Data security processing method based on big data
A processing method and data security technology, applied in the field of data security, can solve the problems of no cloud service security, no information security, etc., and achieve the effect of improving the flexibility of adjustment, improving security, and ensuring security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0024] The present invention will be described in detail below in conjunction with the accompanying drawings and specific embodiments, wherein the schematic embodiments and descriptions are only used to explain the present invention, but are not intended to limit the present invention.
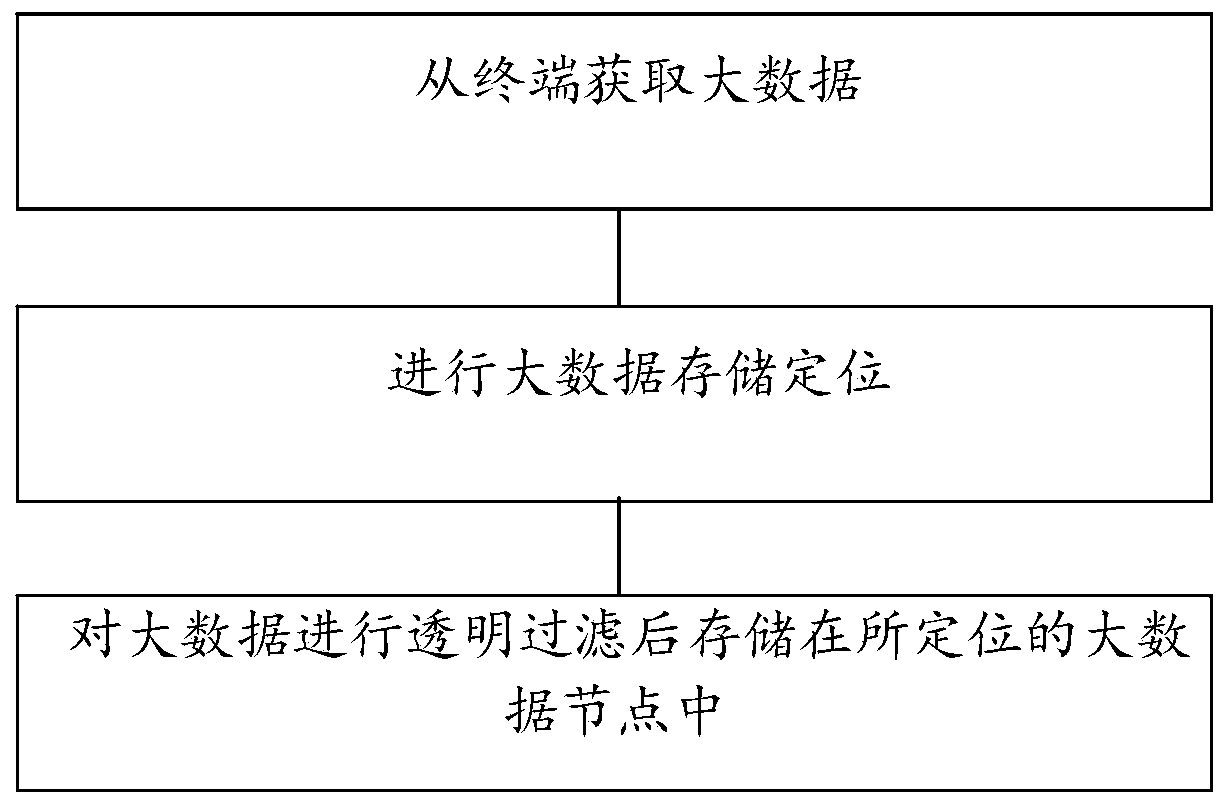
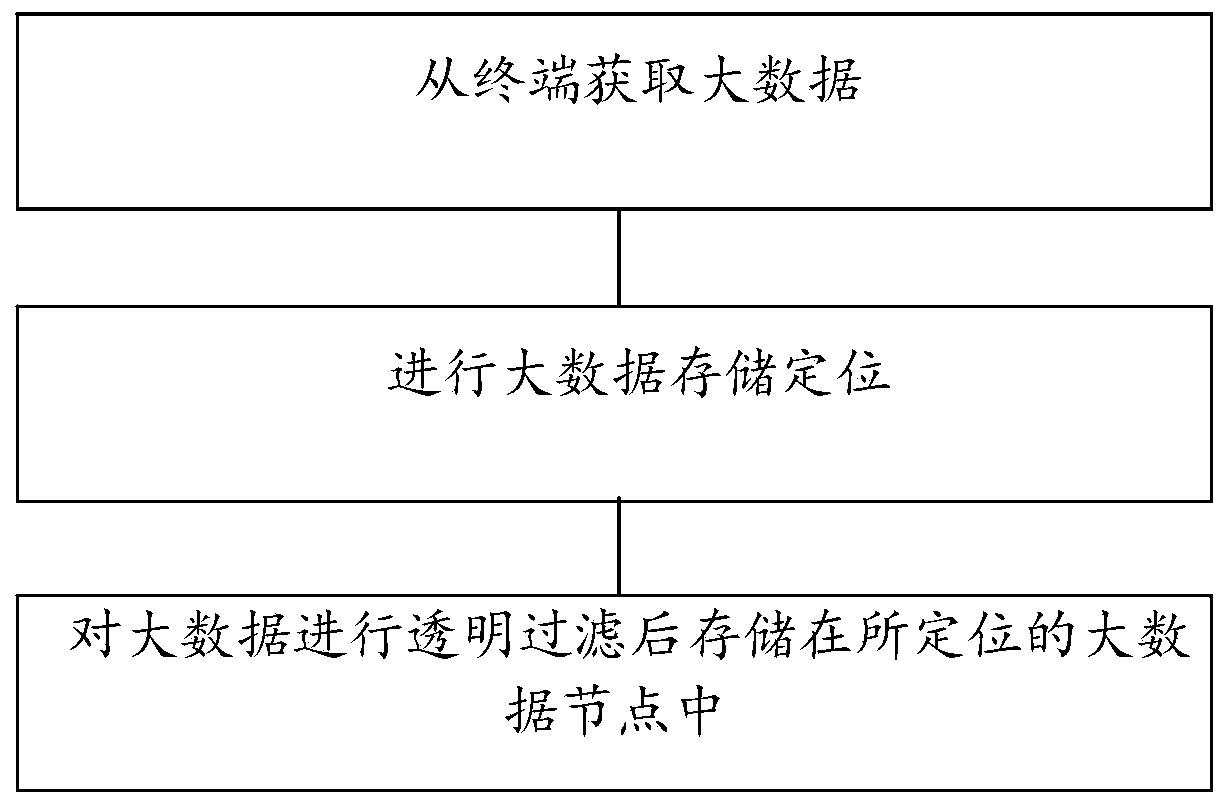
[0025] A method of data security processing based on big data applied in the present invention is described in detail, as shown in the attached figure 1 As shown, the method includes:
[0026] Step S1: Acquire big data from the terminal; specifically: acquire big data according to the processing target of acquiring big data; for example: the processing target of big data is the target of processing the collected big data; the processing target includes Processing steps, credibility, requirements, security requirements, processing result types, processing types, etc.; for example, if big data users and demanders have requirements for the credibility of big data, data with low credibility will n...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More