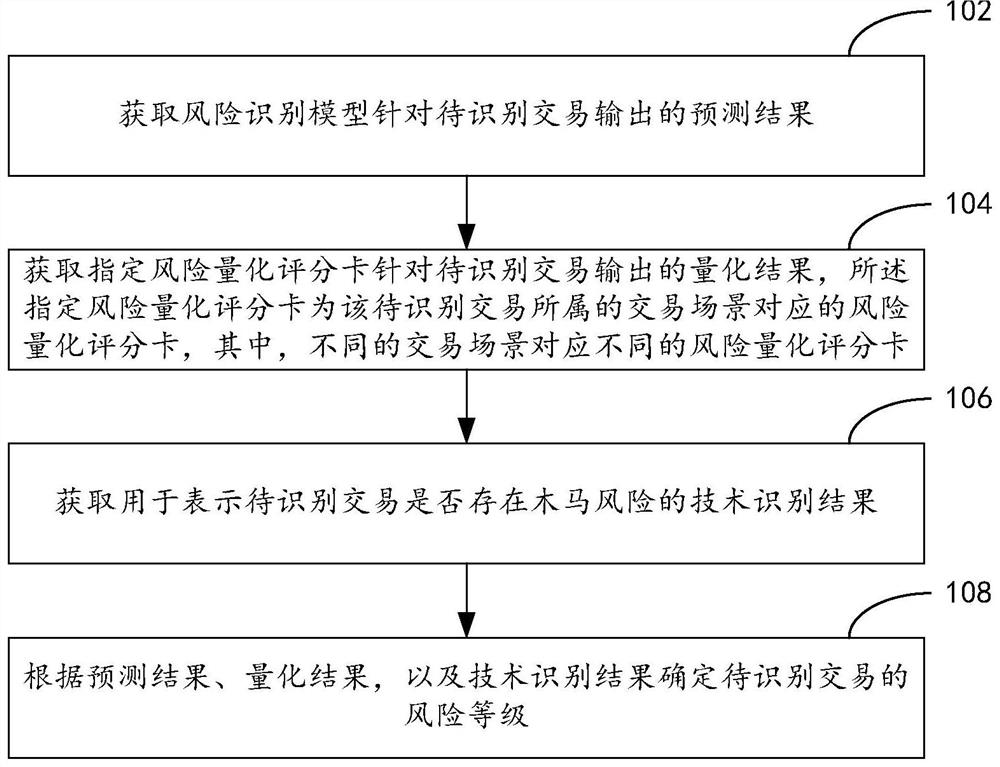
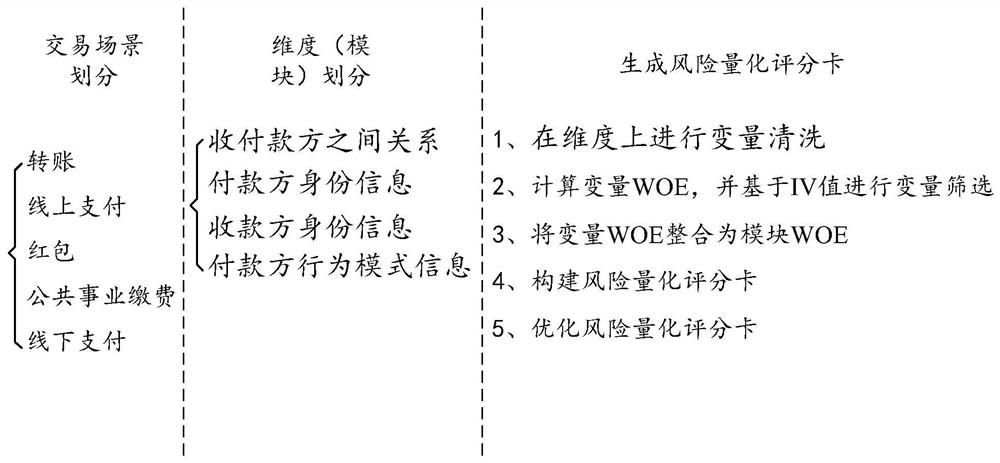
[0025] In order for those skilled in the art to better understand the technical solutions in the embodiments of the present specification, the technical solutions in the embodiments of the present specification will be described in detail below with reference to the accompanying drawings in the embodiments of the present specification. Obviously, the described implementation Examples are only some of the embodiments of the present specification, but not all of the embodiments. All other embodiments obtained by those of ordinary skill in the art based on the embodiments in this specification should fall within the scope of protection.
[0026] In the risk control system, the implementation of anti-theft for user fund accounts is the top priority. Through the analysis of historical fund embezzlement incidents, it can be found that a type of fund embezzler, after stealing the user's identity information and fund account information, uses his own mobile phone or computer equipment...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More