Closed loop type information system security class assessment tool
An information system and security level technology, applied in the field of level evaluation tools
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0025] In order to make the technical means, creative features, goals and effects achieved by the present invention easy to understand, the present invention will be further described below in conjunction with specific illustrations.
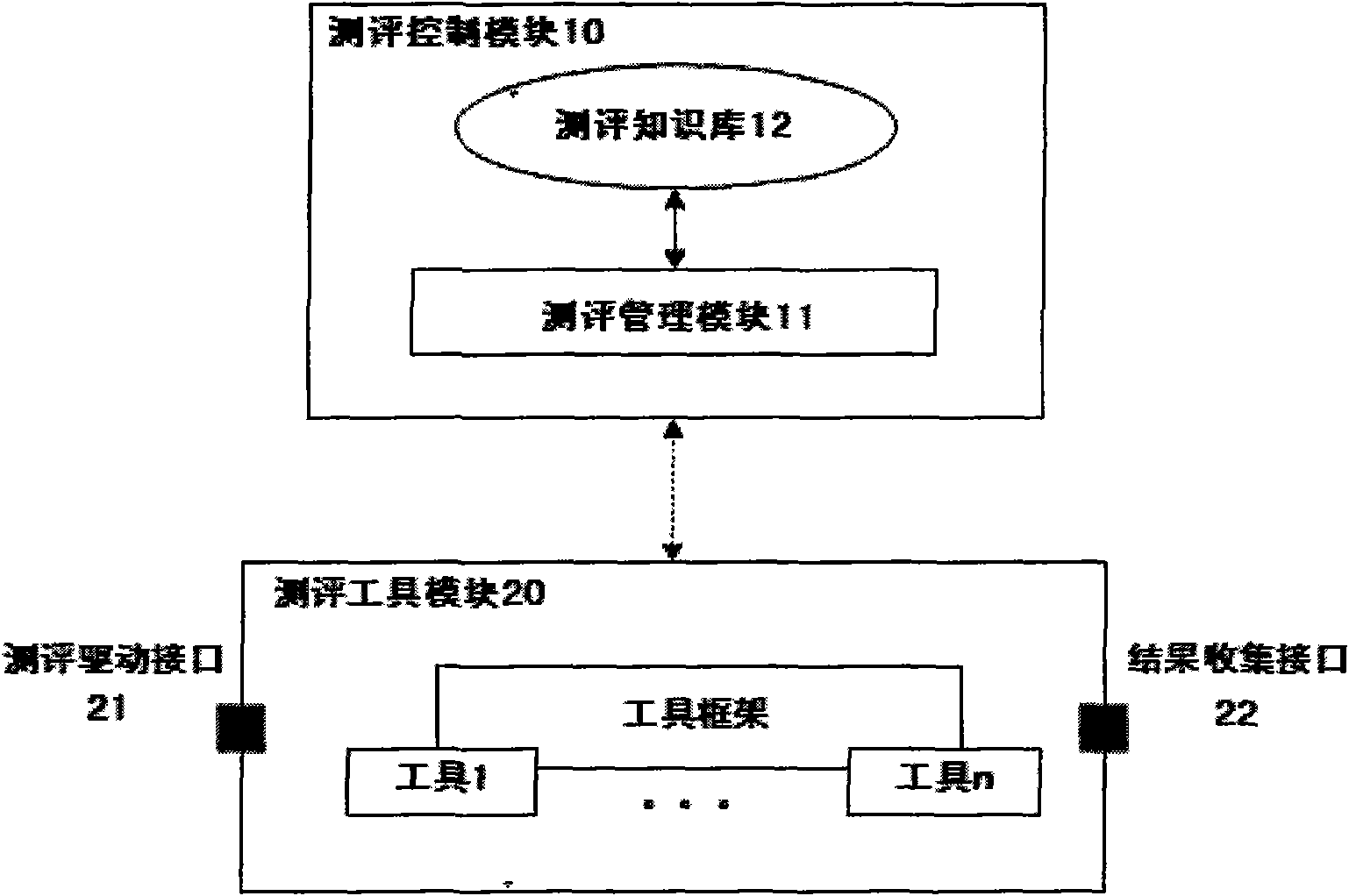
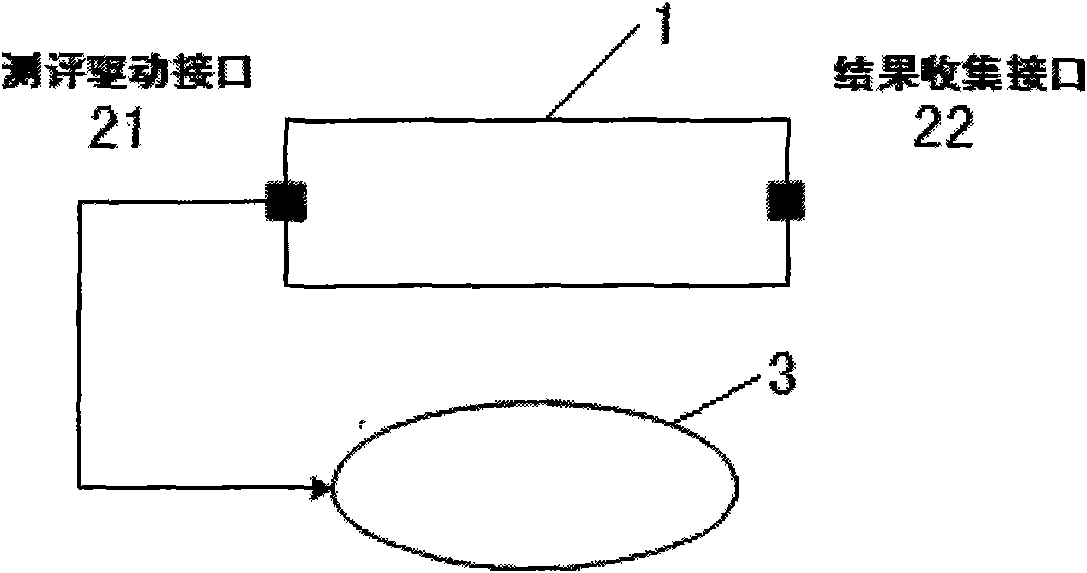
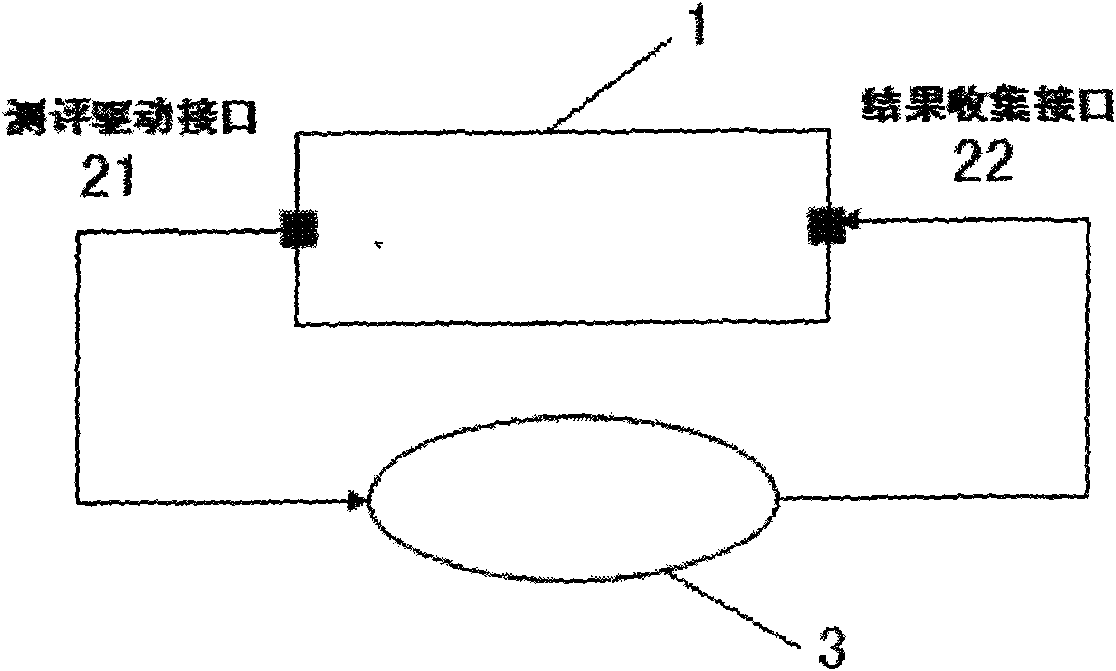
[0026] Such as figure 1 As shown, a closed-loop information system security level evaluation tool 1 includes: an evaluation control module 10 and an evaluation tool module 20; the evaluation control module 10 includes an evaluation management module 11 and an evaluation knowledge base 12; the evaluation tool module 20 is provided with an evaluation driver interface 21 and a result collection interface 22 , and the evaluation tool module 20 is connected to the information system 3 under test through the evaluation driver interface 21 and the result collection interface 22 .
[0027] The evaluation control module 10 is an industrial computer system based on the X86 architecture, and operates the evaluation management module 11 and the evaluation k...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More