Distributed identity authentication method
An authentication method and distributed technology, applied in the field of distributed authentication, can solve the problems of unreliable authentication and low authentication efficiency, and achieve the effect of high authentication efficiency, reliable authentication, and reliable identity authentication.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0030] The technical solutions of the embodiments of the present invention will be clearly and completely described below in conjunction with the accompanying drawings of the present invention.
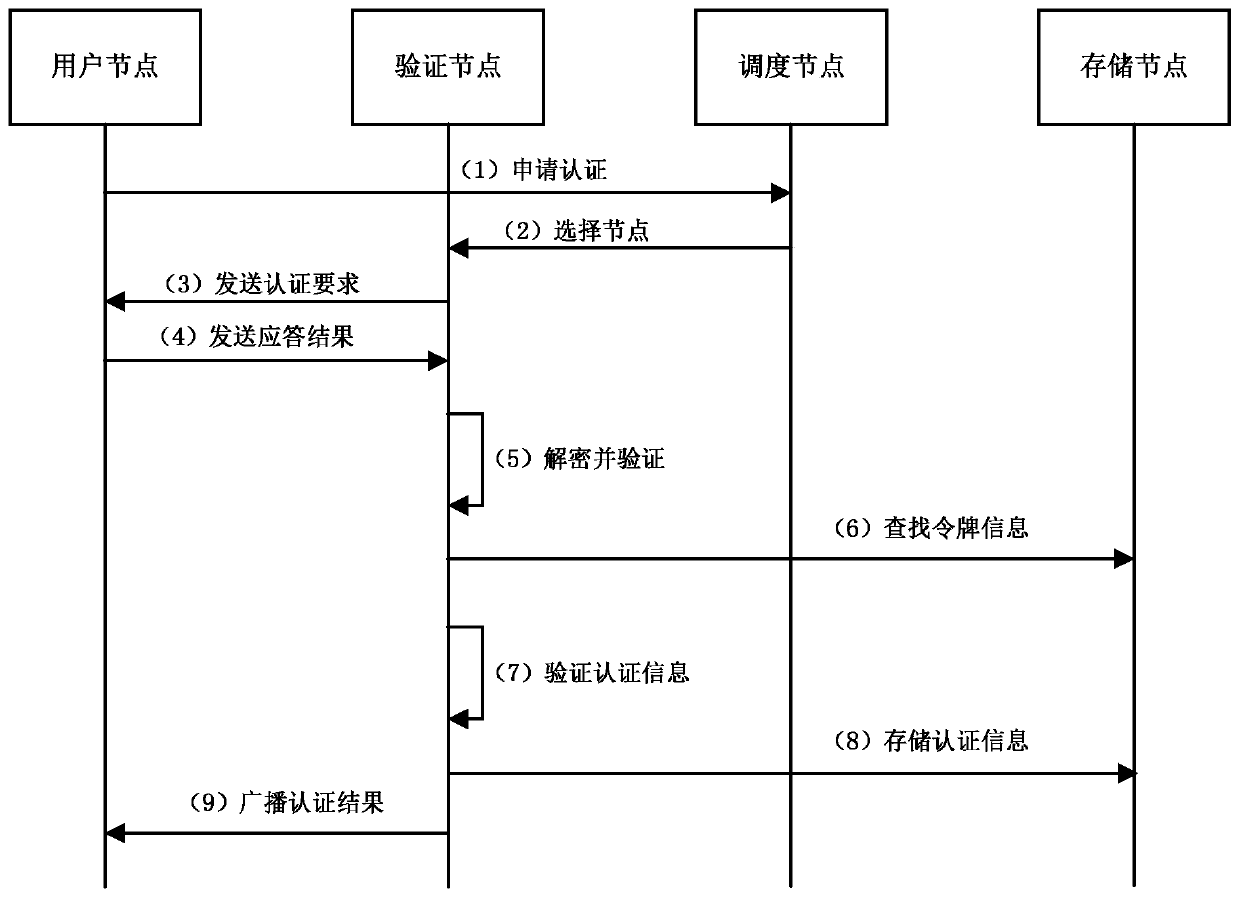
[0031] Such as figure 1 As shown, a distributed authentication method disclosed in the present invention includes the following steps:
[0032] Step S100, the user node sends an authentication request to the scheduling node, and the user node selects a verification node after receiving the authentication request;
[0033] Specifically, when performing distributed identity verification, the user node first sends an authentication request to the scheduling node, and after receiving the authentication request, the user node further selects a verification node. In this embodiment, the verification node suitable for verification is selected through the node selection algorithm, that is, the current node is selected based on whether the current node is online, network bandwidth, delay, num...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More