Encryption method for internal authentication, smart card, internal authentication method, and card reader
An internal authentication and encryption method technology, applied in the field of smart cards, can solve the problems of plaintext and ciphertext exposure, and achieve the effect of avoiding the risk of malicious decryption and leaking keys, preventing replay attacks, and increasing randomness
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0039] It should be understood that the specific embodiments described here are only used to explain the present invention, not to limit the present invention.
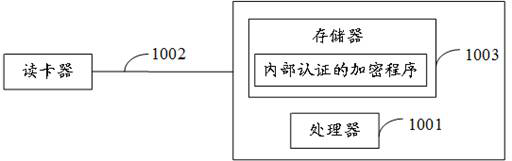
[0040] refer to figure 1 , figure 1 It is a structural schematic diagram of the smart card involved in the solution of the embodiment of the present invention.
[0041] Such as figure 1 As shown, the smart card may include: a processor 1001 , such as a central processing unit (Central Processing Unit, CPU), a communication line 1002 , and a memory 1003 . Wherein, the communication bus 1002 is used to realize connection and communication between the smart card and the card reader. The memory 1003 may be a high-speed random access memory (Random Access Memory, RAM) memory, or a stable non-volatile memory (Non-Volatile Memory, NVM). Optionally, the memory 1003 may also be a storage device independent of the foregoing processor 1001 . The memory 1003 as a storage medium may include an internally authenticated encrypt...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More