Security event log processing method and device and storage medium
A technology of security event and processing method, applied in the field of security event log processing method, device and storage medium, can solve the problems of neglect and incomplete analysis, and achieve the effect of improving the efficiency of security operation
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
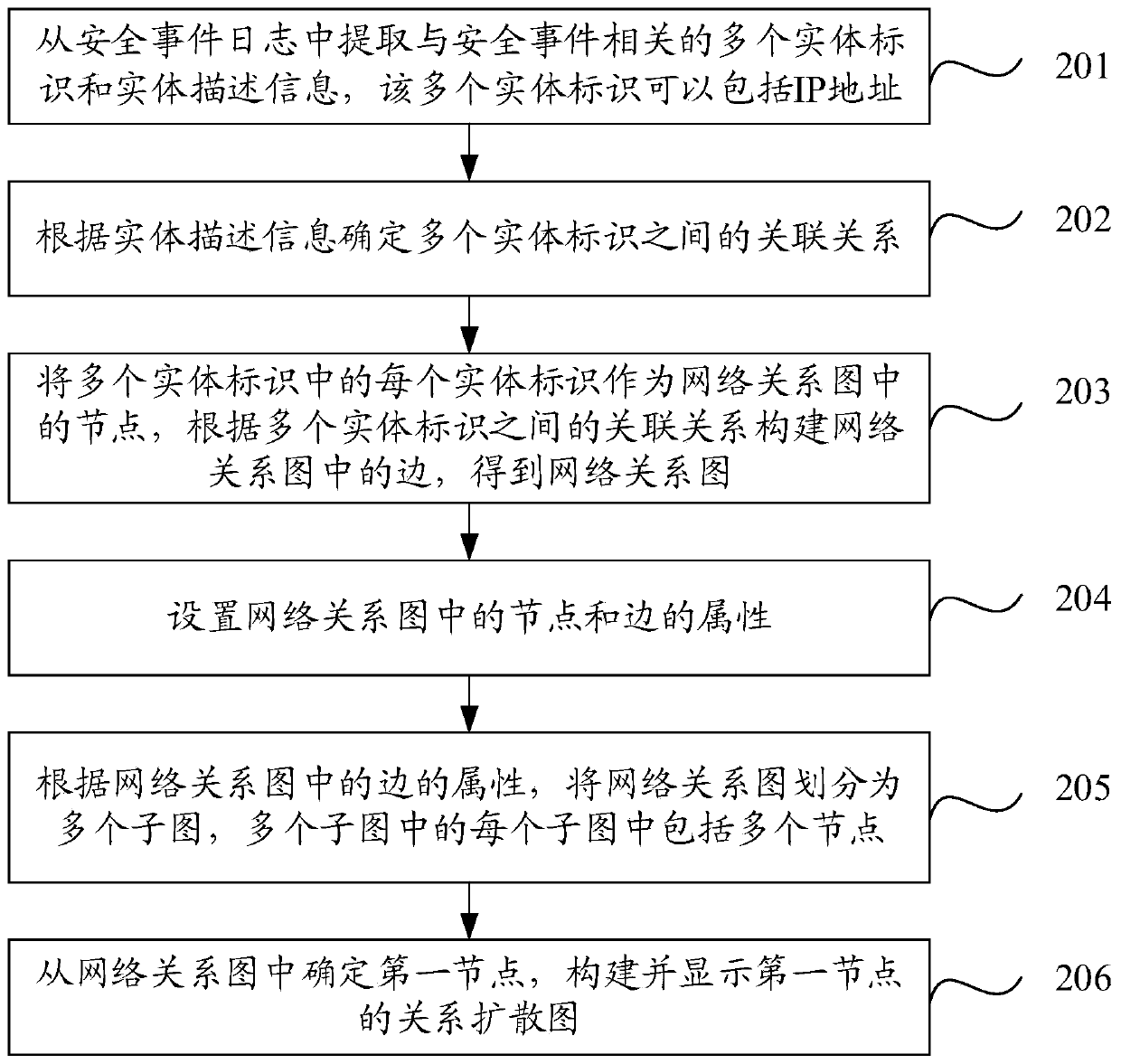
[0028] In order to make the purpose, technical solution and advantages of the present application clearer, the implementation manners of the present application will be further described in detail below in conjunction with the accompanying drawings.
[0029] Before explaining the security event log processing method provided in the embodiment of the present application in detail, the application scenario and implementation environment provided in the embodiment of the present application are firstly introduced.
[0030] Firstly, the application scenarios provided by the embodiments of the present application are introduced.
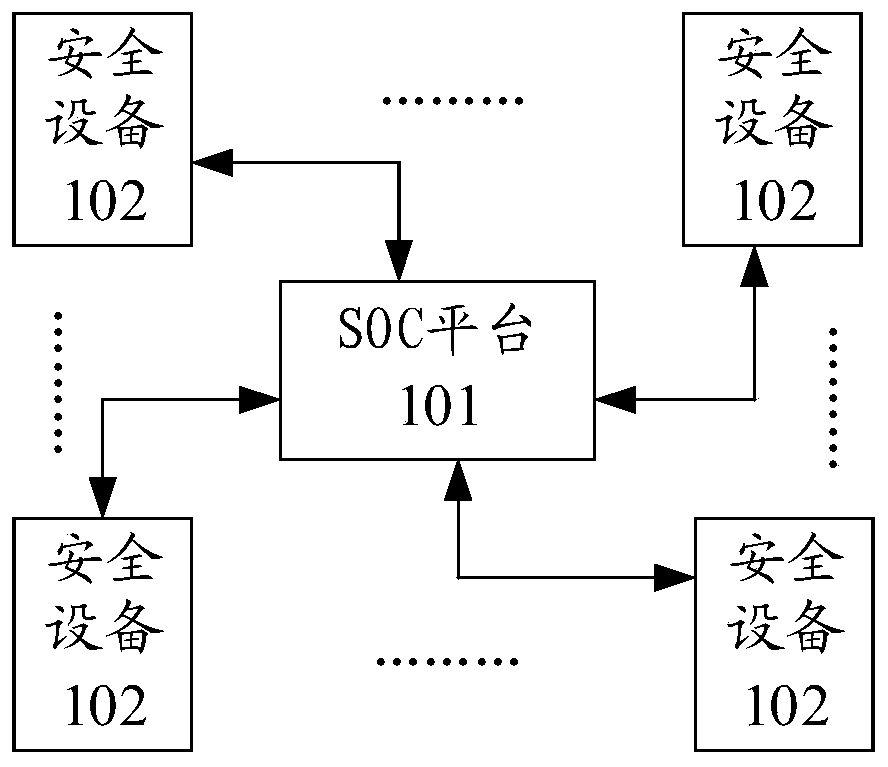
[0031] In order to protect assets and data from being leaked, enterprises usually deploy security devices at all levels to protect their assets and data, such as traffic firewalls, intrusion detection devices, virus protection devices and other security devices. Security devices can detect security threats, security problems, etc., and send them to the SO...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More