[0005] However, the traditional role-based user
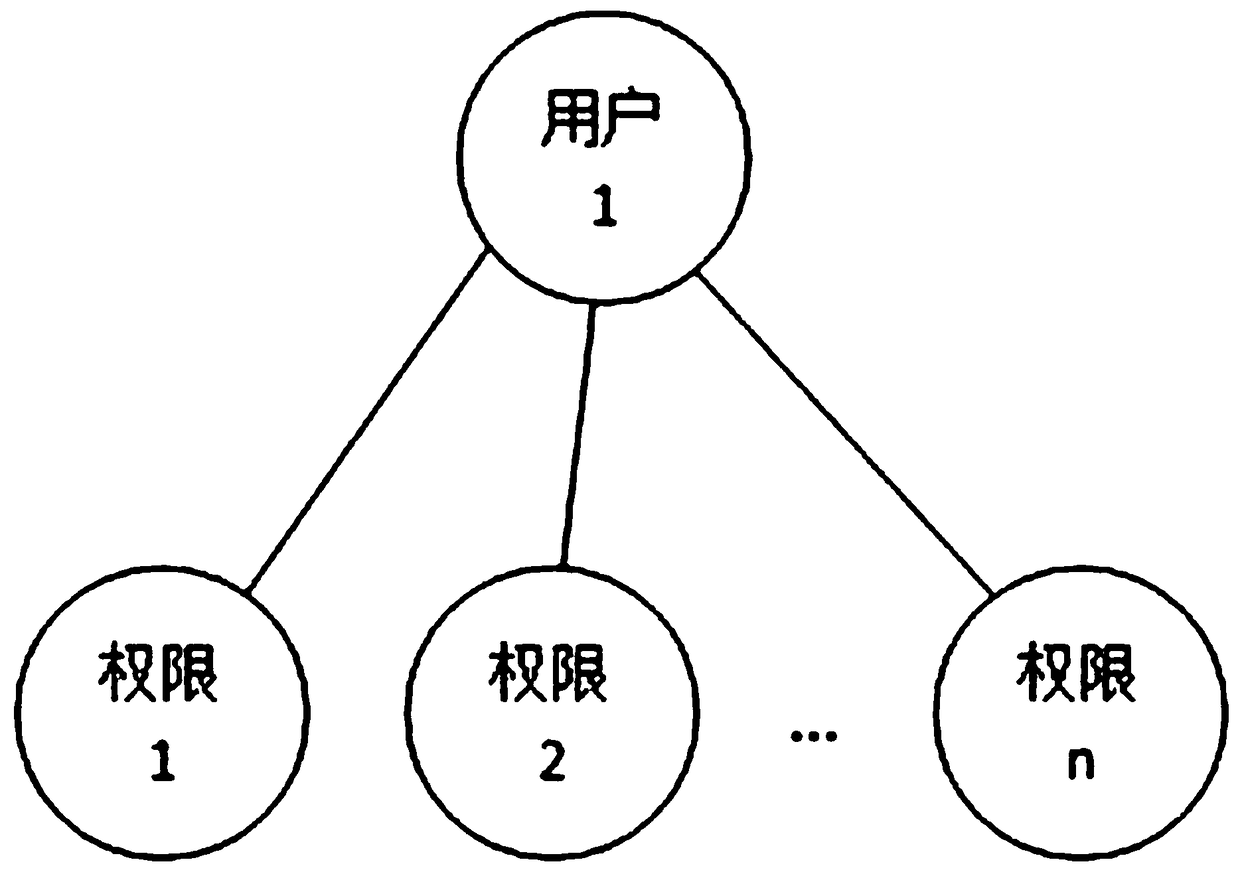
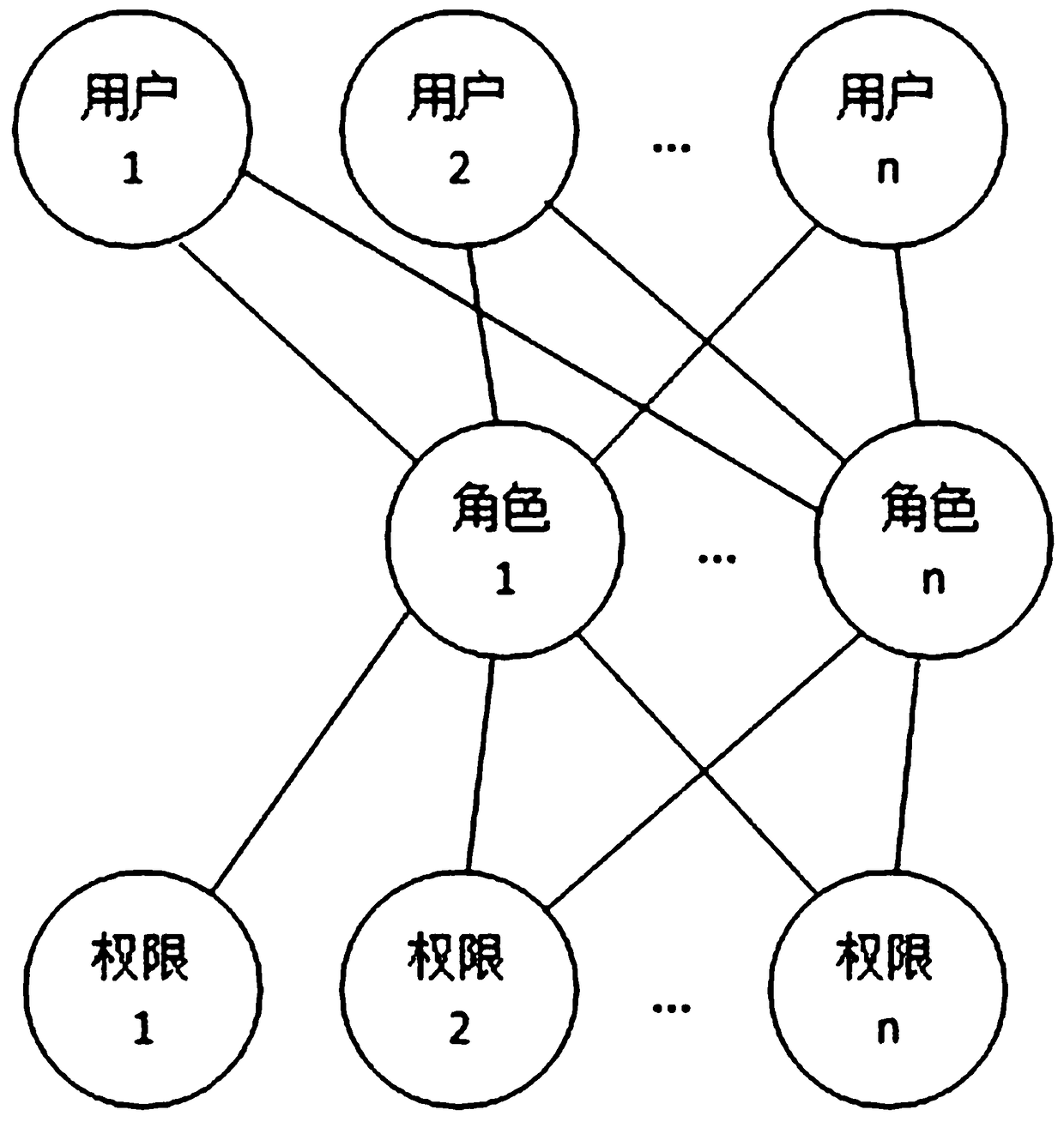
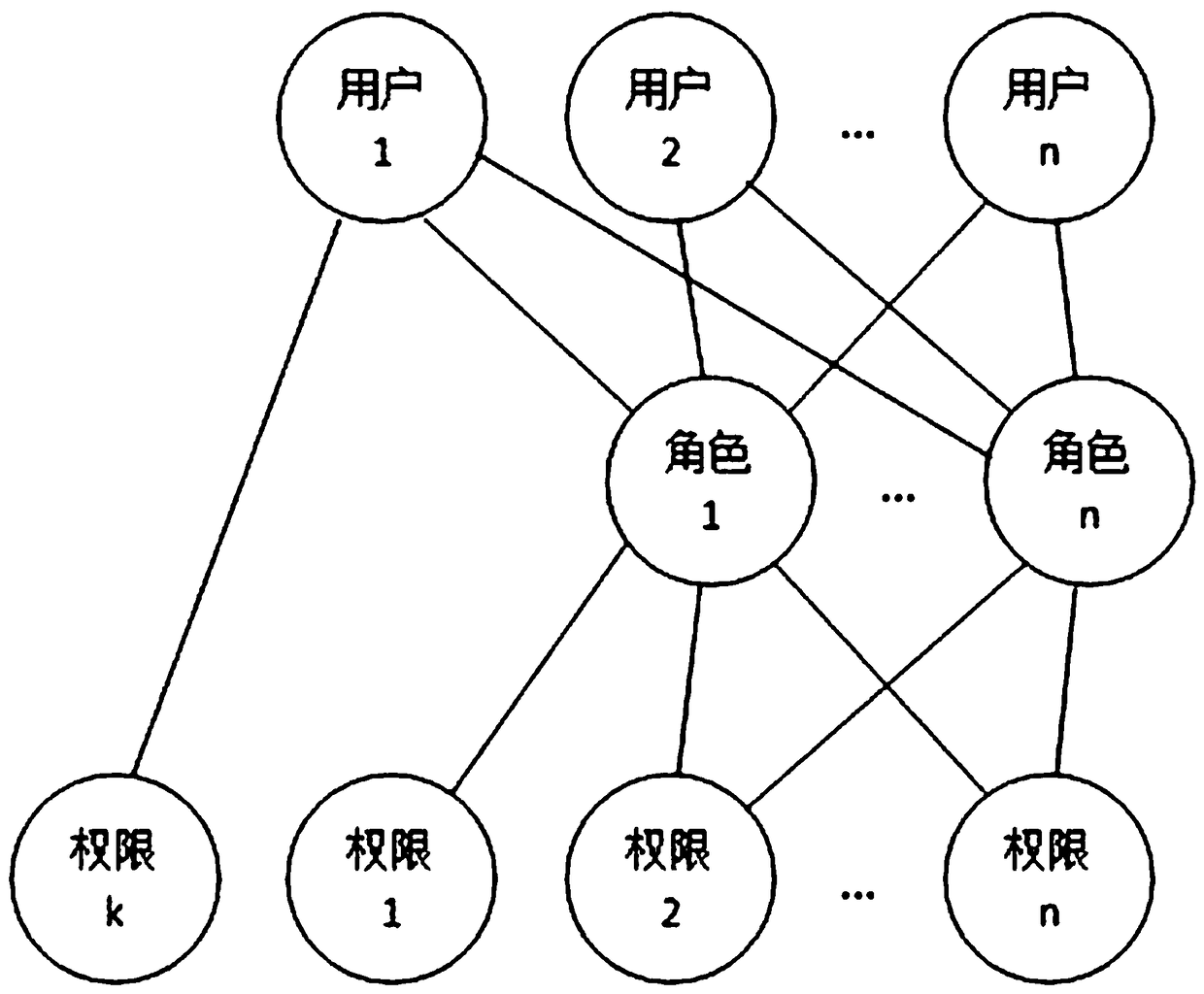
rights management methods all adopt the "role-to-user one-to-many" association mechanism. / Position / Position / Type of work and other concepts, the authorization of user rights under this association mechanism is basically divided into the following three forms: 1. figure 1 As shown, directly authorizing users has the disadvantages of heavy
workload, frequent and cumbersome operations; 2. figure 2 As shown, authorize the role (class / group / post / job / type of work) (a role can be associated with multiple users), and the user obtains the authority through the role; 3. For example image 3 As shown, the combination of the above two methods
[0006] In the above statement, both 2 and 3 need to authorize the role of class / group nature, but the way of authorization through the role of class / group / post / work type has the following disadvantages: 1. The operation is difficult when the user authority changes: In the actual
system use, it is often necessary to adjust the user's permissions during the operation process. For example, when dealing with changes in employee permissions, the permissions of an employee associated with a role change. We cannot Changes to change the permissions of the entire role, because the role is also associated with other employees whose permissions have not changed
The above two
processing methods not only take a long time to authorize the role in the case of many role permissions, but also are prone to mistakes. The operation of the user is cumbersome and troublesome, and it is also easy to make mistakes and cause losses to the
system user.
[0007] 2. It is difficult to remember the specific permissions contained in the role for a long time: If the role has many permission function points, it is difficult to remember the specific permissions of the role over time, and it is even more difficult to remember the permission differences between roles with similar permissions. To associate a new user, it is impossible to accurately determine how to choose the association
[0008] 3. Due to the change of user permissions, more and more roles will be created (if no new roles are created, the direct authorization to users will be greatly increased), and it is more difficult to distinguish the specific differences between the permissions of each role
[0009] 4. When transferring a post, if you want to assign many permissions of the transferred user to several other users, you must distinguish these permissions of the transferred user during
processing, and then create roles to associate with the other users. users, such an operation is not only complicated and time-consuming, but also prone to errors
[0010] In traditional ERP and other management
software systems, after employees / users have obtained the permission to view their own operation records, employees / users can view all their own operation records, but in some cases it will lead to the disclosure of company information
For example, after Zhang San is transferred from the sales manager to the production director, Zhang San will not be involved in viewing the sales approval operation records after being transferred to the production director. However, since Zhang San has the authority to view his own approval operation records, Zhang San can still I checked the approval operation records (such as sales contract approval records) when I was a sales manager before, but the company was unable to take effective restrictive measures at this time (if Zhang San is not granted the permission to view his own approval operation records, it will lead to other Unable to view the approval operation record of himself as the production director, which made Zhang San unable to work normally), which led to the leakage of company information
For another example, when an employee A is temporarily transferred to investigate the operation records of another employee B for a certain period of time, it is necessary to authorize the employee A to view the operation records of employee B. After obtaining the authorization, the employee A can view the employee All operation records of employee B, resulting in the leakage of operation records other than the operation records that need to be investigated in all operation records of employee B
It can be seen from this that the existing authorization method for viewing authority of operation records cannot effectively control the authority in some cases, which is not conducive to the
confidentiality of the company's information and is likely to cause losses to the company
[0011] The traditional authorization method for viewing operation records cannot use the method / rule of "association time between roles (authorization objects / viewing objects) and their current associated users as the
reference time point" to set a dynamic viewing permission time period
For example: If an enterprise wants to use the associated time as a
reference time point to set a viewing time period to authorize a role to view the operation records of certain roles, but the associated time is dynamic (many factors such as employee entry, job transfer, resignation, etc., make The role associated with the corresponding user will change, which will make the association time uncertain), all traditional methods do not have a solution for the dynamic authorization time period; but this application method can solve it very well
 Login to View More
Login to View More  Login to View More
Login to View More