Application security hardening method and device
An application program and security technology, which is applied in the computer field, can solve the problems of inability to implement batch maintenance of program reinforcement methods, waste of system resources, and high maintenance costs, and achieve the effects of easy batch maintenance, prevention of reverse analysis, and low maintenance costs
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0024] The following will refer to the accompanying drawings to describe in more detail the exemplary embodiments of the present disclosure. Although exemplary embodiments of the present disclosure are shown in the accompanying drawings, it should be understood that the present disclosure may be implemented in various forms and should not be limited by the embodiments described herein. Instead, these embodiments are provided in order to be able to more thoroughly understand the present disclosure, and to be able to communicate the scope of the present disclosure completely to those skilled in the art.
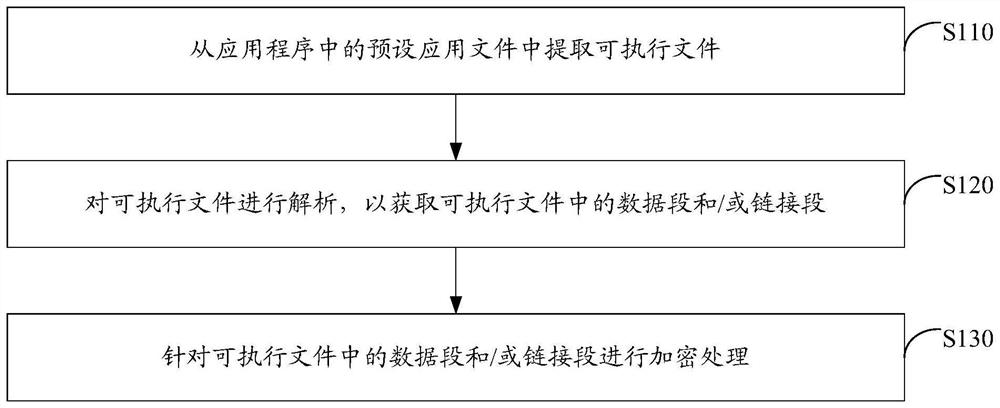
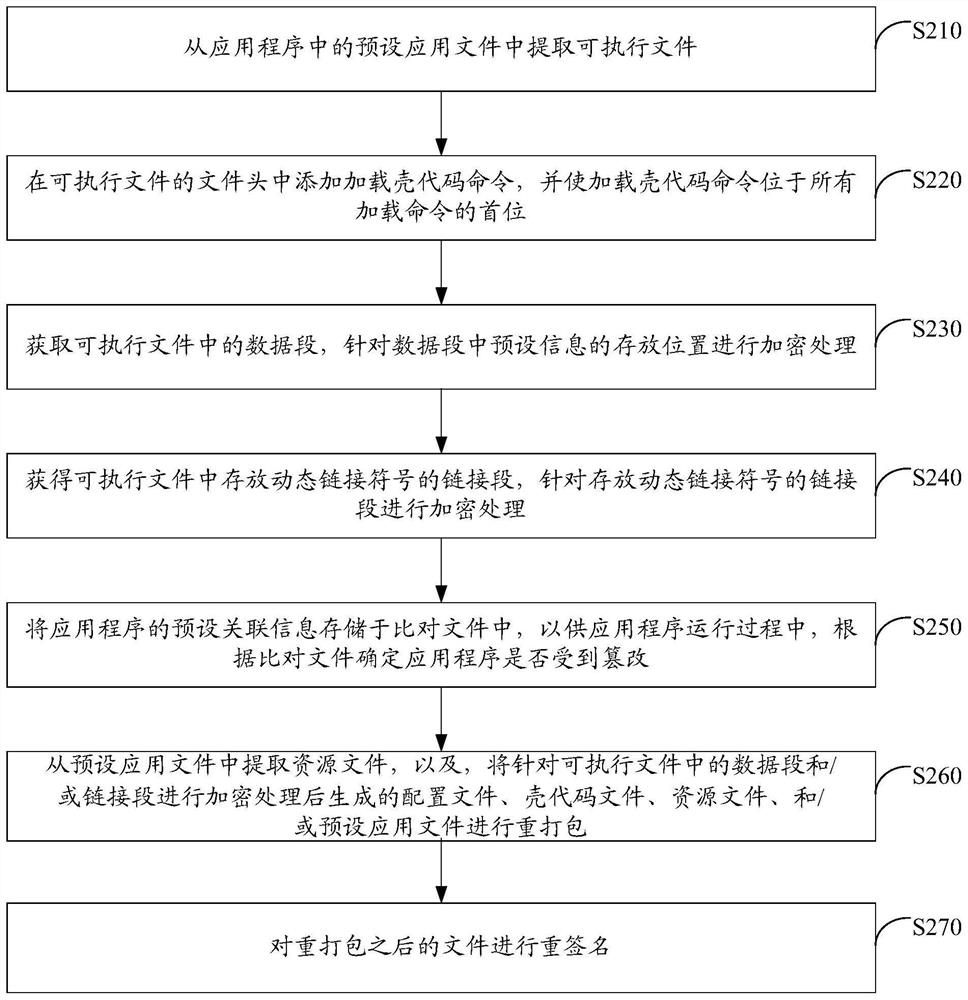
[0025] Figure 1 A schematic diagram of an application security hardening method provided according to one embodiment of the present invention is shown. Wherein, the application security hardening method provided in the present embodiment may be applied to IOS and / or MachOS systems. as Figure 1 As shown, the method comprises:
[0026] Step S110, extract the executable file from...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More