Role-based complete access control method under intelligent contract
A technology of smart contracts and access control, used in secure communication devices, computer security devices, instruments, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
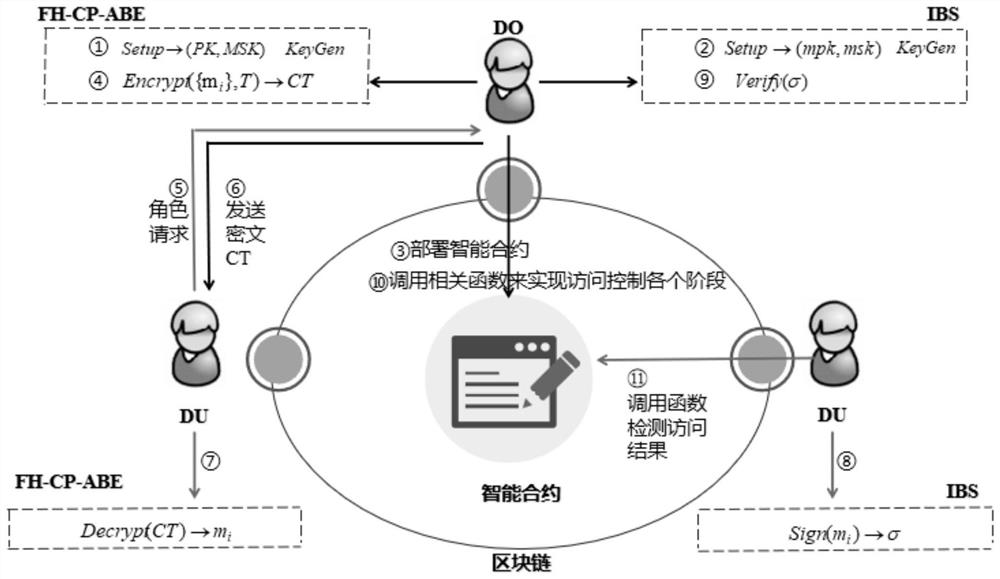
[0052] combined with figure 1 , this embodiment proposes a role-based full access control method under smart contracts, and its implementation process includes:
[0053] ①. Based on the attribute encryption mechanism algorithm FH-CP-ABE of the file hierarchy, the resource owner DO performs the initialization operation.
[0054] The attribute encryption mechanism algorithm FH-CP-ABE based on the file hierarchy is a known algorithm, which consists of four operations: Setup represents the initial establishment of the algorithm, parameter setting, and is executed by a trusted authority authorization center. KeyGen represents a key generation algorithm. According to the generated master key and public key, it is calculated from the user attribute list parameters to generate the user's private key. This operation is performed by a fully trusted authorization center. Encrypt represents an encryption algorithm, which is executed by the resource owner DO. The encryption algorithm real...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More