Decryption method, device and system, medium and equipment
A device and protocol technology, applied in the field of decryption, which can solve the problems of data theft and the system being easily accessed by lawbreakers
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
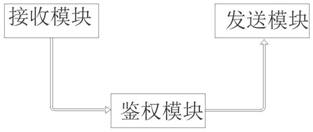
Image
Examples
Embodiment Construction
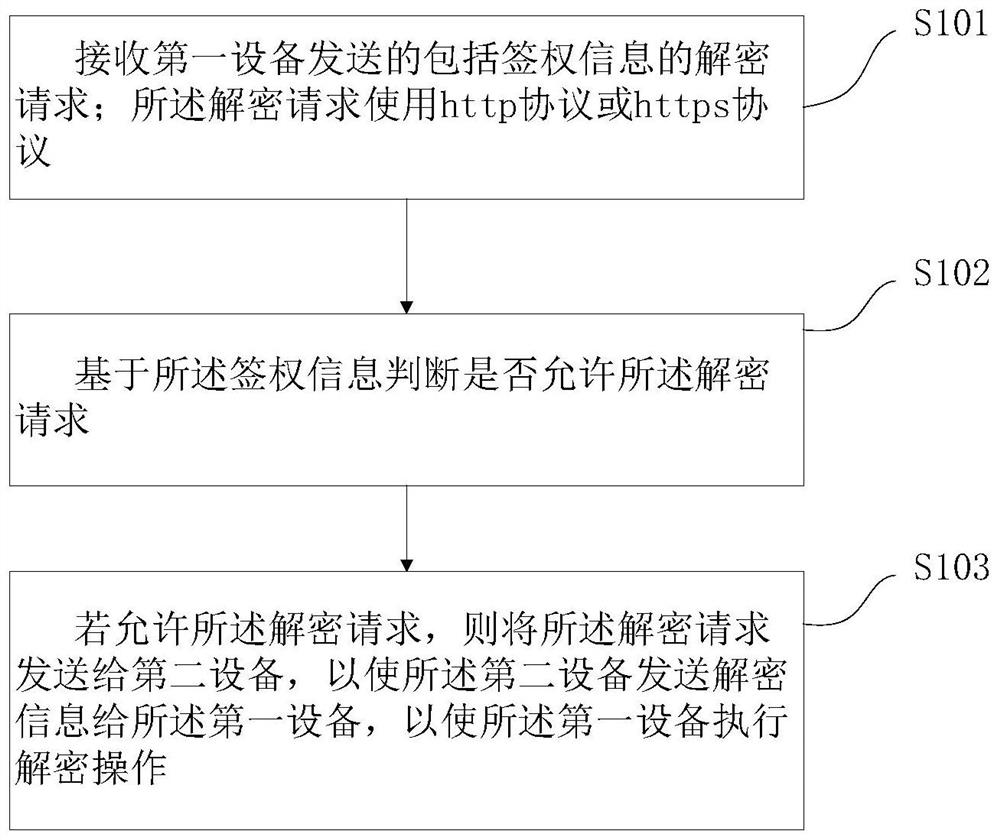
[0050]In order to make the purpose, technical solutions and advantages of the embodiments of this paper clearer, the technical solutions in the embodiments of this paper will be clearly and completely described below in conjunction with the accompanying drawings in the embodiments of this paper. Obviously, the described embodiments are the Some, but not all, embodiments. Based on the embodiments herein, all other embodiments obtained by persons of ordinary skill in the art without making creative efforts fall within the scope of protection herein. It should be noted that, in the case of no conflict, the embodiments in the present application and the features in the embodiments can be combined arbitrarily with each other.
[0051] According to the description in the background technology, when the device is in an unsafe environment, for an attacker who can access the physical server, among the various passwords set by the system, the hard disk password is very important, but fo...
PUM
 Login to view more
Login to view more Abstract
Description
Claims
Application Information
 Login to view more
Login to view more - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap