Electronic file processing method and device, storage medium and processor
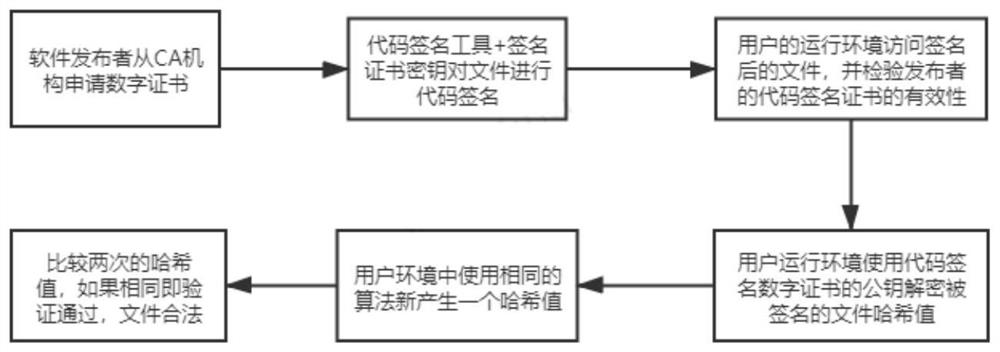
A technology of electronic files and processing methods, which is applied in the fields of electronic digital data processing, computer security devices, instruments, etc., can solve the problems of protecting the integrity and security of software, which cannot be realized, and achieve the effect of protecting integrity and security.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
[0033] According to an embodiment of the present invention, an embodiment of an electronic file processing method is provided. It should be noted that the steps shown in the flow chart of the accompanying drawings can be executed in a computer system such as a set of computer-executable instructions, and, Although a logical order is shown in the flowcharts, in some cases the steps shown or described may be performed in an order different from that shown or described herein.
[0034] figure 2 is a flowchart of an electronic file processing method according to an embodiment of the present invention, such as figure 2 As shown, the method includes the following steps:
[0035] Step S202, obtaining the signature certificate and file content in the target electronic file;
[0036] Step S204, determining the first key of the signature certificate and the first hash value corresponding to the first key;
[0037] Step S206, obtaining the second key and the data to be verified pres...
Embodiment 2
[0085] According to an embodiment of the present invention, an embodiment of an apparatus for implementing the above electronic file processing method is also provided, Image 6 is a schematic structural diagram of an electronic document processing device according to an embodiment of the present invention, such as Image 6 As shown, the above-mentioned electronic document processing device includes: a first acquisition module 60, a determination module 62, a second acquisition module 64, a comparison module 66 and a processing module 68, wherein:
[0086] The first obtaining module 60 is used to obtain the signature certificate and file content in the target electronic file; the determination module 62 is used to determine the first key of the above-mentioned signature certificate and the first hash value corresponding to the above-mentioned first key ; The second obtaining module 64 is used to obtain the second key and the data to be verified preset at the target node positi...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More