An attack graph-based method for automatic generation of cloud outsourcing service data leakage security test cases
A technology of security testing and outsourcing data, applied in the field of cloud computing security, can solve problems such as leak test case automation, achieve the effect of ensuring comprehensiveness and improving construction efficiency
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0090] The present invention will be further described below in conjunction with the accompanying drawings and specific embodiments.
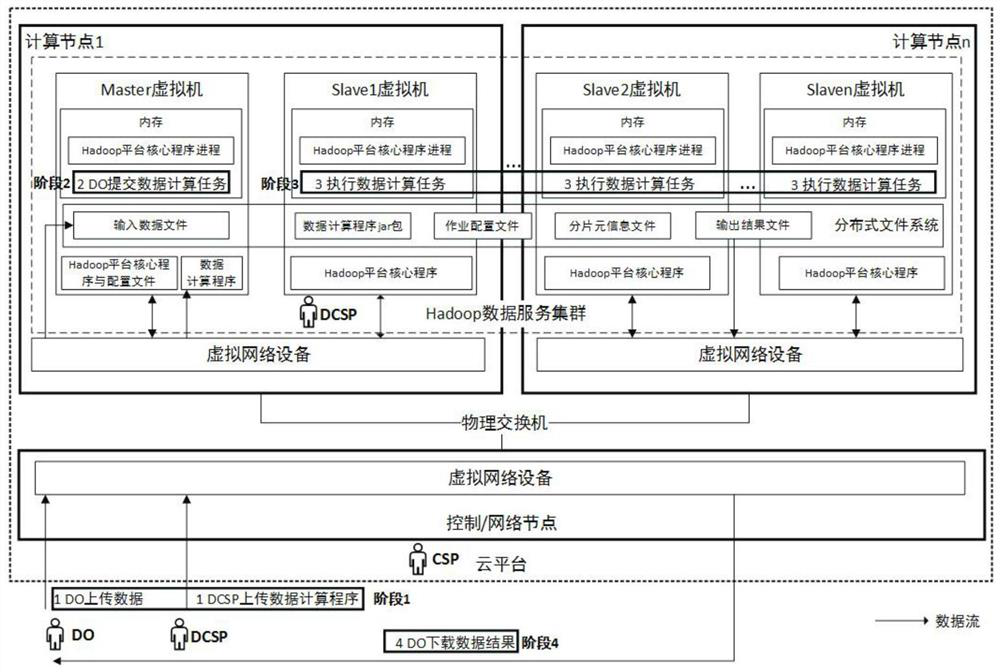
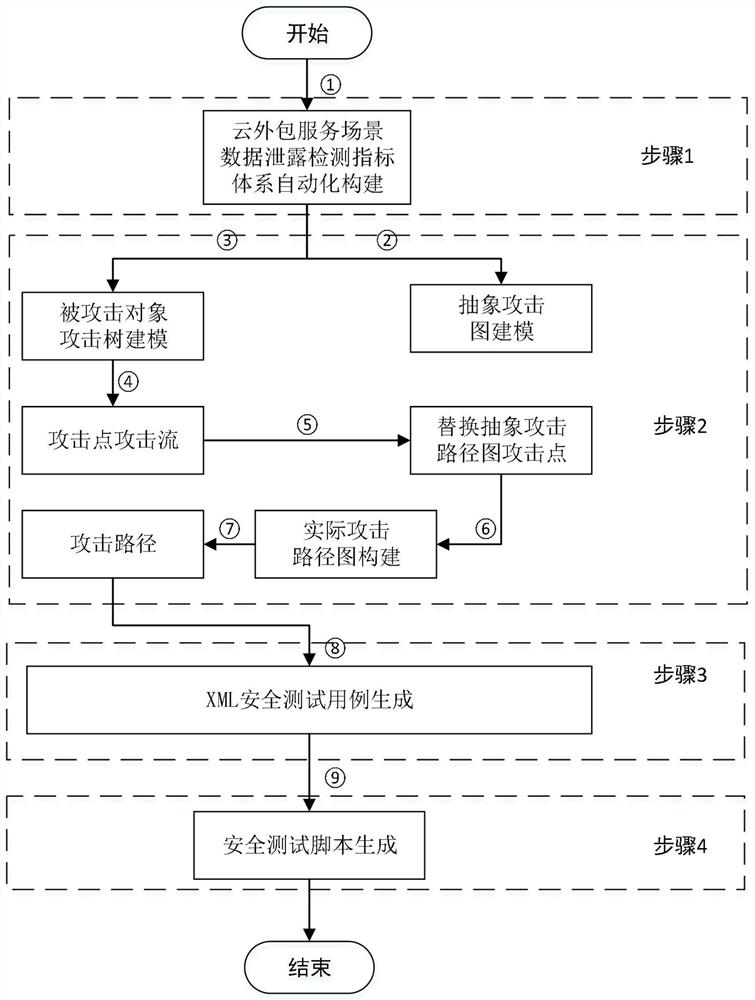
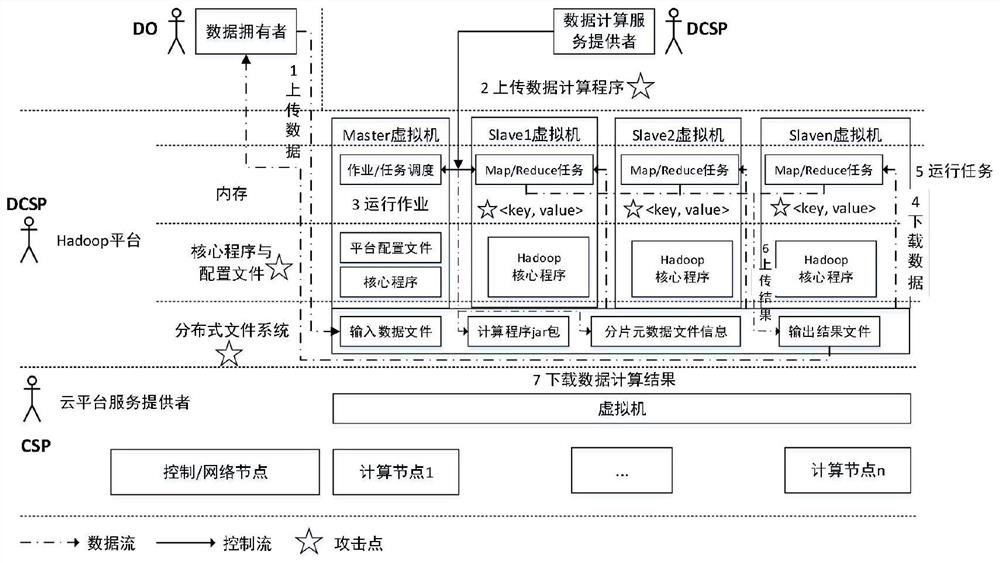
[0091] The present invention mainly uses DCSP to deploy Hadoop distributed data service clusters in OpenStack cloud platform virtual machines as an example to illustrate the execution process of the automatic generation method of cloud outsourcing service data leakage security test cases based on attack graph, but is not limited to deploying distributed data on other cloud platforms. big data service platform. Specific steps are as follows:
[0092] 1. A method for generating data leakage detection indicators in the life cycle of cloud outsourcing data services based on data flow analysis. The specific implementation steps are:
[0093] First of all, analyze the key points of data flow, data location, attacked object and attack role in this scenario, and realize the automatic construction of cloud outsourcing data service data leakage detectio...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More