Depth-first attack drawing generating method
A depth-first, attack graph technology, applied in the field of network attack sequence identification technology, can solve the problems of network state explosion, increase the scale of attack graph, and difficulty in attack graph analysis, and achieve the effect of reducing scale
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
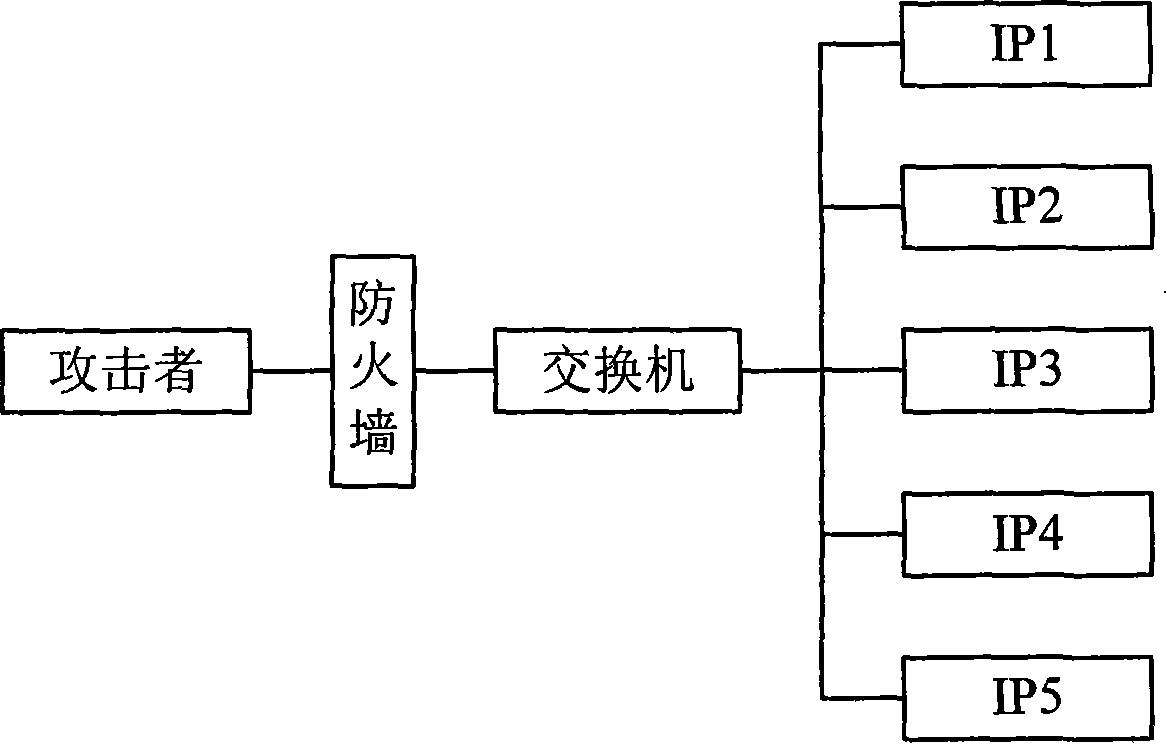
[0029] The present invention is described in more detail below in conjunction with accompanying drawing example:
[0030] In order to realize the purpose of the present invention, the present invention provides a series of definitions at first:
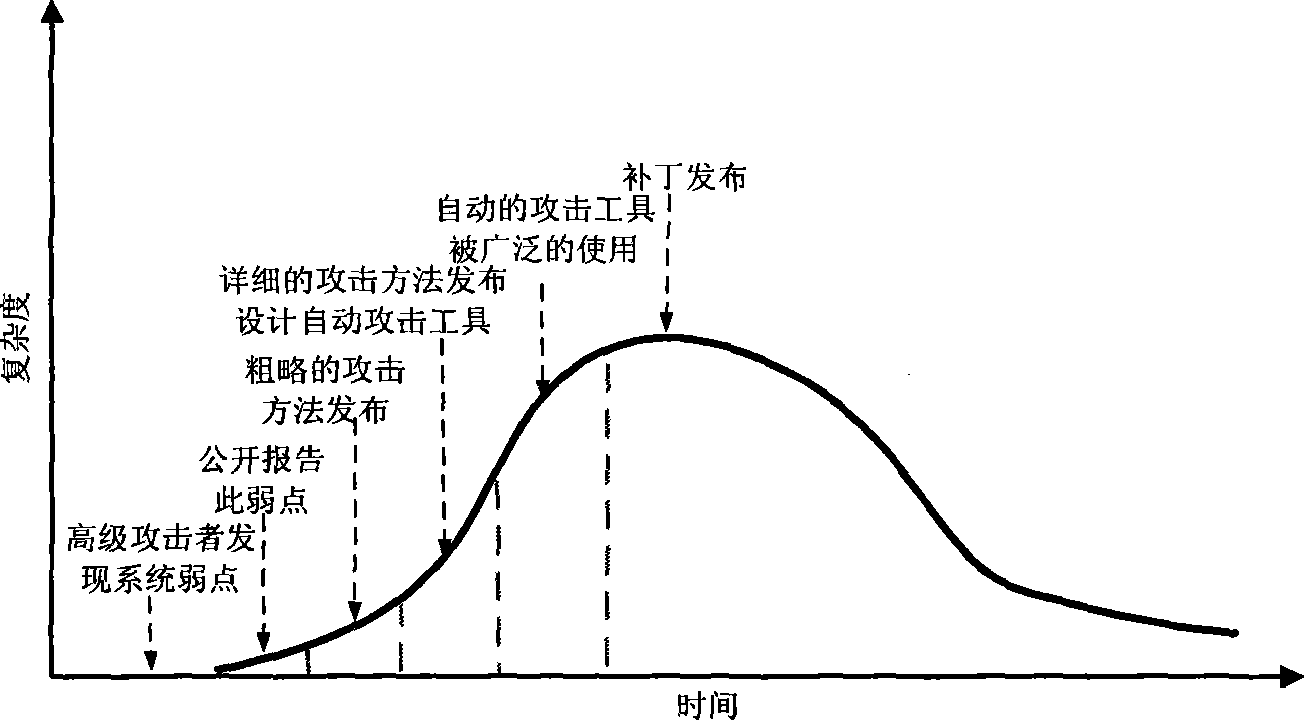
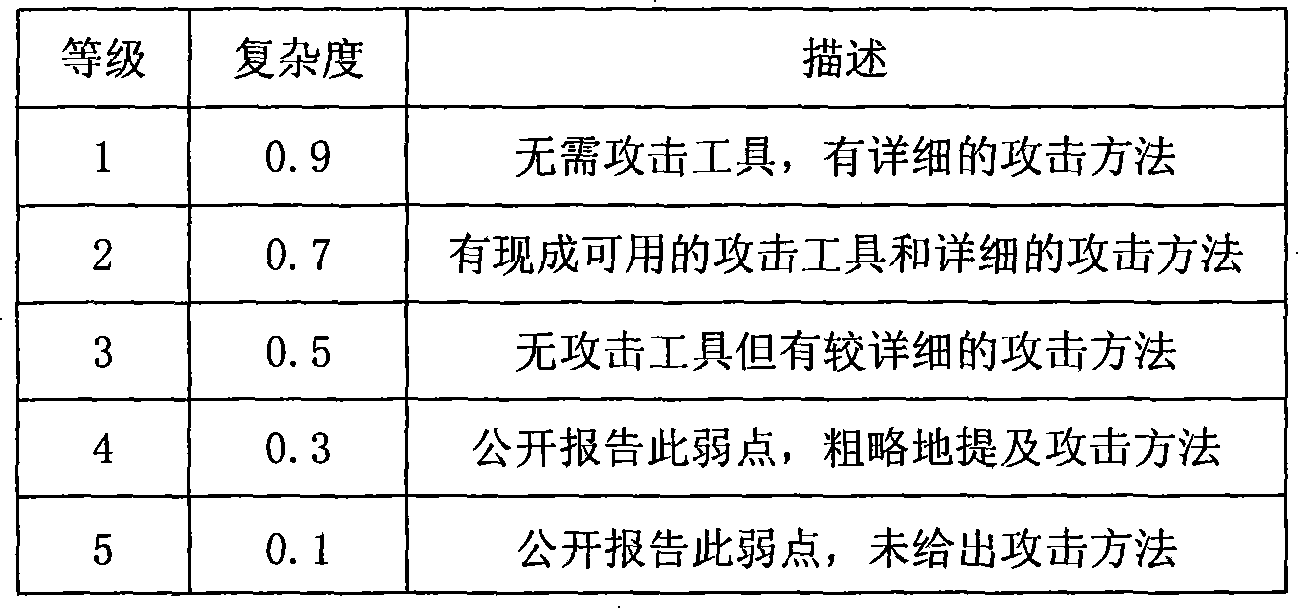
[0031] Definition 1 (Attack Complexity). The attack complexity of a weakness is a measure of how easy it is for an attacker to successfully exploit that weakness.
[0032] The attack complexity of a vulnerability is affected by many factors, such as attack tools, attack time, and attacker experience. The calculation of the attack complexity of the weakness is essentially to establish a mapping from the high-dimensional attribute space to the low-dimensional attribute space. Through the investigation and statistics of a large number of security incidents, researchers found that there is a mapping relationship between the discovery and utilization cycle of vulnerabilities and the complexity of vulnerability attacks. This mapping relati...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More