Key exchange method and device, storage medium and computing device
A key exchange and shared key technology, applied in the fields of devices and storage media, key exchange methods, and computing devices, can solve problems affecting implementation efficiency, complex algorithm design, asymmetric steps, etc., to save processing resource consumption, The algorithm design is simple and the effect of improving efficiency
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
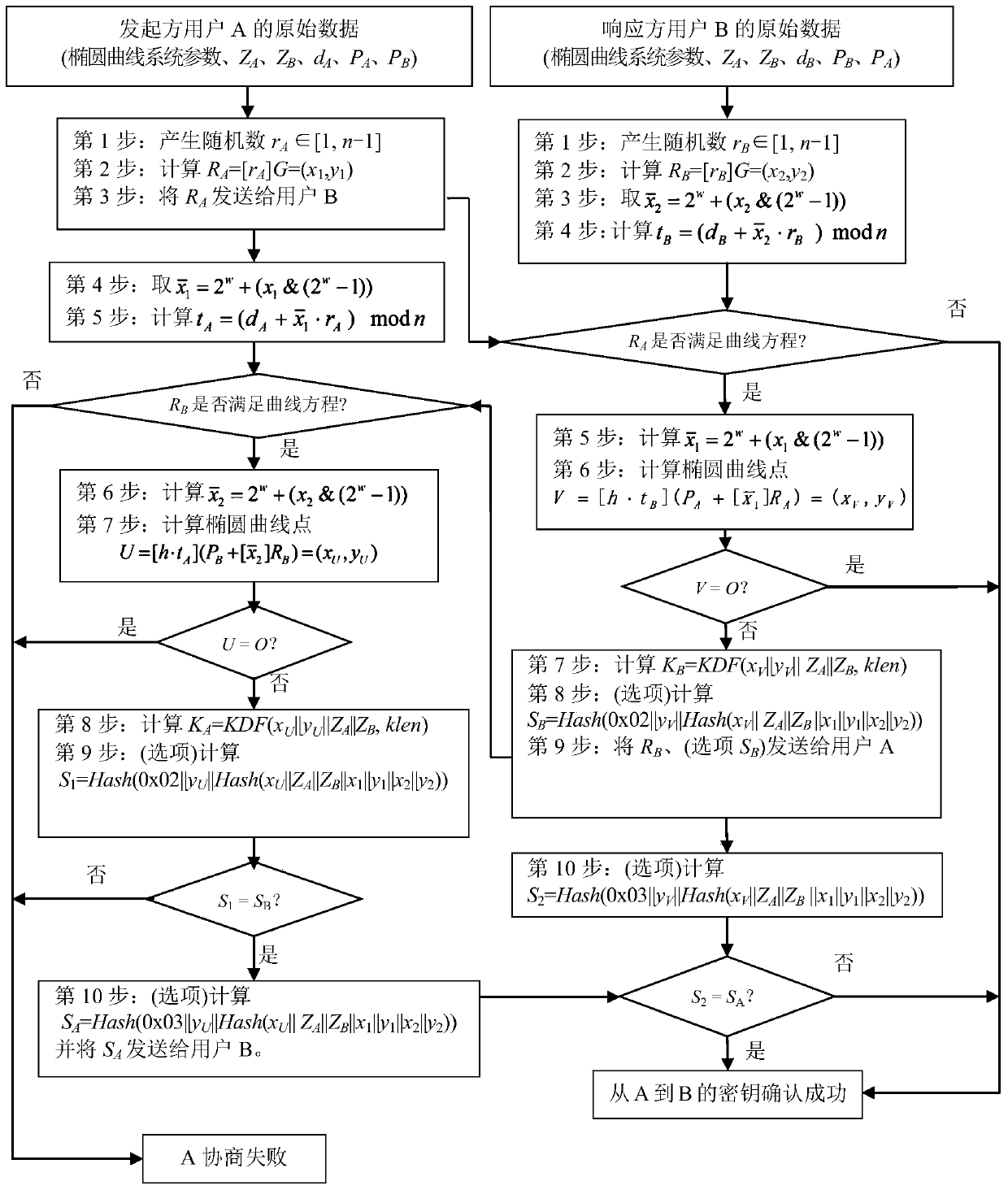
[0055] In order to make the purpose, technical solutions and advantages of the embodiments of the present invention clearer, before introducing the key exchange algorithm of the present application, first combine figure 1 Introduces the SM2 key exchange standard algorithm.
[0056] First, the symbols involved in the SM2 key exchange standard algorithm are explained:
[0057] A, B: Two users using public key cryptography.
[0058] a, b: elements in Fq, they define an elliptic curve E on Fq.
[0059] d A : User A's private key.
[0060] d B : User B's private key.
[0061] E(Fq): The set of all rational points (including the point O at infinity) of the elliptic curve E on Fq.
[0062] Fq: A finite field containing q elements.
[0063] G: A base point of an elliptic curve whose order is a prime number.
[0064] Hash(): Cryptographic hash function.
[0065] Hv(): A cryptographic hash function with a message digest length of v bits.
[0066] h: cofactor, where h=1.
[00...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More