Indirect access method and system of service system
A business system and access method technology, which is applied to the indirect access method and system field of the business system to achieve the effect of ensuring data security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0022] The following specific examples illustrate the implementation of the present invention. Those familiar with the technology can easily understand other advantages and effects of the present invention from the content disclosed in this specification.
[0023] In the following description, for the purpose of illustration rather than limitation, specific details such as specific system structure, interface, technology, etc. are proposed for a thorough understanding of the present invention. However, it should be clear to those skilled in the art that the present invention can also be implemented in other embodiments without these specific details. In other cases, detailed descriptions of well-known systems, circuits, and methods are omitted to avoid unnecessary details from obstructing the description of the present invention.
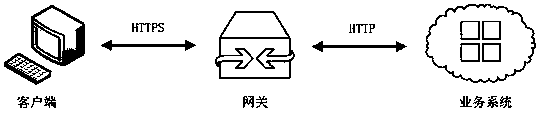
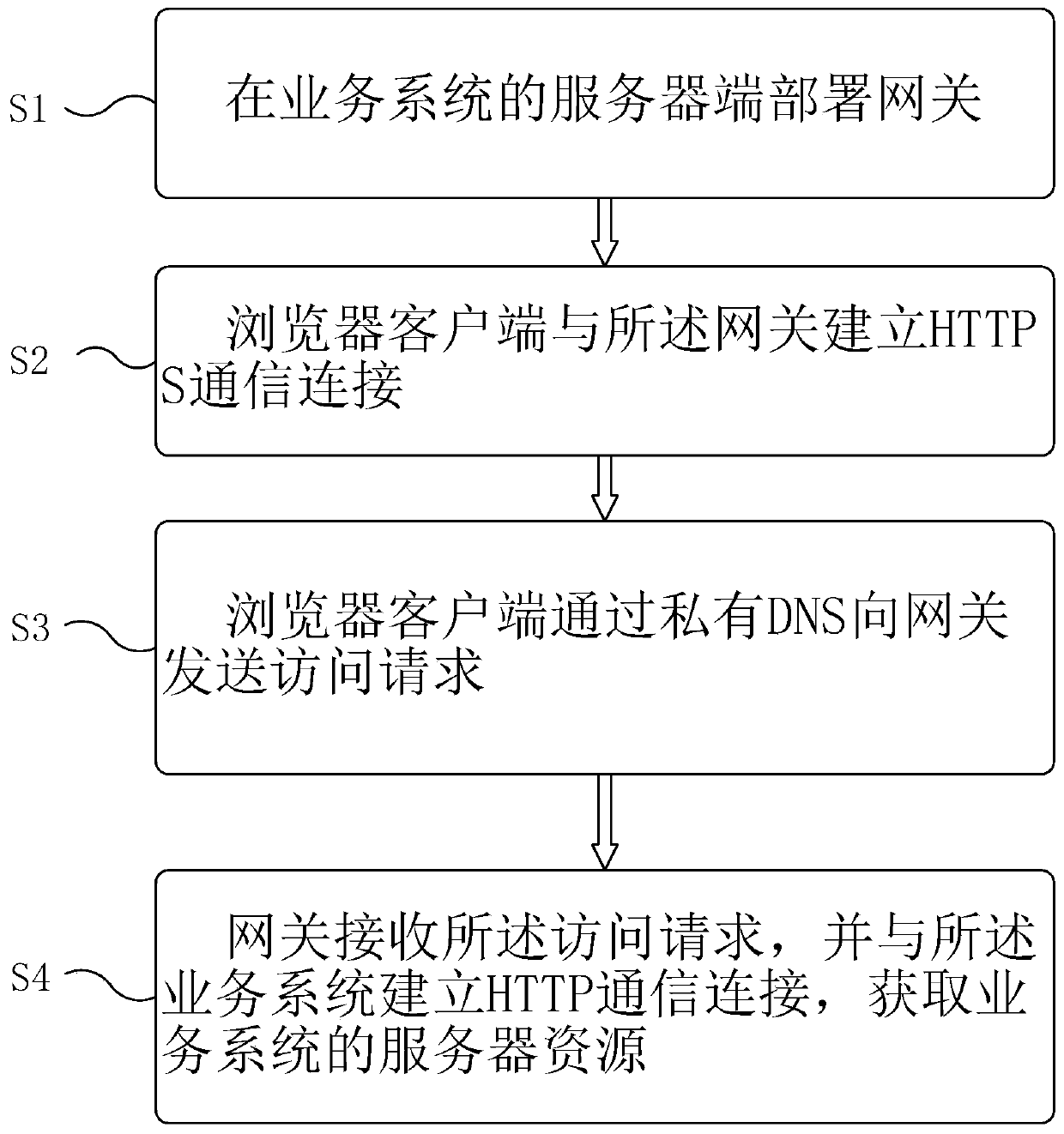
[0024] The embodiment of the present invention provides an indirect access method of a business system, refer to figure 1 , The method includes:
[0025]...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More