Private data guard method in sequential mode mining
A sequential pattern mining and privacy data technology, applied in digital data protection, electronic digital data processing, special data processing applications, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
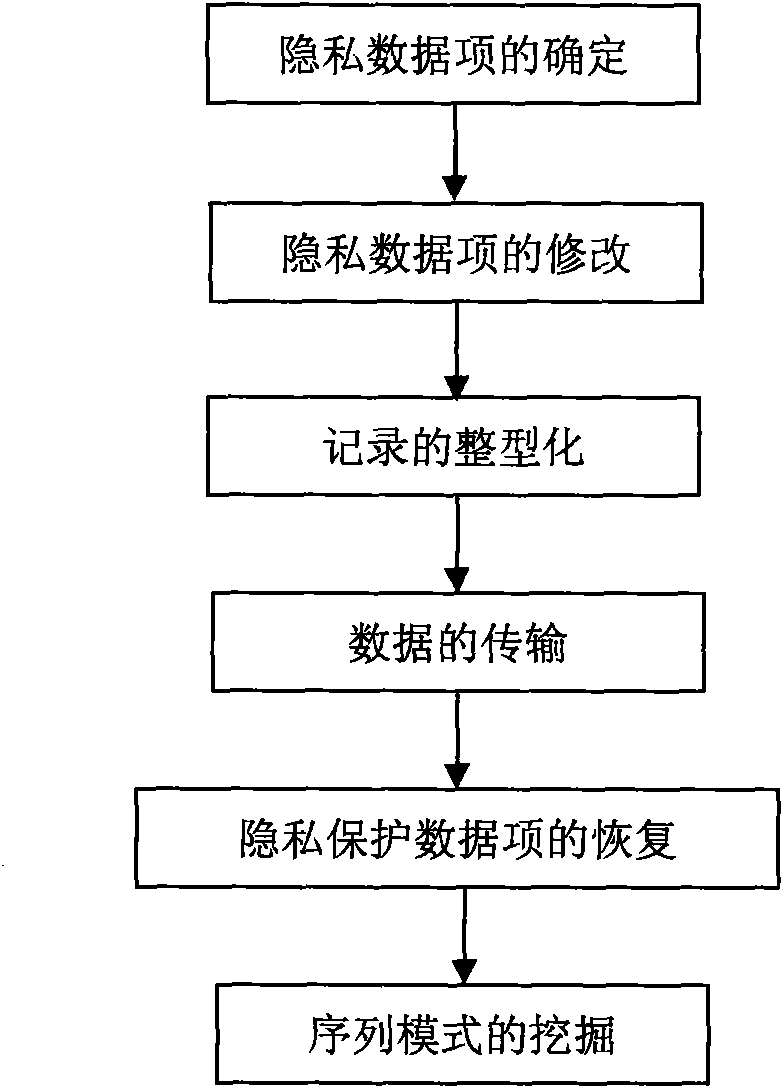
[0043] Such as figure 1 As shown, a sequential pattern mining privacy data protection method includes the steps of determining private data items, modifying private data items, shaping records, transmitting and restoring data, and mining sequential patterns.
[0044] The modification steps of the privacy data items include the following steps:
[0045] (1) Randomly generate two numbers b 1 and b 2 .
[0046] (2) Grouping of records, each group corresponds to an integer a i .
[0047] (3)a i assignment.
[0048] (4)a i Modifications.
[0049] Integrating records, transferring data and restoring steps include the following steps:
[0050] (1) Express each record in the transaction database with a corresponding binary number.
[0051] (2) Transmission of binary numbers.
[0052] (3) according to b 1 and b 2 , restore a i .
[0053] (4) According to the recovered a i Value modifies received binary transactions to the database.
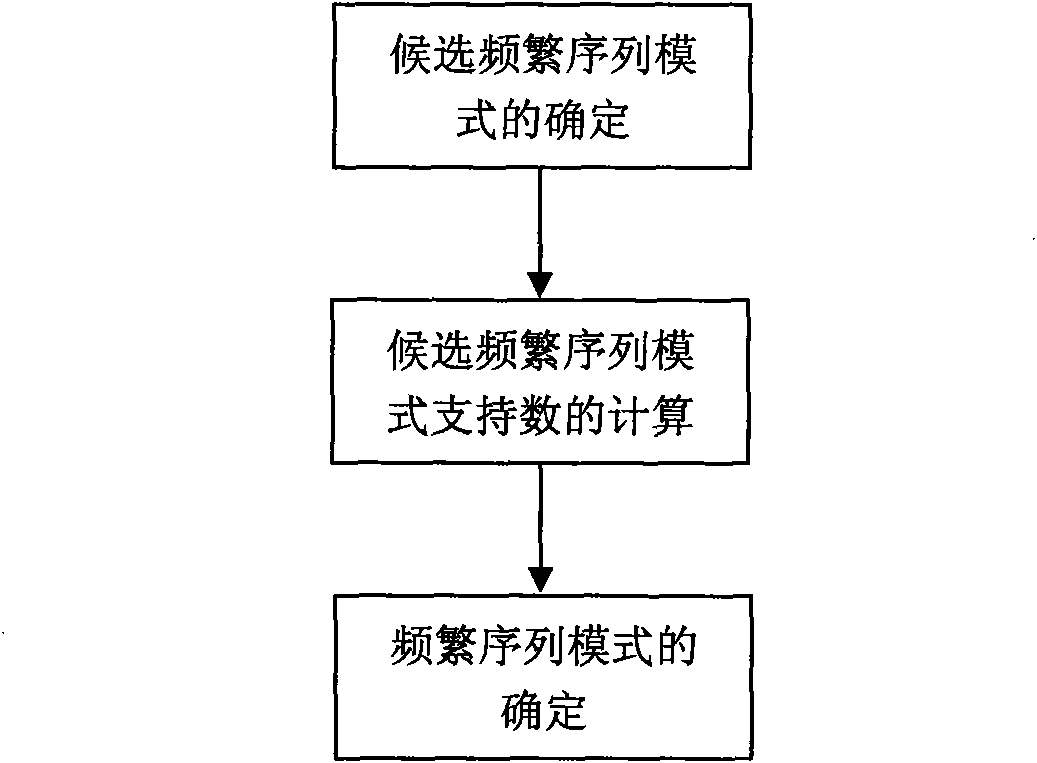
[0054] The sequential pattern minin...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More