Key heterogeneous defense method
A key, heterogeneous technology, applied in the field of network security, can solve the problem of too much cache of the clock controller, and achieve the effect of increasing the difficulty of attack, increasing uncertainty, and increasing the difficulty of attack.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0024] The present invention will be described in detail below in conjunction with specific embodiments. The following examples will help those skilled in the art to further understand the present invention, but do not limit the present invention in any form. It should be noted that those skilled in the art can make several modifications and improvements without departing from the concept of the present invention. These all belong to the protection scope of the present invention.
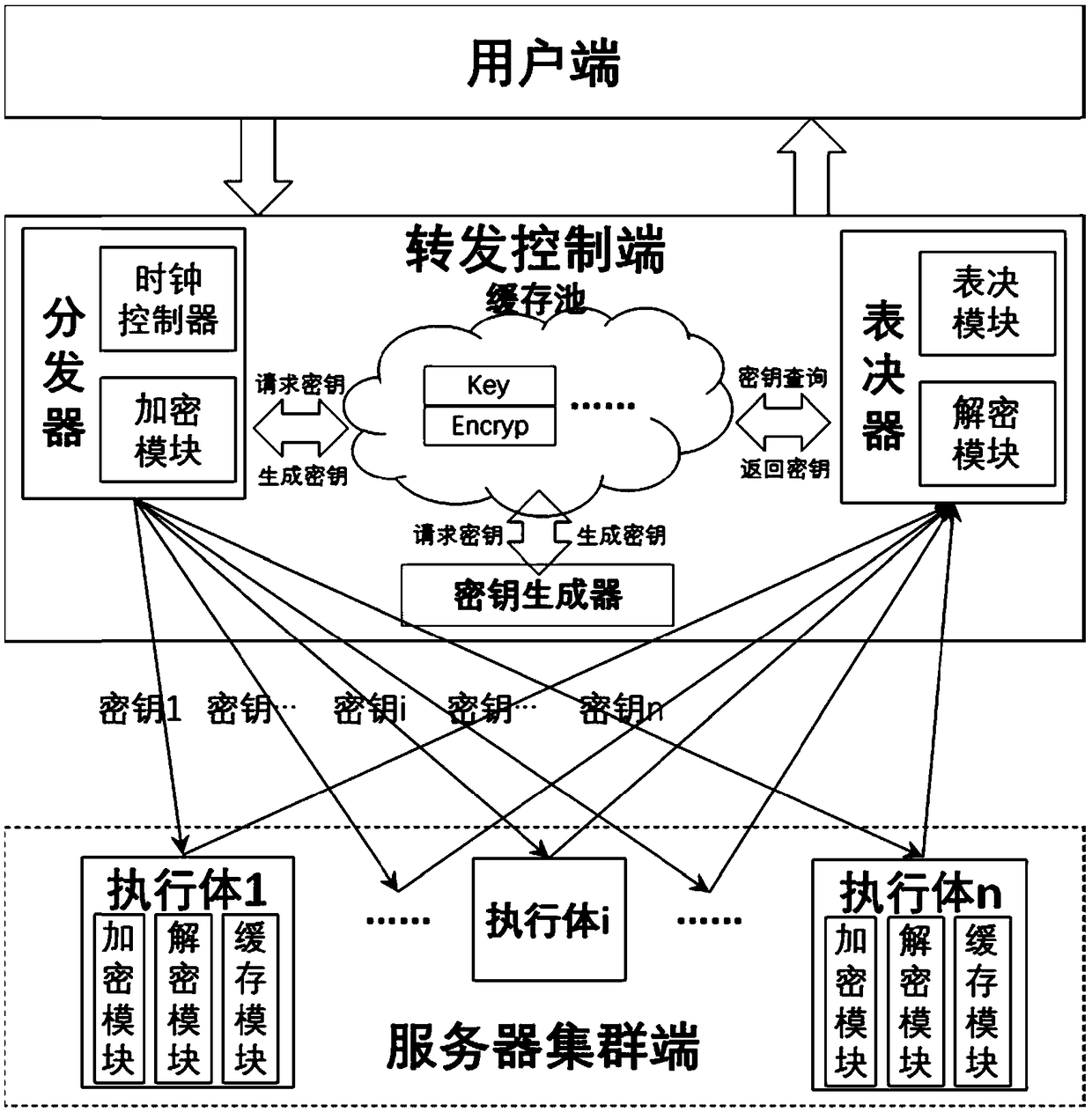
[0025] A key heterogeneous defense method, involving the user end, the forwarding control end and the server cluster end, such as figure 1 shown.
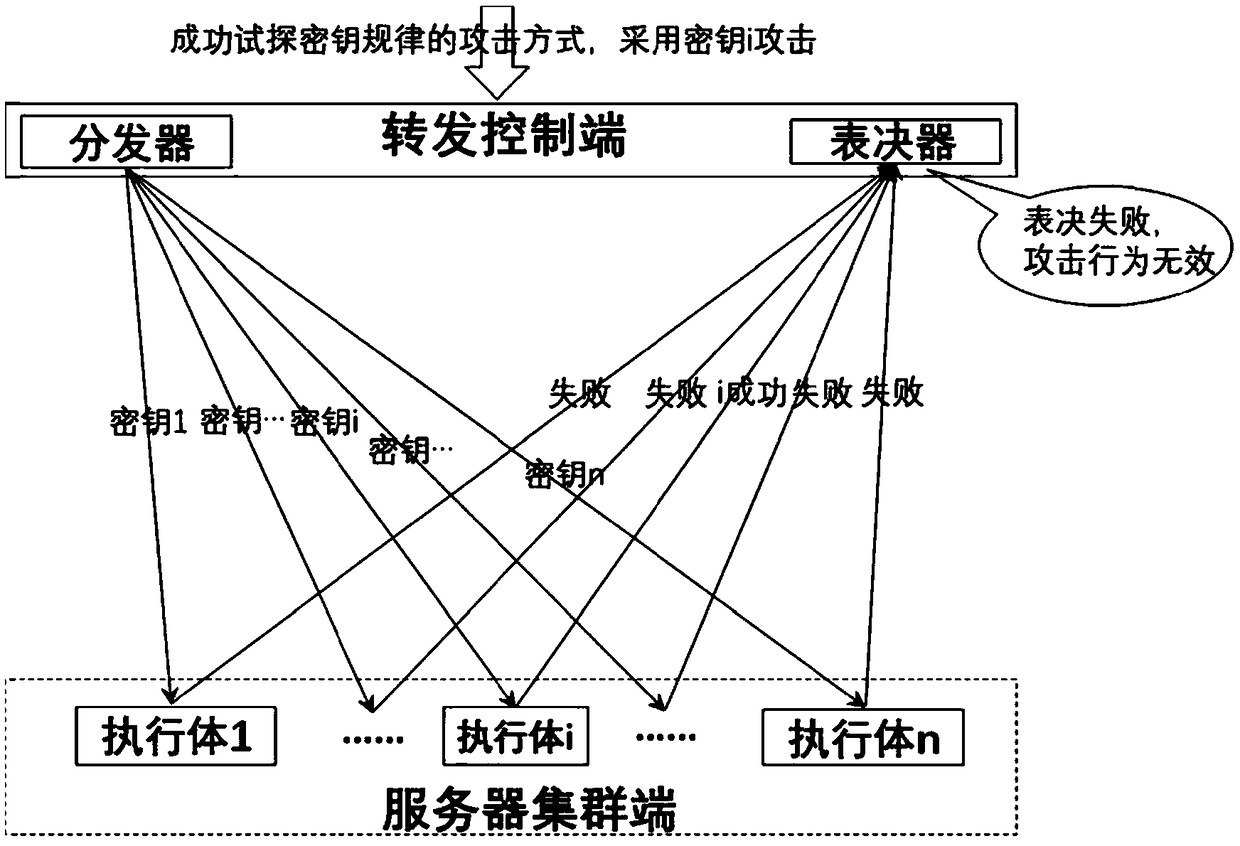
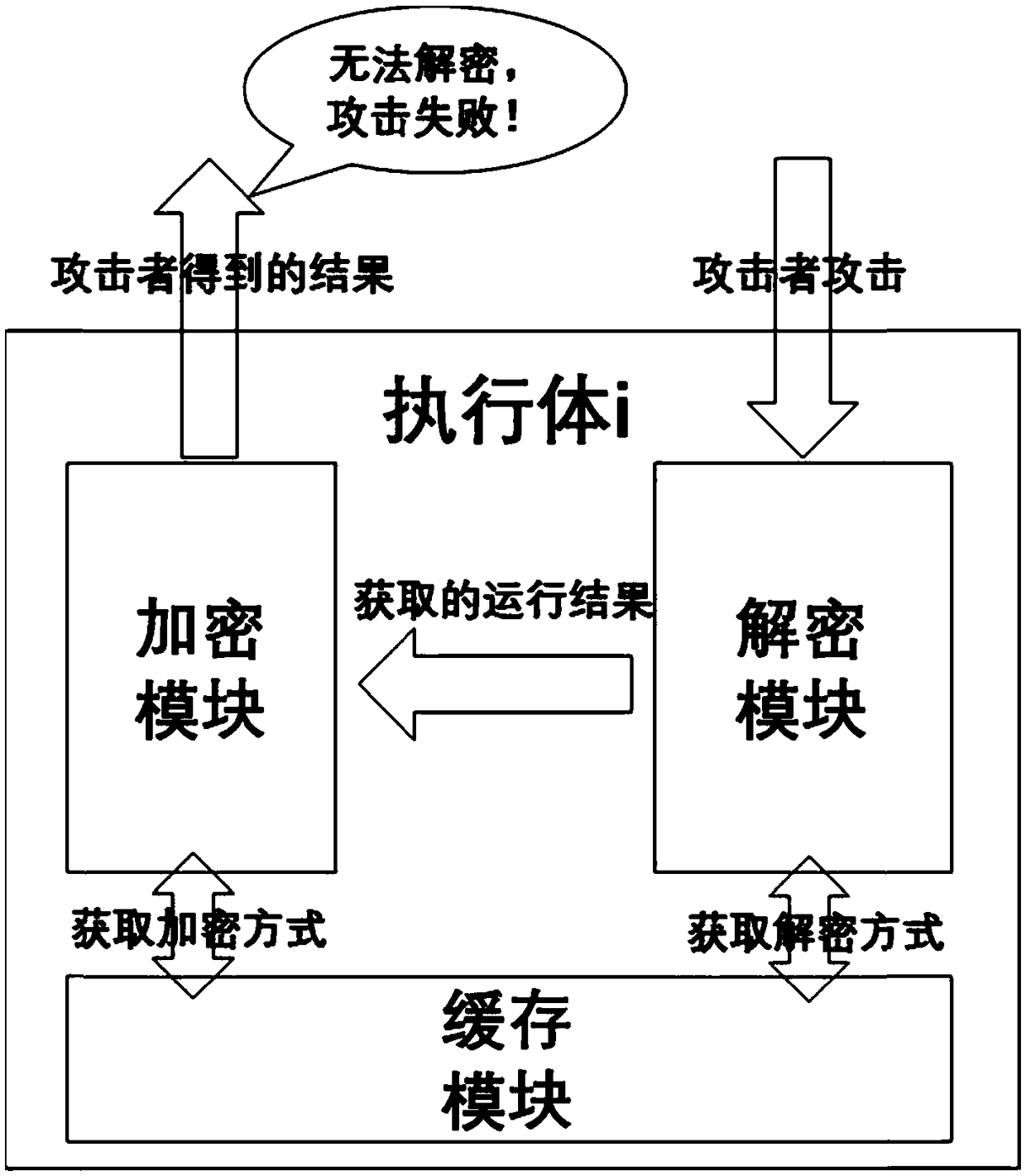
[0026] The forwarding control terminal includes a distributor, a cache pool, a key generator and a voter; after receiving a user request, the forwarding control terminal will encrypt the request information in different ways and distribute it to Different executives on the server cluster side; the forwarding control end can also process the results re...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More