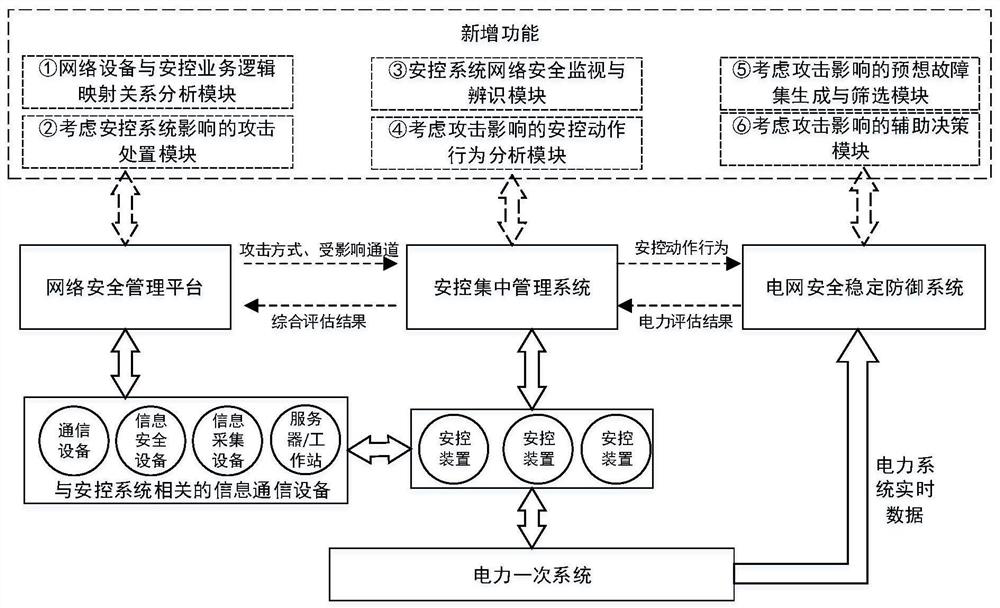
Information and physics collaborative analysis and defense system for hostile attack
A malicious attack and defense system technology, applied in transmission systems, electrical components, etc., can solve problems such as insufficient network security protection capabilities
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
[0057] "Network security management platform", through real-time monitoring, early warning, location traceability, audit analysis, etc. of computers, network equipment, security equipment, etc. in the controlled network space, so as to promote network security management from "static deployment, border monitoring" to " Real-time control, defense in depth" transformation. However, the current "network security management platform" has the following problems: ① It cannot monitor and analyze the power secondary system, such as safety and stability control devices, protection devices, etc., only for conventional computers, databases, network equipment and security equipment, etc. Monitoring and Analysis. ②Risk assessment is qualitative analysis, mostly statistical analysis or a set of assessment system based on expert experience, which cannot quantitatively assess the impact of malicious network attacks on the primary power system. ③ Insufficient closed-loop processing capability...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More