Cross-domain access control method based on block chain
An access control and blockchain technology, applied in the field of information security, can solve problems such as lack of transparency in privacy, and achieve the effect of preventing system abnormalities and secure access control
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0040] The present invention will be further described below in conjunction with the accompanying drawings.
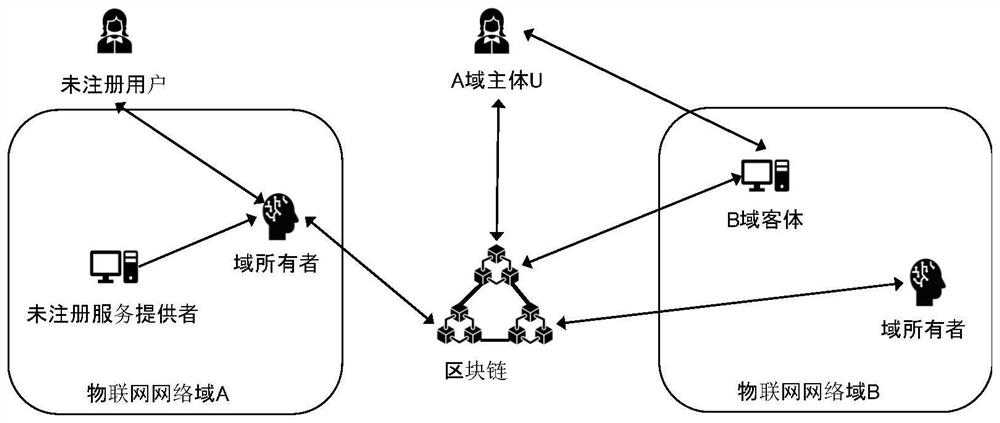
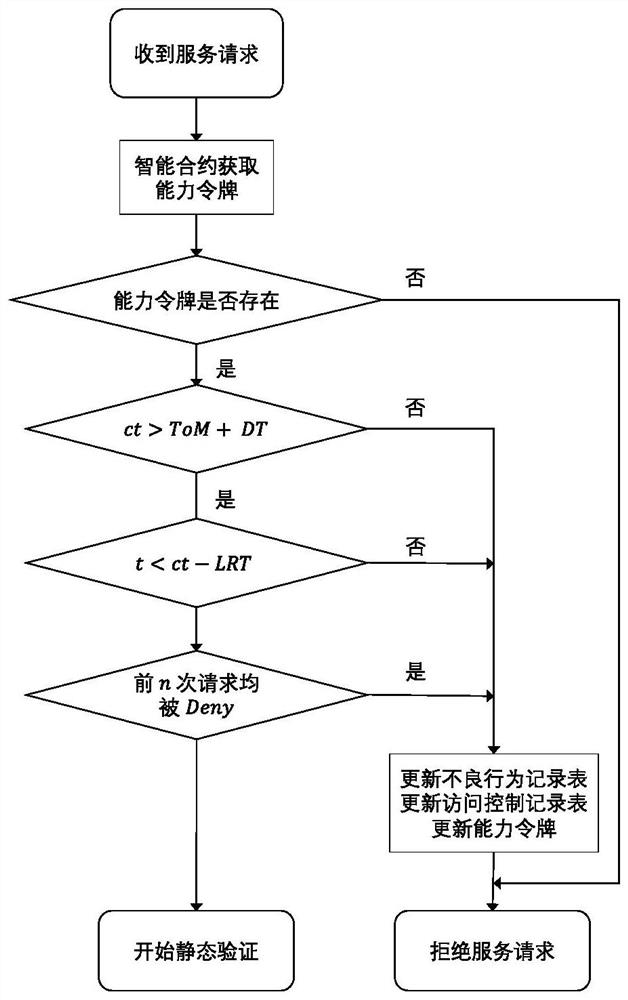
[0041] combine figure 1 , the present invention proposes a blockchain-based cross-domain access control method, including registration of users and service providers, generation of capability tokens, and verification of access rights, mainly including the following steps:
[0042] Step 1: In the registration phase, entities participating in the access control process are divided into subjects and objects. Subjects are entities that request access to services or resources. Objects are usually service providers or resource providers. All entities need to participate in the registration process Access control, generate a unique identification EID according to its own address information, and maintain a configuration file database locally by the domain owner.
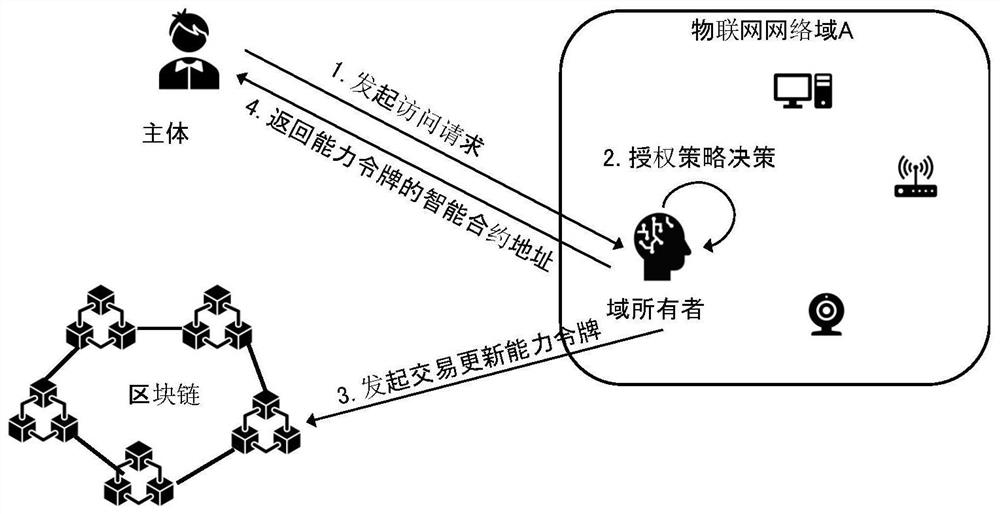
[0043] Step 2: In the capability token generation stage, the registered user as the subject sends a request to t...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More