Threat intelligence oriented security knowledge graph construction method and system
A technology of security knowledge and construction method, applied in the field of computer network security, can solve the problems of multi-source heterogeneity of threat intelligence, weak information analysis ability, etc., and achieve the effect of improving analysis ability
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0031] In order to enable those skilled in the art to better understand the technical solutions in the embodiments of the present invention, and to make the purpose, features and advantages of the present invention more obvious and easy to understand, the technical core of the present invention will be further described in detail below in conjunction with the accompanying drawings and examples instruction of.
[0032] In the present invention, a threat intelligence-oriented security knowledge graph system is designed, which can effectively solve the above-mentioned problems. The system includes the following:
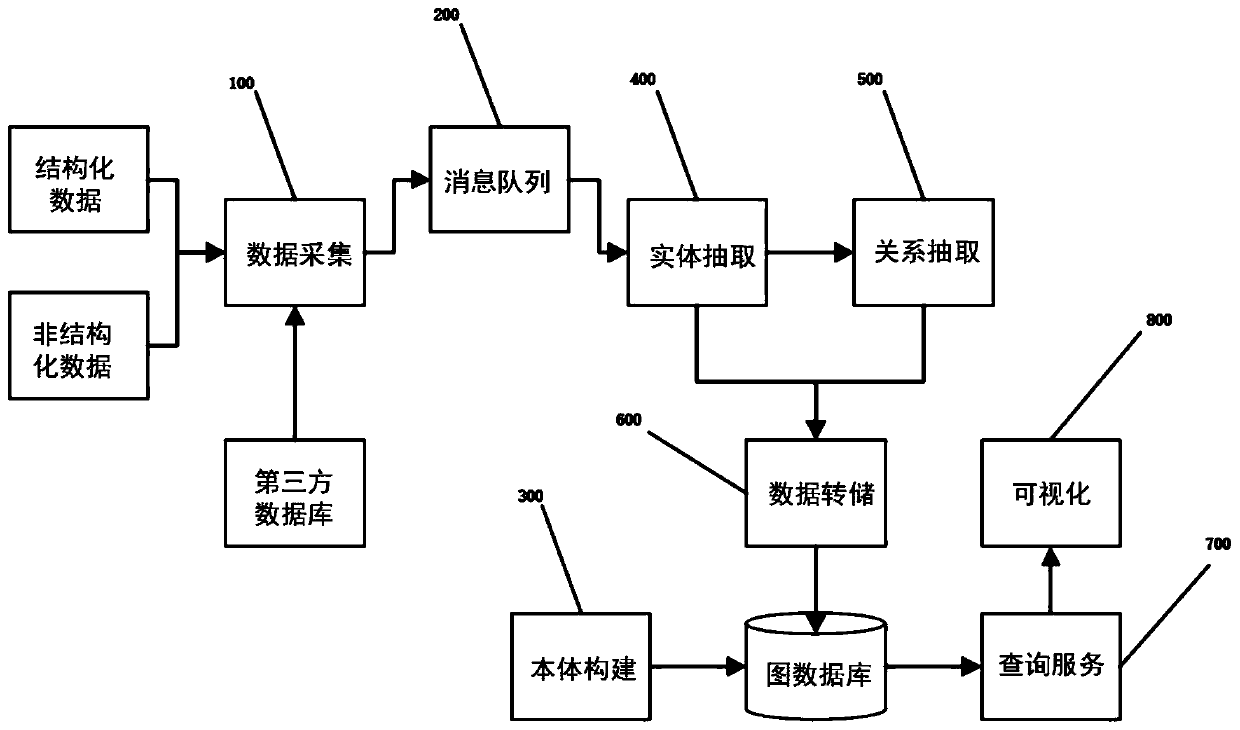
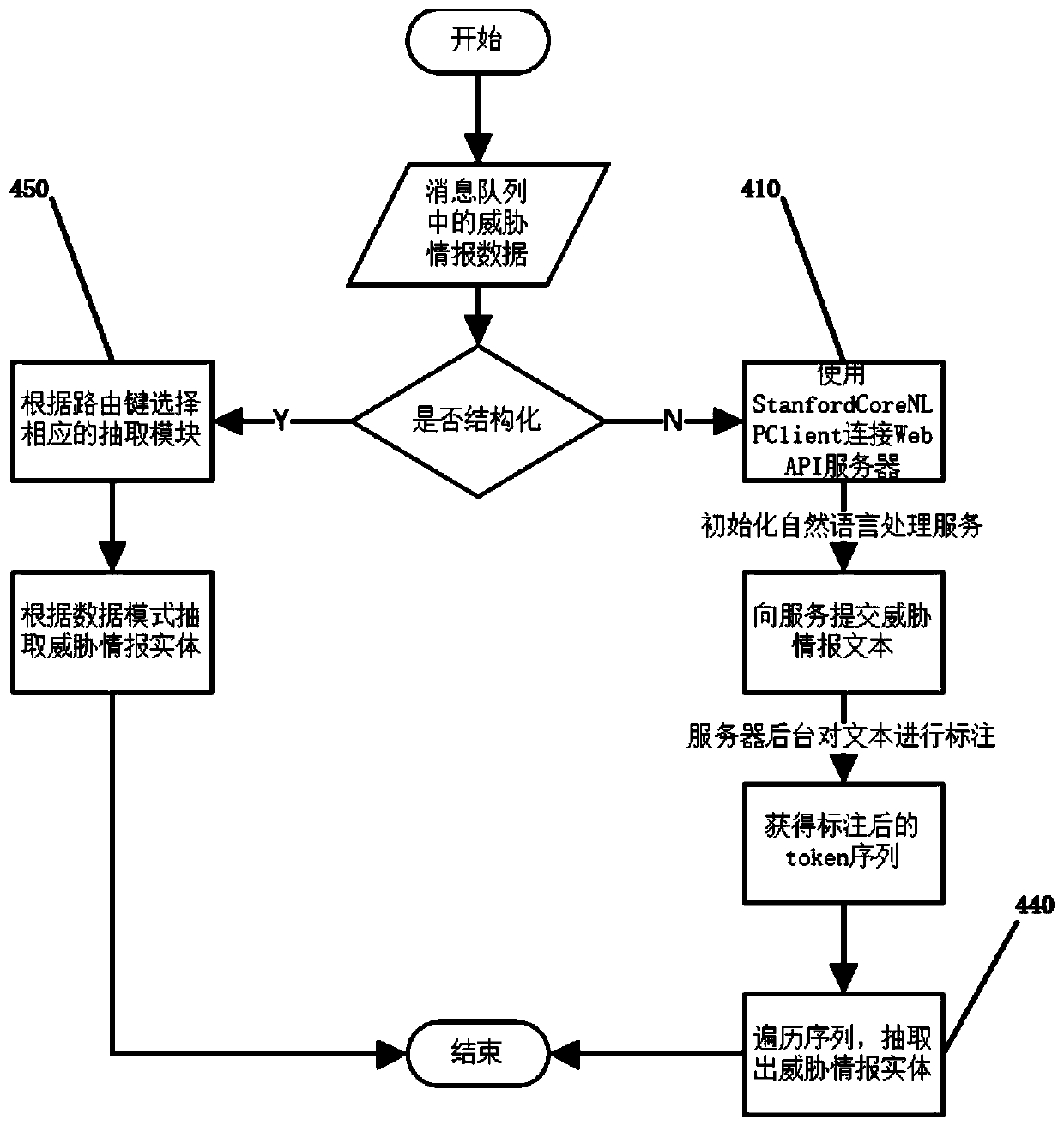
[0033] Such as figure 1 Shown is the overall flow chart of the security knowledge graph system. The data collection module 100 collects threat intelligence data from the network, routes it to the knowledge extraction module (including the entity extraction module 400 and the relationship extraction module 500) through the corresponding message queue module 200, and ext...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More