Method and system for realizing reconfiguration of multiple hash algorithms
A hash algorithm and algorithm technology, applied in the field of realizing the reconfiguration of multiple hash algorithms, can solve problems such as poor configurability, insufficient reconfiguration level, and high-speed design of a single hash algorithm.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
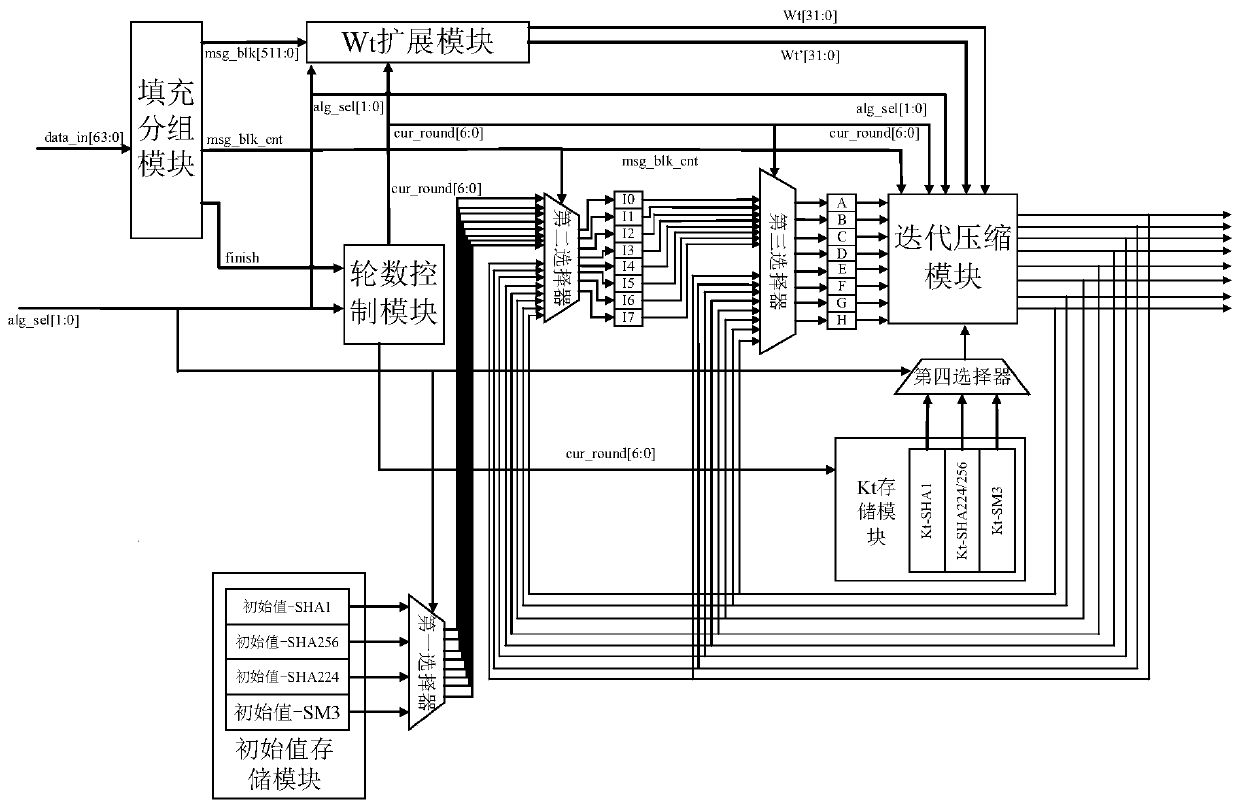
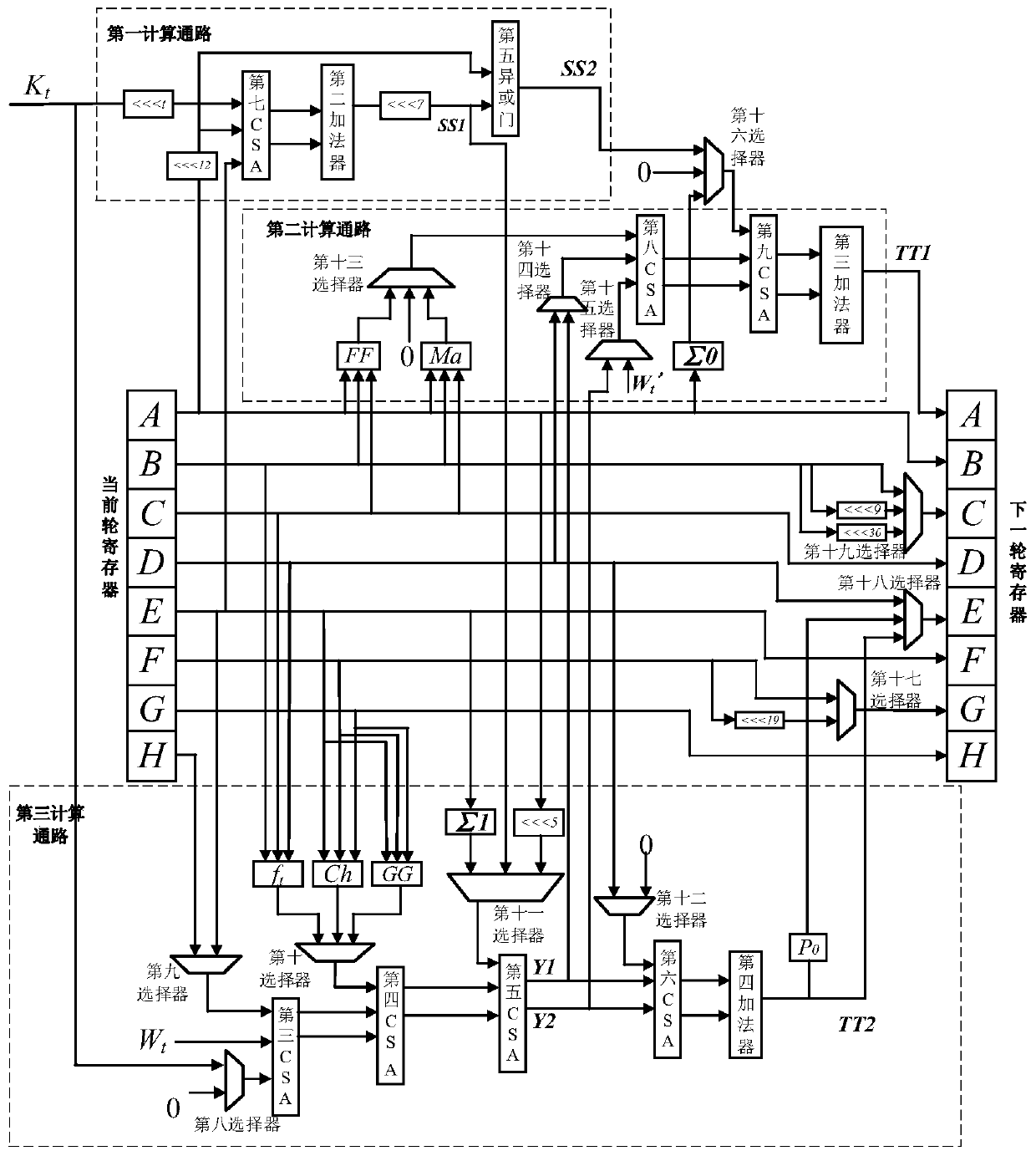
[0102] In order to make the object, technical solution and advantages of the present invention clearer, the present invention will be further described in detail below in conjunction with the accompanying drawings and embodiments. It should be understood that the specific embodiments described here are only used to explain the present invention, not to limit the present invention. In addition, the technical features involved in the various embodiments of the present invention described below can be combined with each other as long as they do not constitute a conflict with each other.
[0103] This embodiment provides a method for realizing the reconfigurability of multiple hash algorithms, including steps:
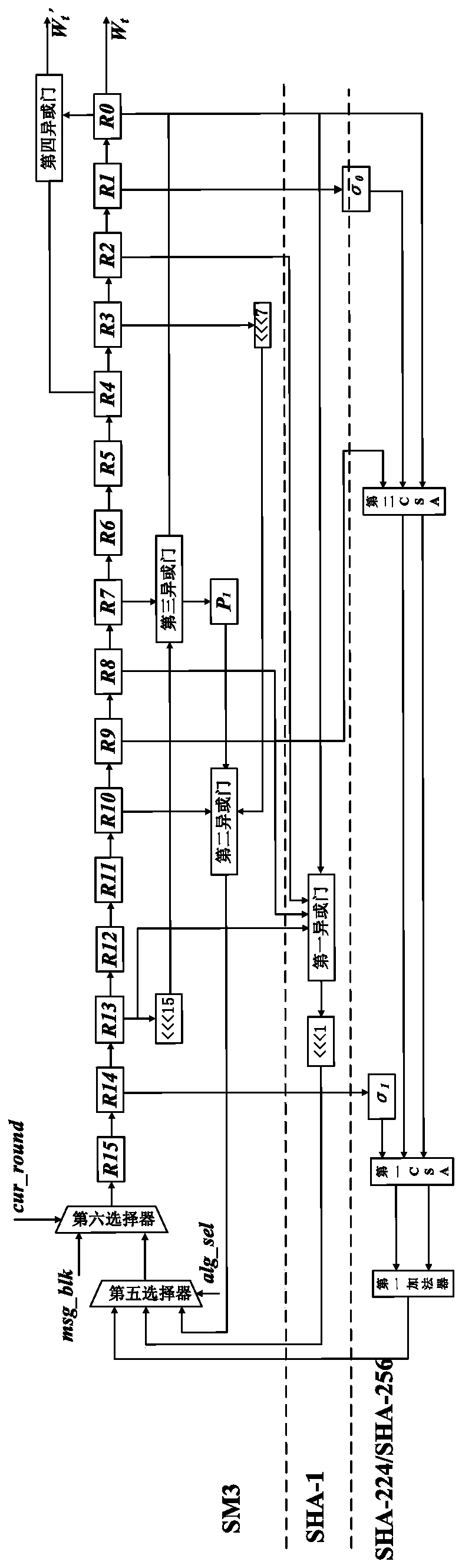
[0104] Receive the data to be authenticated and divide it into multiple 512bit (bit width) message blocks, store the initial values of the four algorithms of SHA-1, SM3, SHA-224 and SHA-256, and store the constant data K required for iterative compression of the four alg...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More