Method for distinguishing baleful program behavior
A program and behavioral technology, applied in the field of attack protection and computer virus, can solve problems such as ports and protocols cannot be set, virus or hacker intrusion, affecting the normal operation of the network, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
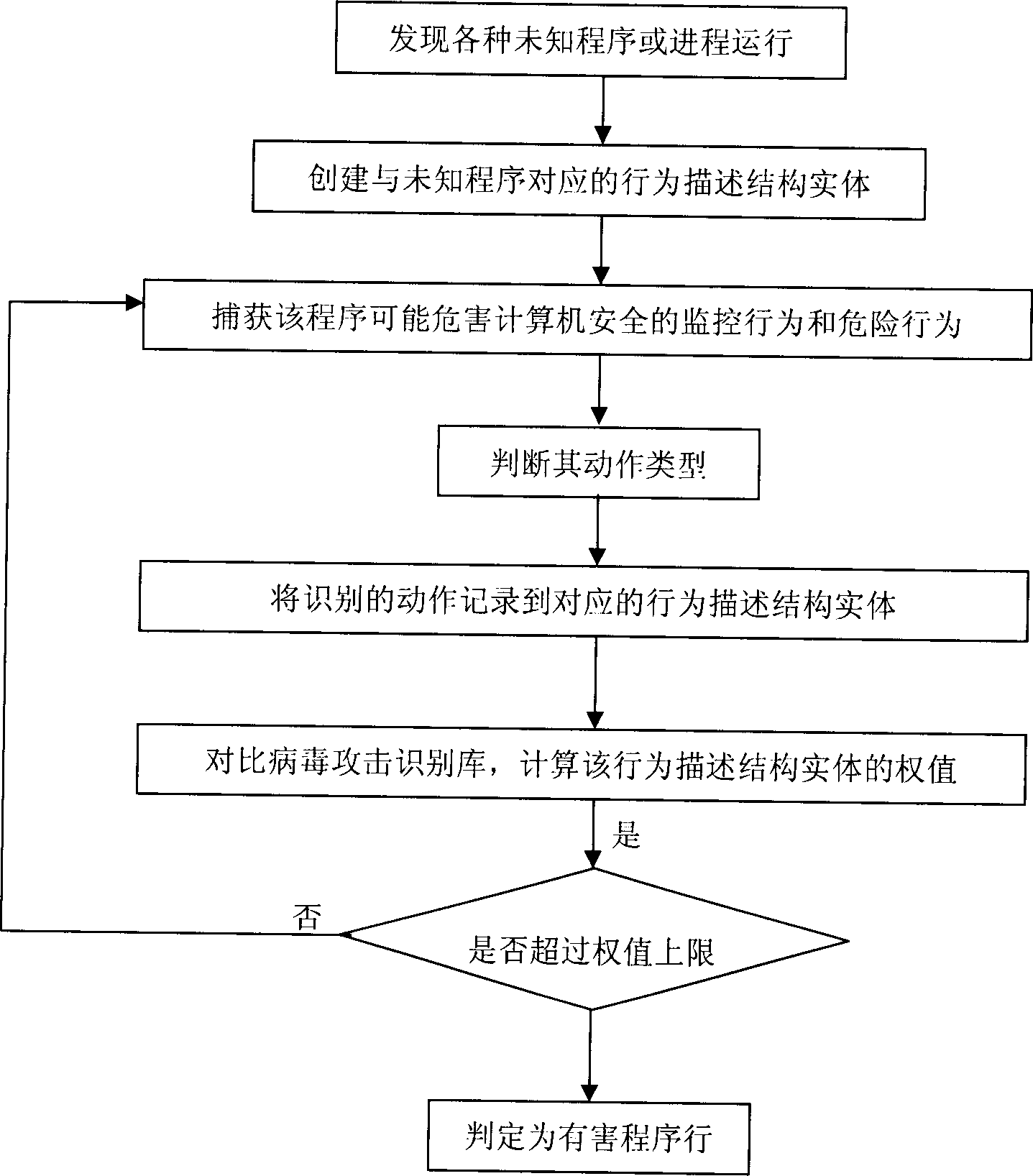
[0056] Specific embodiments of the present invention will be described in detail below in conjunction with the accompanying drawings.
[0057] The method for distinguishing harmful program behaviors of the present invention is based on a virus attack recognition rule base, which records the attack behavior characteristics of various viruses, Trojan horses and harmful programs, each record corresponds to a type of virus, and each A virus-like virus corresponds to an action set, which includes a series of actions and specific associations among them.
[0058] The method for distinguishing harmful program behaviors of the present invention includes the following steps:
[0059] 1.1) Monitor and record the actions of unknown programs;
[0060] 1.2) comparing the recorded action behavior of the program with the virus attack identification rule base as a whole;
[0061] 1.3) Distinguish harmful program behaviors according to the comparison results; if yes, alarm the user or preven...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More