Method for block-encryption of discrete data
A technology for block encryption and discrete data, applied in encryption devices with shift registers/memory, digital transmission systems, usage of multiple keys/algorithms, etc., can solve low encryption rate, high encryption rate, 56-bit encryption Key bit length and other issues, to achieve the effect of increased encryption rate, high anti-decryption resistance, and increased rate
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
example 1
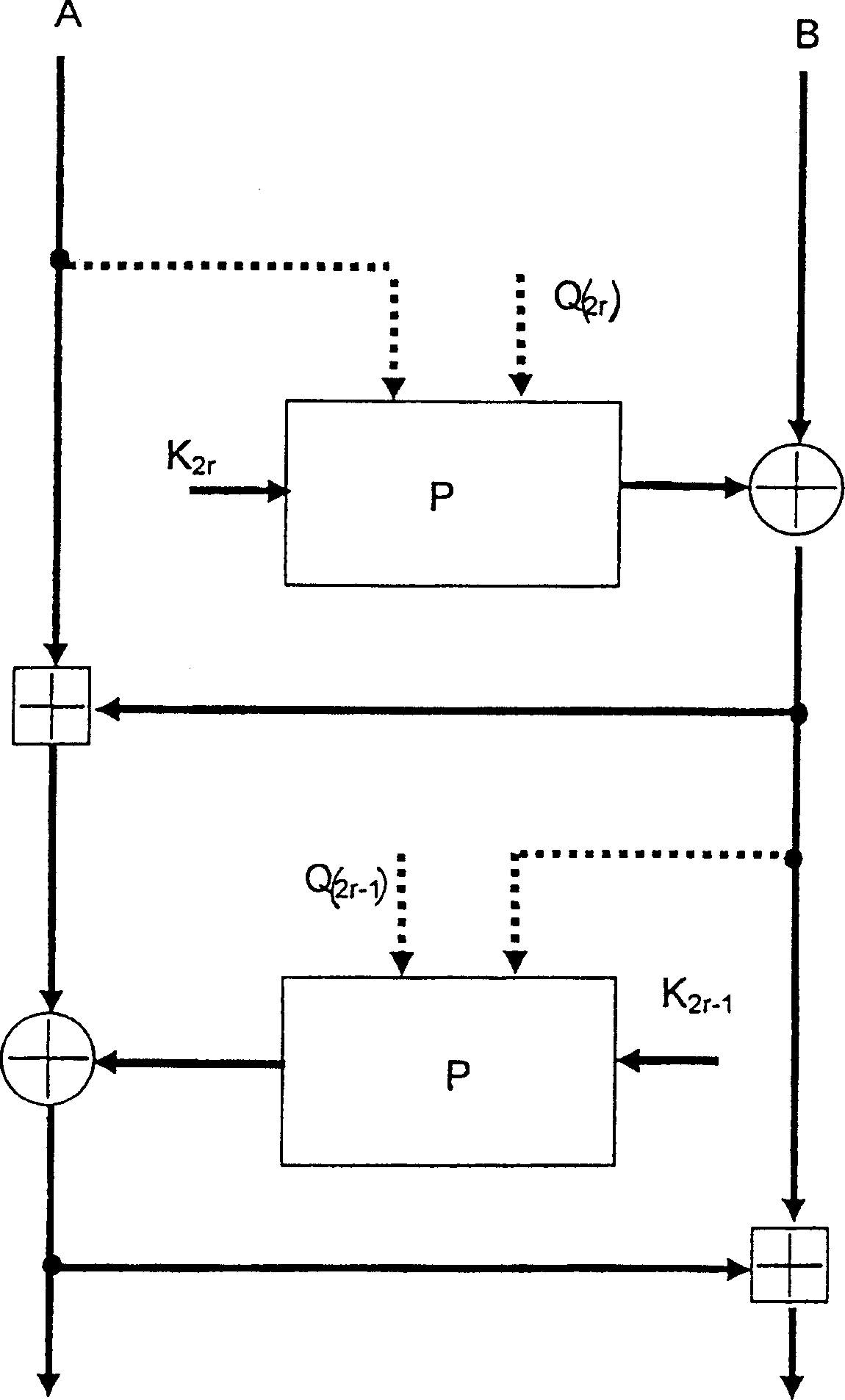
[0040] In this example, the 64-bit data block is encrypted by using a controlled permutation operation as an operation performed on the subkey from one of the transformed data blocks. The generated encryption key is in the form of 16 subkeys K each with a length of 32 bits. 1 , K 2 , K 3 ,...,K 16 . Also no additional subkeys are used. The input data block is decomposed into two 32-bit sub-blocks A and B. The input data block encryption algorithm is as follows:
[0041] 1. Set the encryption round counter r: = 1;
[0042] 2. According to the formula B:=BP A (K 2r ) to transform the sub-block B, where P A (K 2r ) indicates that the subkey K is paired according to the value of subblock A 2r The digit permutation operation performed.
[0043] 3. Transform the sub-block A according to the formula A:=AB
[0044] 4. According to the formula A:=AP B (K 2r-1 ) to transform the sub-block A, where P B (K 2r-1 ) means pairing subkey K according to the value of subbloc...
example 2
[0059]What is used in this example is the cyclic offset operation performed on the subkey according to the transformed subblock. The steps are as follows: First, generate a subkey K in the form of 16 bits with a length of 32 bits 1 , K 2 ,...,K 32 encryption key; then decompose a 64-bit input data block into two 32-bit sub-blocks A and B; then encrypt according to the following algorithm:
[0060] 1. Set the round counter value r=1
[0061] 2. According to formula B:=B(K 2r 2r <<
[0062] 3. Transform the sub-block A according to the formula A:=AB, where "" means modulo 2 32 Addition operation.
[0063] 4. According to the formula A:=A(K 2r-1 2r-1 2r-1 Performs a circular shift operation that shifts B digits to the left.
[0064] 5. Sub-block B is transformed according to the formula B:=BA.
[0065] 6. If r≠16, add one to the counter r:=r+1, and jump to step 2, otherw...
example 3
[0068] What is used in this example is the replacement operation performed on the subkey according to the subblock to be transformed. For this example, data block P 1 and P 2 Indicates the operation data block on which the replacement operation is performed according to an appropriate number of sub-blocks. Wherein the substitution operation represents the replacement of the binary signal value on the input of the operation data block P with another binary value (set by the output of the operation data block) (which is obtained by referring to a substitution table and according to the input of the data block P value to perform the selected) operation. Two forms of substitution operations can be implemented as follows:
[0069] (1) replace an n-bit input binary vector with an n-bit output binary vector, whereby different output binary vectors correspond to different input binary vectors;
[0070] (2) An m-bit binary vector is replaced by an n-bit output binary vector, where ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More