Attack detection method and device, electronic equipment and storage medium
An attack detection and sample technology, applied in the computer field, can solve the problem of inaccurate and reliable attack identification results, and achieve the effect of accurate and reliable attack detection.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
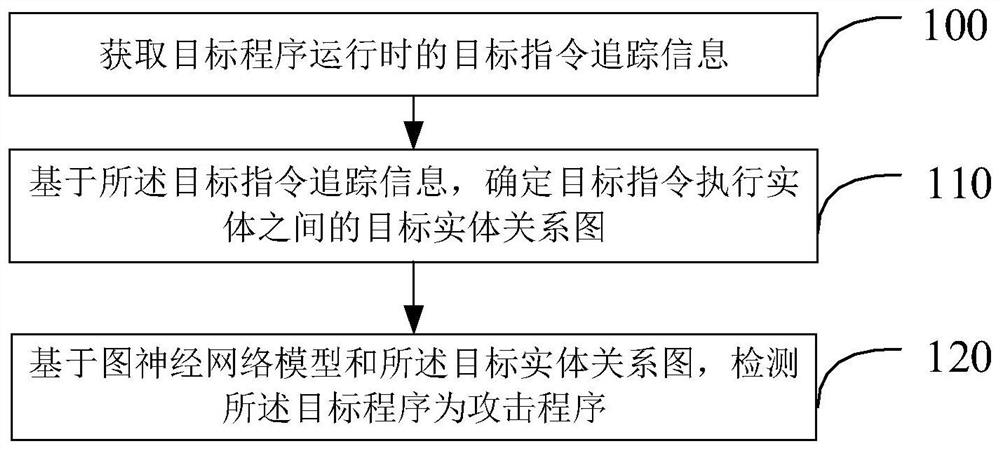
Method used
Image
Examples
Embodiment Construction
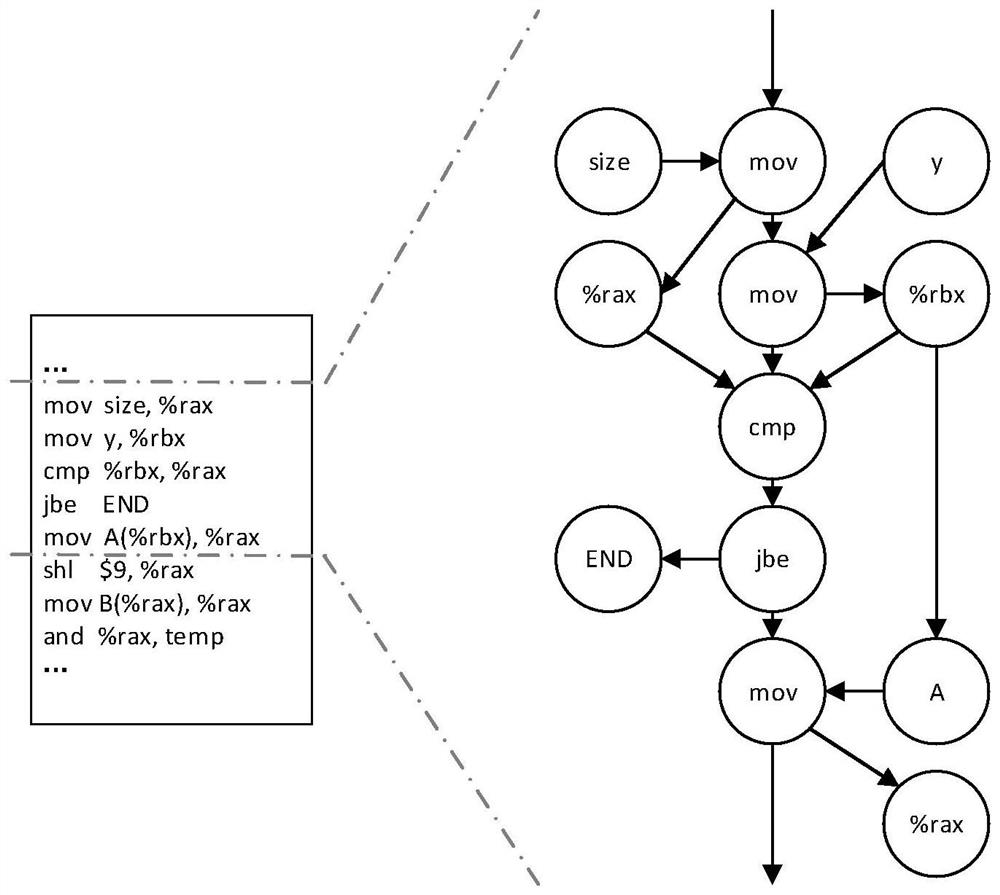
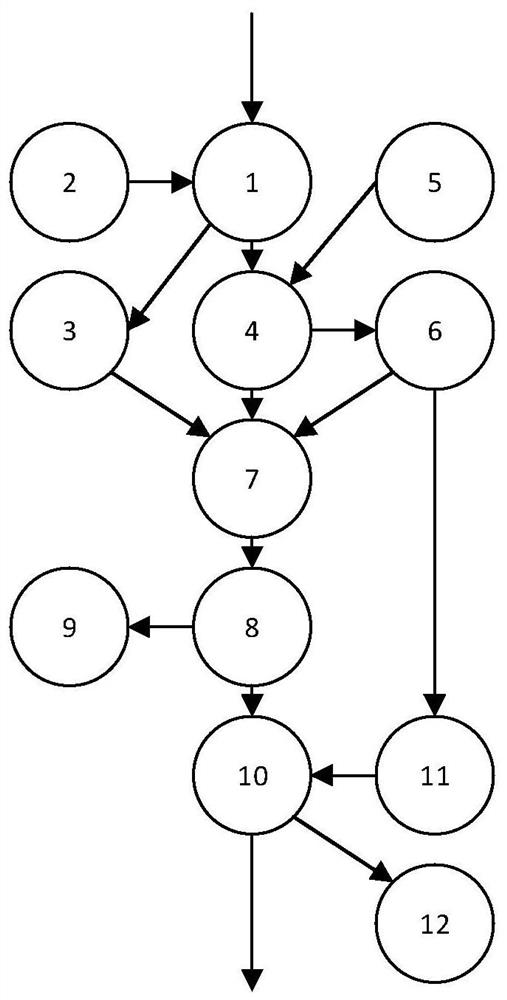
[0042] In order to make the purpose, technical solutions and advantages of the present invention clearer, the technical solutions in the present invention will be clearly and completely described below in conjunction with the accompanying drawings in the present invention. Obviously, the described embodiments are part of the embodiments of the present invention , but not all examples. Based on the embodiments of the present invention, all other embodiments obtained by persons of ordinary skill in the art without creative efforts fall within the protection scope of the present invention.
[0043] Modern computer systems are being attacked by various attack programs and are at great risk.
[0044] Take the transient attack as an example, the attacker of the transient attack usually uses the security loopholes generated by the processor microarchitecture hardware design flaws, such as fuse and ghost, etc., to steal any location in the shared memory with a legal identity and minim...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More