Abnormal behavior recognition system
A technology for identifying systems and behaviors, applied in the field of information security, can solve problems such as non-fixed rules, rigid fixed rules, and high false alarm rate
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0044] abnormal behavior
[0045] The abnormal behavior mentioned in the present invention refers to the operation behavior that does not match the content of the white list, including but not limited to abnormal behavior caused by hacker attacks, abnormal behavior caused by misoperation of internal operation and maintenance personnel, etc.
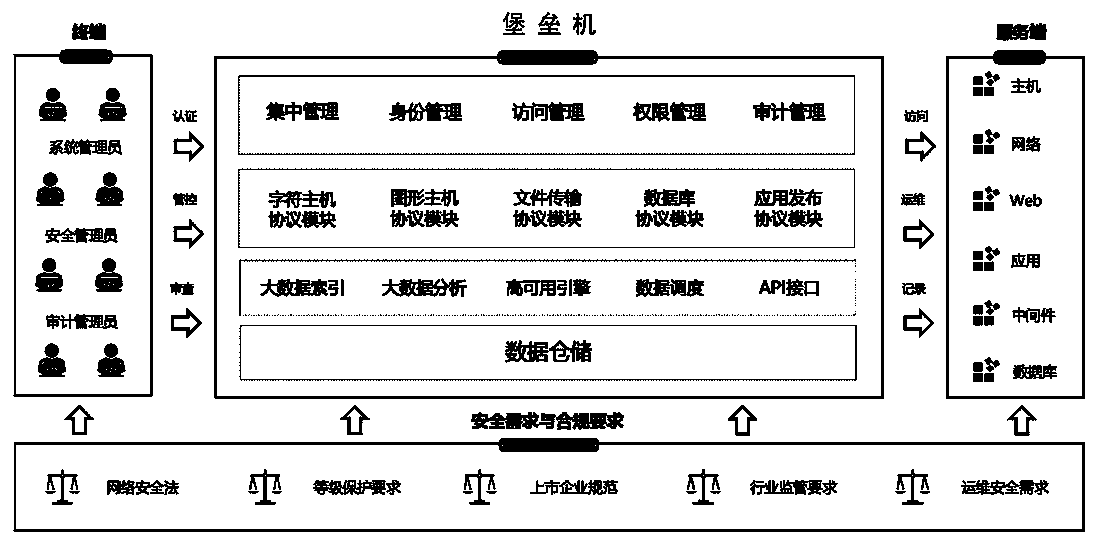
[0046] gateway
[0047] Everyone knows that to walk from one room to another, one must pass through a door. Similarly, sending information from one network to another must pass through a "gateway", which is a gateway. As the name suggests, a gateway is a "gateway" that connects a network to another network, that is, a network gate. The gateway mentioned in the present invention refers to the door to enter the data center.
[0048] workflow engine
[0049] The so-called workflow engine refers to workflow as a part of the application system, and it provides core solutions such as determining information transmission routing and co...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More