js script file vulnerability detection method and system
A script file, vulnerability detection technology, applied in the field of vulnerability detection, can solve problems such as heavy workload and low efficiency, and achieve the effect of ensuring efficiency and effectiveness
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0061] In order to describe the technical content, structural features, achieved goals and effects of the present invention in detail, the following will be described in detail in conjunction with the embodiments and accompanying drawings.
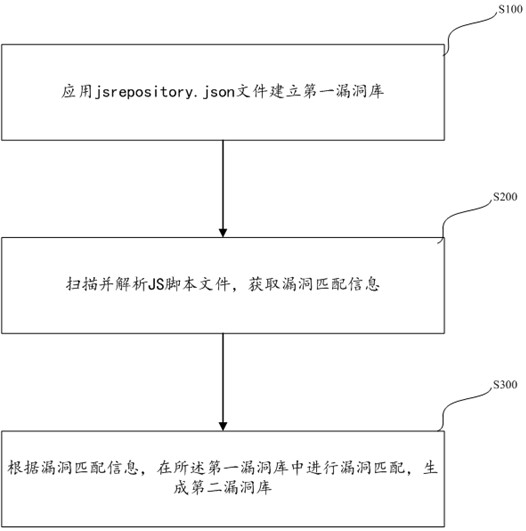
[0062] see figure 1 , figure 1 It is a flow chart of the steps of the JS script file vulnerability detection method in the first embodiment of the present invention. A JS script file vulnerability detection method, comprising the steps of:
[0063] Step S100, using the jsrepository.json file to create a first vulnerability repository.
[0064] Step S200, scanning and parsing the JS script file to obtain vulnerability matching information.
[0065] Step S300, according to the vulnerability matching information, perform vulnerability matching in the first vulnerability database to generate a second vulnerability database.
[0066] Using the JS script file vulnerability detection method provided by the present invention, the functions that ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More