Log encryption method and system of Android device, equipment and medium
An encryption method and technology of an encryption system, which are applied in the field of encryption of Android device information, can solve problems such as leakage of Android device information, and achieve the effects of enhancing convenience, facilitating analysis, and enhancing reliability
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
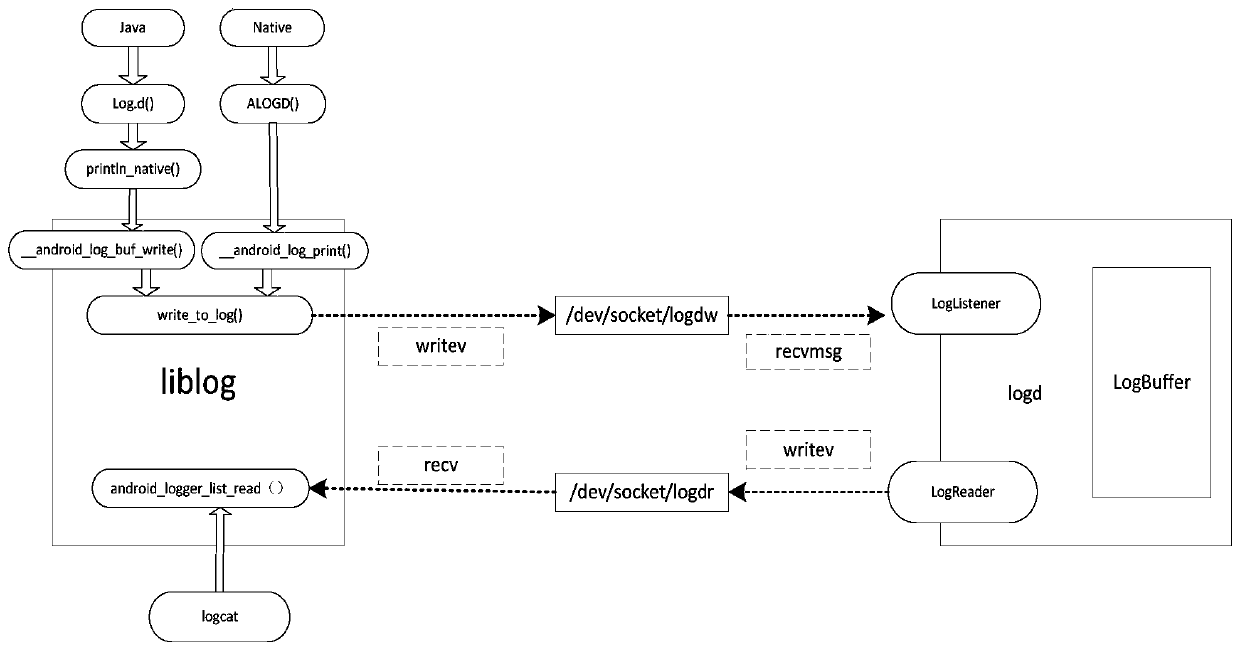
[0059] The present embodiment provides a log encryption method of an Android device, which can be specifically described as the following process:
[0060] Step S1, after the android_log_buf_write() function and __android_log_write() call the write_to_log() function, obtain the encryption algorithm through persist.sys.logarithmetic, and obtain the encryption key through persist.sys.logkey; the present invention supports SHA1, MD5, HMAC , AES, RC4, Rabbit, Base64 and other encryption algorithms. For example, to obtain the value of persist.sys.logarithmetic: 1-7, the specific meanings are as follows 1: SHA1, 2: MD5, 3: HMAC, 4: AES, 5: RC4, 6: Rabbit, 7: Base64; and the encryption key one string of 8 digits;
[0061] Step S2, encrypt the [log msg] text in plaintext format through the encryption algorithm and encryption key into ciphertext; the general default output log format is FORMAT_BRIEF:[time][log priority] / [tag][pid][log msg ], so you only need to encrypt the stri...
Embodiment 2
[0071] A kind of log encryption system of Android device is provided in the present embodiment, comprising:
[0072] The acquisition module is used to obtain the encryption algorithm through persist.sys.logarithmetic and the encryption key through persist.sys.logkey after the android_log_buf_write() function and __android_log_write() call the write_to_log() function;
[0073] The encryption module is used to encrypt the [log msg] text in plaintext format through the encryption algorithm and encryption key into ciphertext; the general default output log format is FORMAT_BRIEF:[time][log priority] / [tag][pid][ logmsg], so you only need to encrypt the text of [log msg], because only this string of information will contain private information.
[0074] It is also used to customize the ciphertext format; the ciphertext format is: Header+Length+ciphertext+check digit+End;
[0075] in,
[0076] Header is the start bit 0x0A;
[0077] Length is the length of the ciphert...
Embodiment 3
[0083] This embodiment provides an electronic device, specifically an Android device, such as Figure 5 As shown, it includes a memory, a processor, and a computer program stored in the memory and operable on the processor. When the processor executes the computer program, any implementation manner in Embodiment 1 can be realized.
[0084] Since the electronic device introduced in this embodiment is the device used to implement the method in Embodiment 1 of this application, based on the method described in Embodiment 1 of this application, those skilled in the art can understand the electronic device of this embodiment. Specific implementation methods and various variations thereof, so how the electronic device implements the method in the embodiment of the present application will not be described in detail here. As long as a person skilled in the art implements the equipment used by the method in the embodiment of the present application, it all belongs to the protecti...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More