Verifiable fine-grained access control inner product function encryption method
A technology of access control and encryption method, which is applied in the direction of user identity/authority verification, digital transmission system, and secure communication device, etc., which can solve problems such as vulnerability, achieve security, solve flexible authority control problems, and provide high security Effect
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
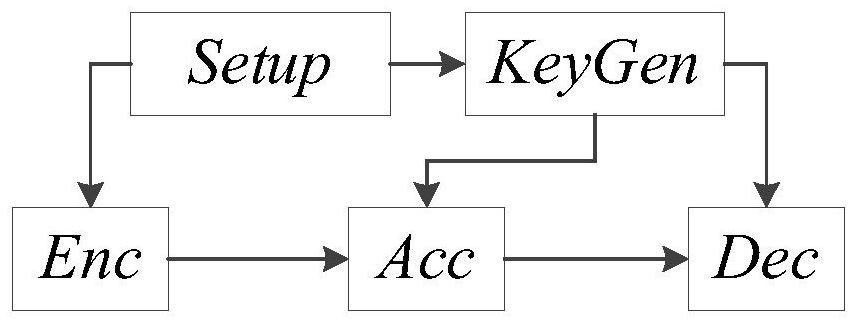
[0031]like figure 1 , figure 2 As shown, a verifiable fine-grained access control inner product function encryption method according to the present invention includes the following steps:
[0032] Step 1. Based on set theory, give the definition of general access structure with hierarchical permissions: according to the attribute set U of the participants user , the logical operation set Θ and the hierarchical permission set R, fused with the power set of the attribute set of the participants Power Sets of Logical Operation Sets 2 Θ and a hierarchical permission set R, defining the Cartesian product:
[0033]
[0034] In this way, an authorized access tree structure space with hierarchical permissions is constructed:
[0035]
[0036] Define the subset Σ∈T of T as a general access structure with hierarchical permissions (also called authorization structure), and d( ) represents the degree of tree nodes;
[0037] Step 2. Based on the defined general access structur...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More