A privacy protection based blockchain design method
A design method and privacy protection technology, applied in the field of information security, can solve problems such as false accounts
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0028] In order to make the purpose, technical solution and advantages of the present invention more clear, the present invention will be further described in detail below in conjunction with the accompanying drawings and embodiments. It should be understood that the specific embodiments described here are only used to explain the present invention, not to limit the present invention.
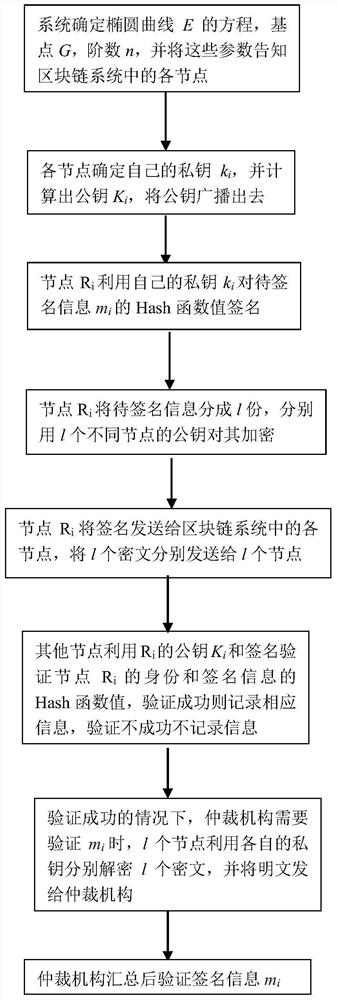
[0029] Such as figure 1 As shown, it is a privacy protection-based block chain design method of the present invention, the specific content and steps are as follows:
[0030] (1) First, the blockchain system determines the equation of the elliptic curve E as y 2 =x 3 +ax+b, the base point G of the elliptic curve, the order of the elliptic curve is n, and these parameters are notified to each node in the blockchain system;
[0031] (2) Each node in the blockchain system determines its own private key k i , calculate the public key K i =k i G, and the public key K i Inform other nodes in the...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More